-
Products
- Network Security
- Threat Protection
- Secure Access Service Edge (SASE)
- Managed XDR
- Endpoint Security
- Email Security
- Secure Access
-
Gen 7 Firewalls
SonicWall's Gen 7 platform-ready firewalls offer performance with stability and superior threat protection — all at an industry-leading TCO.
Read More
-
Solutions
- Industries
- Use Cases
-
Widgets
-
Content WidgetFederal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
-
Image Widget

-
-
Partners
- SonicWall Partners
- Partner Resources
-
Widgets
-
Content WidgetPartner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
-
Image Widget

-
-
Support
- Support
- Resources
- Capture Labs
-
Widgets
-
Content WidgetSupport Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
-
Image Widget

-
- Company
- Contact Us
SonicWall NSv support on Nutanix



Description
The document provides use cases scenarios to be executed for SonicWall NSv appliance on Nutanix Platform. Together, SonicWall and Nutanix deliver superior security, simplicity, scalability and performance to enterprise hybrid and multi-cloud platform operations.
 NOTE: For more information on partnership between SonicWall and Nutanix, please refer: https://www.nutanix.com/partners/technology-alliances/sonicwall
NOTE: For more information on partnership between SonicWall and Nutanix, please refer: https://www.nutanix.com/partners/technology-alliances/sonicwall
Resolution
Nutanix software pre-requisites
AHV Cluster should be running the below AOS / AHV and PC versions.
- AOS Version: 5.15.x and above LTS release
- AHV Version: AHV version bundled with AOS
- Prism Central (PC) version: 5.15.x compatible with AOS version
- Nutanix AHV cluster registered to PC
- SonicWall NSv version should be the latest GA (LTS) release
SonicWall NSv Virtual Firewall Appliances on Nutanix AHV
Nutanix AHV Service Chain
- Flow is a software-defined networking product tightly integrated into Nutanix AHV and Prism. Flow provides rich visualization, automation, and security for VMs running on AHV. Micro-segmentation is a component of Flow networking that simplifies policy management. Using multiple Prism Central categories (logical groups), you can create a powerful distributed firewall that gives administrators an application-centric policy management tool for securing VM traffic.
