DPI-SSL, FTPS (FTP over SSL/TLS) and GAV



Description
In FTPS, traffic passing through SonicWall will be encrypted and therefore cannot be inspected for malware. For this purpose DPI-SSL can be implemented to enable SonicWall to inspect such traffic in clear text and enforce Security Services.
Resolution
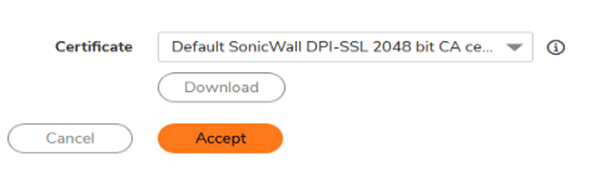
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware. When clients behind the SonicWall access an FTPS server on the WAN side of the SonicWall and outbound FTPS connection needs to be decrypted. Other options like including or excluding users, IP addresses are not enabled in this example but can be enabled as per the deployment. Although none of the Security Services except GAV are enabled, all traffic with standard SSL ports as destination will be re-signed by Client DPI-SSL . Once the certificate is imported into the SonicWall it must be mapped to the private IP address of the FTPS server. Step 4. Configure Gateway Anti-Virus FTP Settings under Protocols need not be checked because the following options will not be enforced: This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware. When clients behind the SonicWall access an FTPS server on the WAN side of the SonicWall and outbound FTPS connection needs to be decrypted. Once the certificate is imported into the SonicWall it must be mapped to the private IP address of the FTPS server. Resolution for SonicOS 7.X
In this example, we use the default SonicWall DPI-SSL CA certificate.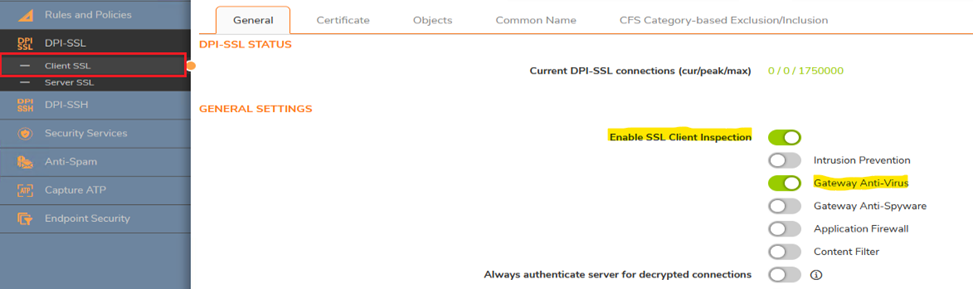
Step 3. Configure Server DPI-SSL
When the FTPS server is behind the SonicWall and clients connect to it from the WAN side of the SonicWall. Before configuring Server DPI-SSL we must import a server certificate into the SonicWall. Although the server certificate could be either from a Windows CA or from a public CA like GoDaddy, it is recommended to use a certificate signed by a public CA. Please refer to these articles on how to obtain a server certificate: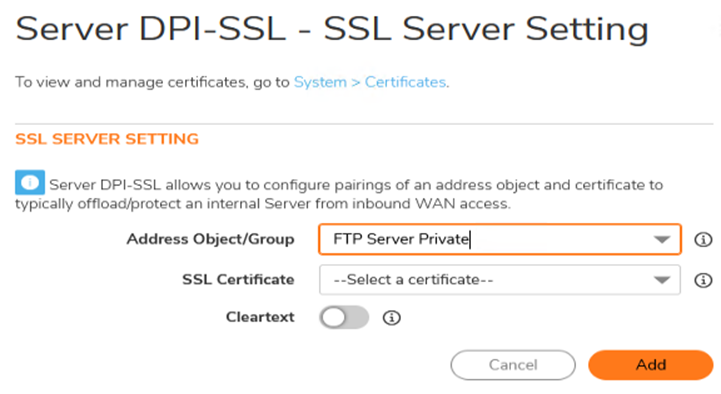
Resolution for SonicOS 6.5
In this example, we use the default SonicWall DPI-SSL CA certificate.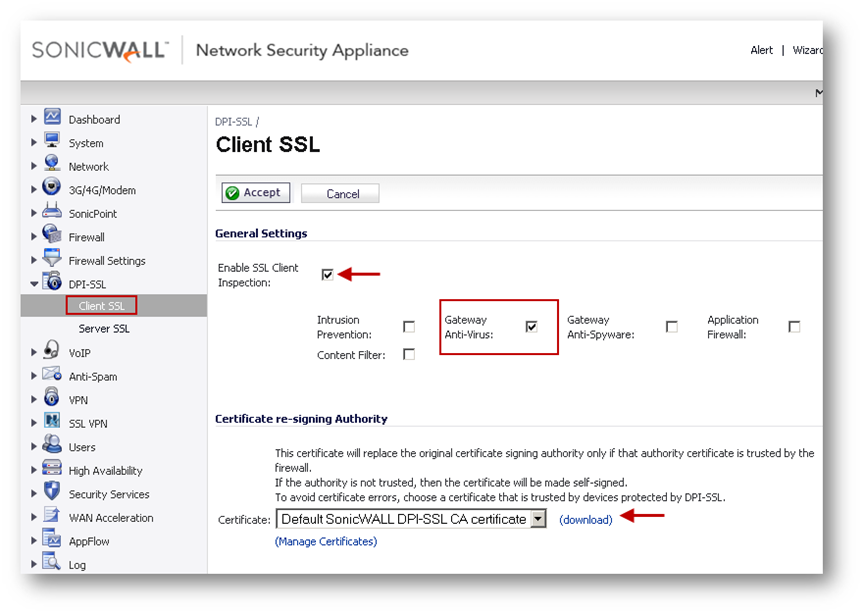
Other options like including or excluding users, IP addresses are not enabled in this example but can be enabled as per the deployment. Although none of the Security Services except GAV are enabled, all traffic with standard SSL ports as destination will be re-signed by Client DPI-SSL .