Refer: https://portal.nutanix.com/#/page/solutions/details?targetId=TN-2094-Flow:TN-2094-Flow
Video: https://www.youtube.com/watch?v=50edygfpBvw&feature=youtu.be - Service chains have to be created using REST API in current AOS releases, as no UI exists for this yet.
Refer KB 5486: https://portal.nutanix.com/#/page/kbs/details?targetId=kA00e000000LIelCAG
AHV Service chaining in inline mode will be applicable for Scenario 3 as mentioned later in the document.
SonicWall NSv Firewall deployment scenarios
Scenario 1: Standalone NSv in L3 (routed) mode
In this mode the NSv firewall is deployed as a single virtual machine with 1 management interface and additional (2 or more) interfaces for data processing. The primary objective is for the firewall to secure north - south traffic. In this mode the NSv firewall will be connected to a WAN interface (non-trusted) and LAN (trusted) networks on separate VLANs. The routing between the VLANs will be handled by the NSv firewall.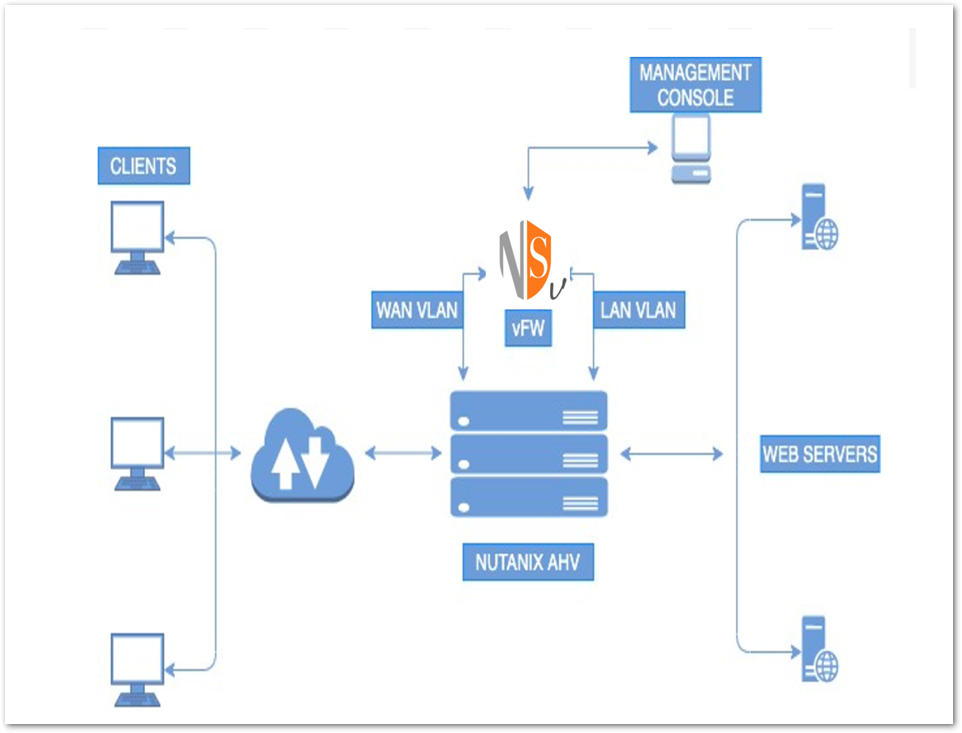
Scenario 2: NSv Firewall in High Availability L3 (routed) mode
In HA mode deploy 2 instances of the NSv firewall on different nodes in AHV cluster. Both the instances should have identical hardware resources (such as CPU cores/memory/network interfaces) assigned to them, and have the set same of licenses/subscriptions.
The vCPU and memory configurations are as per partner products requirements, Nutanix recommends configuring at least 4 vNICs per instance -
1. Management 2. Peer-to-peer HA port 3. WAN VLAN Interface 4. LAN VLAN Interface (Refer below diagram).
The backend web server setup is similar to Scenario 1.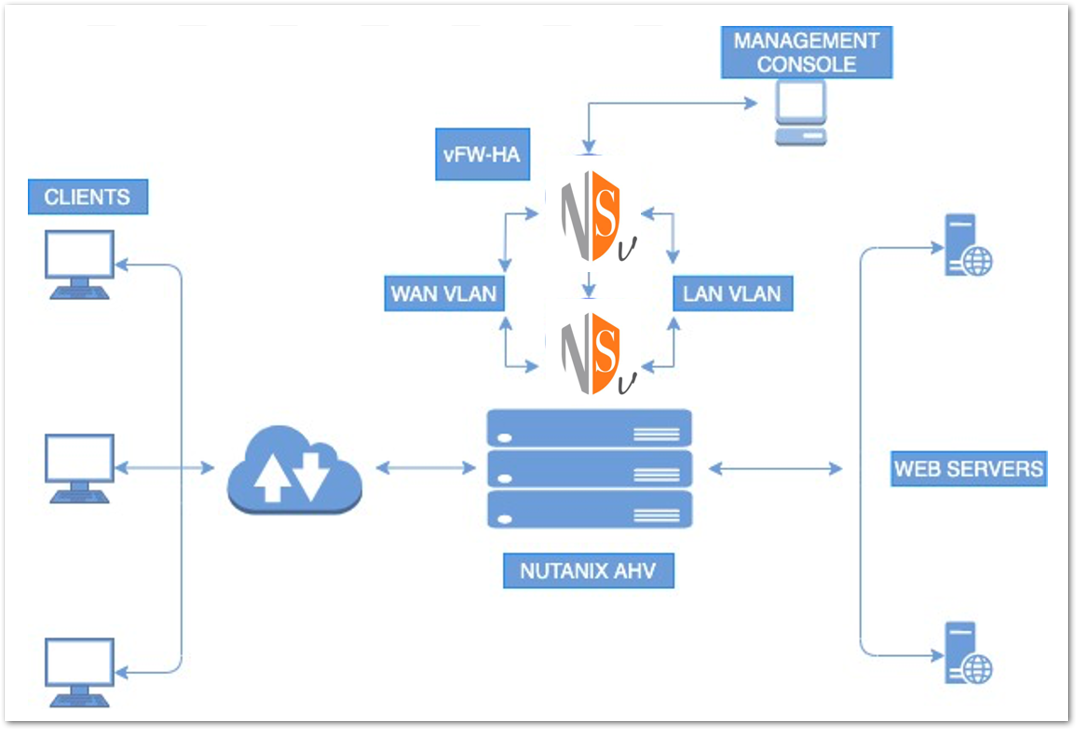
Scenario 3: NSv Firewall in virtual wire mode with Nutanix FLOW
The traffic to and from certain VMs (or networks) on AHV will be directed to a network function SonicWall NSv Firewall that is also running on AHV. Flow policies or entire networks are used to control which traffic is directed to the network function VM.
The overall architecture places a network function VM on every AHV host. Usually these network function VMs are centrally controlled through a vendor specific device (Control or Management VM). Service Chains (or network function chains interchangeably) are created using REST APIs or Calm to create the pipes that allow Flow policies, entire networks, or VMs to direct traffic to the network function VM. A NFV VM such as an IDS or firewall is placed on every host, and controlled by a central management plane as shown below.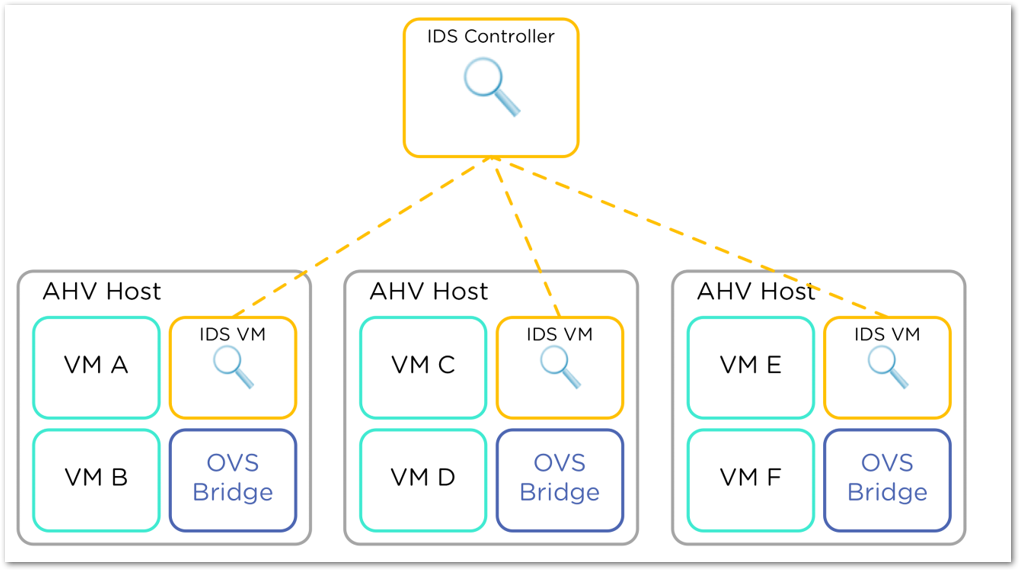
There are two modes of operation for the network function VM. In the first mode (TAP) the network function VM only receives traffic between VMs on a single interface. It does not sit in the path of network traffic and is not able to block or take action that impacts the network traffic. TAP devices would be used for Intrusion Detection or packet capture. If the TAP device is offline, traffic should still flow. This is an example of one AHV host. Every AHV host in the cluster would be configured the same way.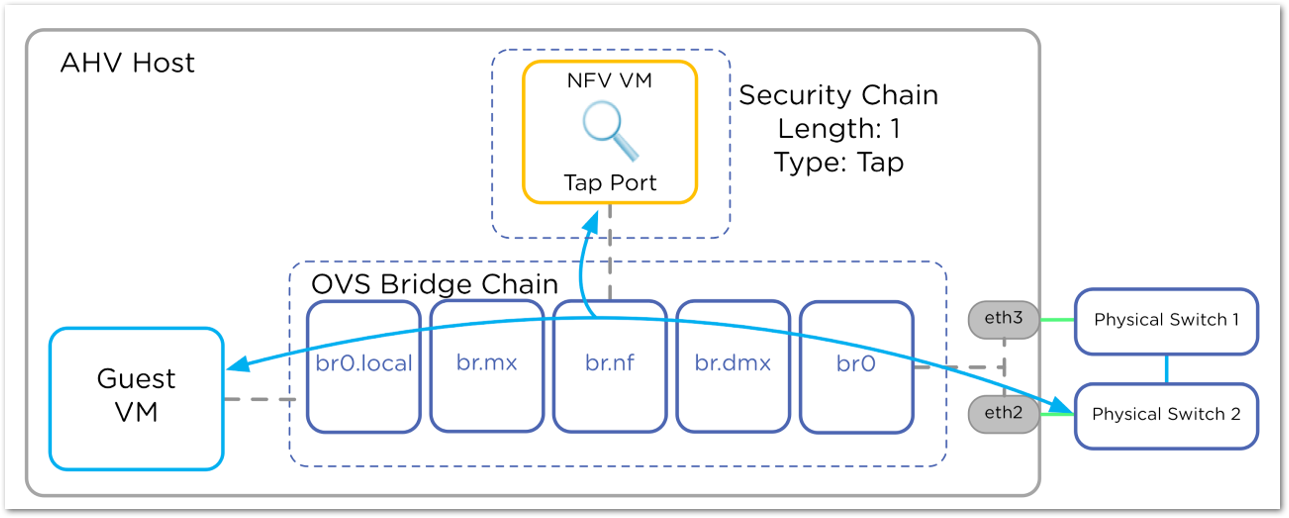