Step 3. Configure Server DPI-SSL
When the FTPS server is behind the SonicWall and clients connect to it from the WAN side of the SonicWall. Before configuring Server DPI-SSL we must import a server certificate into the SonicWall. Although the server certificate could be either from a Windows CA or from a public CA like GoDaddy, it is recommended to use a certificate signed by a public CA. Please refer to these articles on how to obtain a server certificate: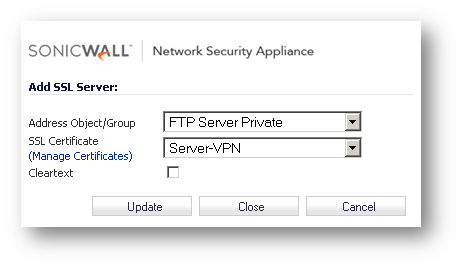
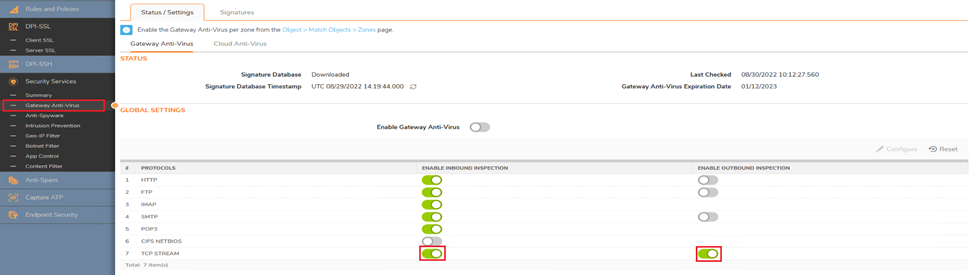
Step 4. Configure Gateway Anti-Virus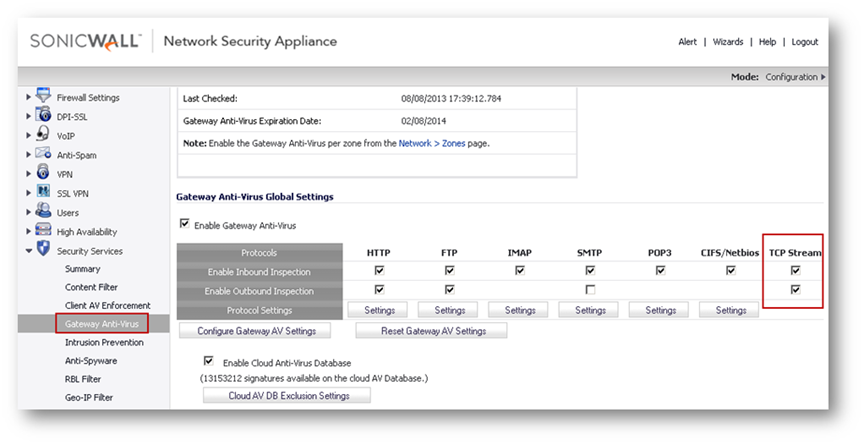
FTP Settings under Protocols need not be checked because the following options will not be enforced:
Related Articles
- Configuring split DNS over site to site VPN
- How to enable DNS Doctoring?
- Understanding TCP Handshake violation
Categories
- Firewalls > TZ Series
- Firewalls > SonicWall SuperMassive E10000 Series
- Firewalls > SonicWall SuperMassive 9000 Series
- Firewalls > SonicWall NSA Series






 YES
YES NO
NO