The INLINE mode of operation intercepts traffic and has the ability to block or drop traffic before it is sent along. INLINE network functions have an ingress and egress interface. INLINE applications “fail closed”, meaning that if the INLINE application is powered off or malfunctions, all traffic is blocked by design for security purposes. In the diagram below, the HR VM traffic is redirected through an INLINE firewall VM using Flow. It is also possible to direct the entire HR network, or just the HR VM through INLINE firewall VM. The following configuration will be deployed on every AHV host in the cluster.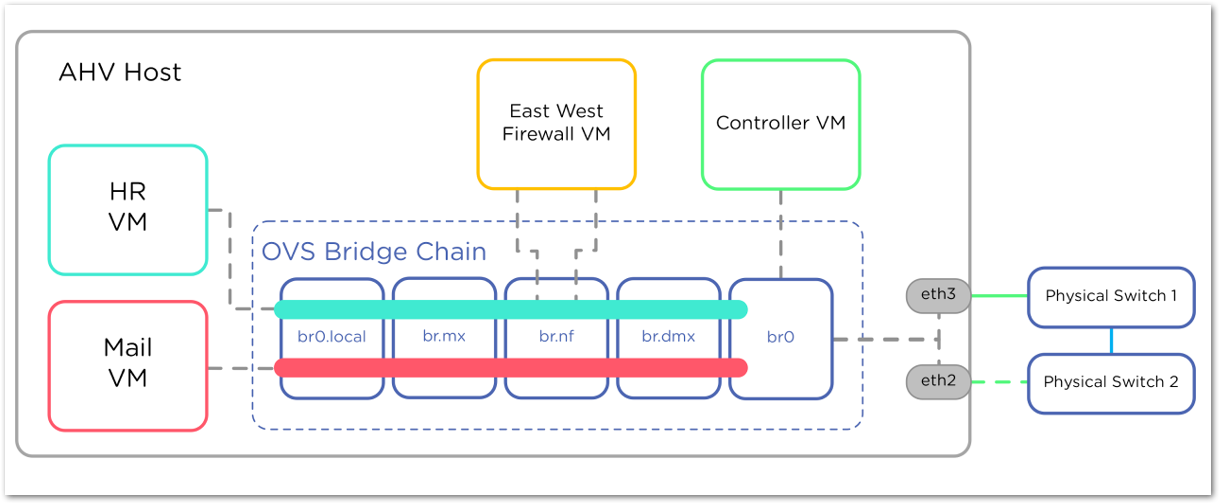
Now that the network function VMs are added to a network function chain, there are a number of ways to direct traffic to the chain. The first method uses Flow security policies to selectively direct specifically defined traffic flows to the function chain. The next method directs an entire AHV network through the chain. The final configuration directs a specific AHV VM through the network function chain.
Related Articles
- Supported SonicWall and 3rd party SFP and SFP+ modules that can be used with SonicWall TZ series
- Certificate Signing Request (CSR) Error: Please enter a valid certificate name for SonicOS 7.1.1
- SNMP OID values that are not supported on Gen7 firewalls



 YES
YES NO
NO