Scam Alerts Deceiving Users to Download Harmful Android Applications
by Anand Singh

SonicWall Capture Labs threat researchers identified an ongoing Android scam campaign targeting users with fake promotional offers, cashback rewards, and traffic-fine notifications. Distributed via social media, messaging platforms, and third-party app stores, the campaign deceives victims into installing a malicious application disguised as a legitimate service. Once installed, the app requests intrusive permissions, displays phishing interfaces to steal card details, OTPs, and UPI PINs, intercepts calls and SMS messages, and exfiltrates sensitive device and user data to attacker-controlled command-and-control (C2) servers.
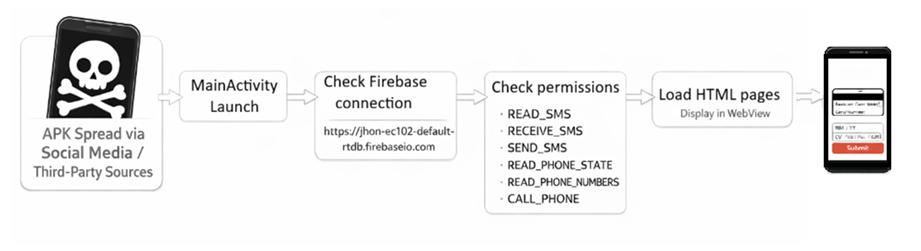
Infection Cycle
The application, presented as “Gift Card Hub,” invites users to spin a wheel for a chance to win a reward, claiming they can obtain a $100 gift card of their choice for just $1, as shown below:

The app offers items for $1, asks for payment, collects card details, and sends them to the attacker’s server.

This campaign also targets users in India with messages about vouchers, cashback, and traffic fines.
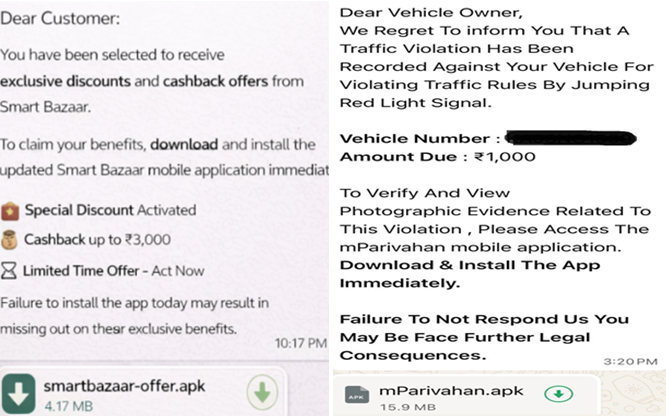
The images show how attackers use cashback offers and traffic-fine messages to lure users into installing the malicious apps.



The malware gathers device details and sends them to its server.

The malware uses a WebView to open and display a local web page (index.html) stored inside the app asset folder.

The index.html file includes malicious scripts that collect the user’s phone number and send it to the attacker’s Telegram bot.


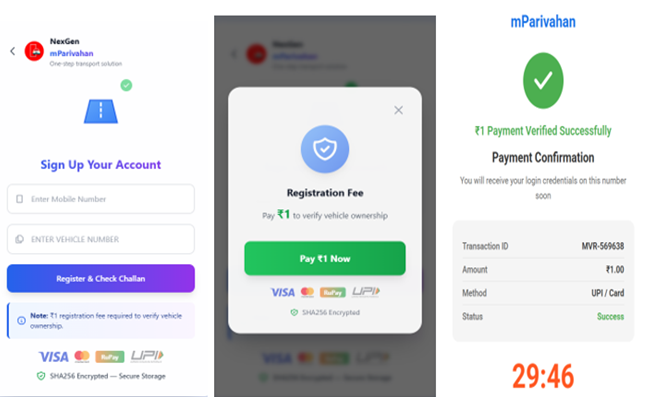
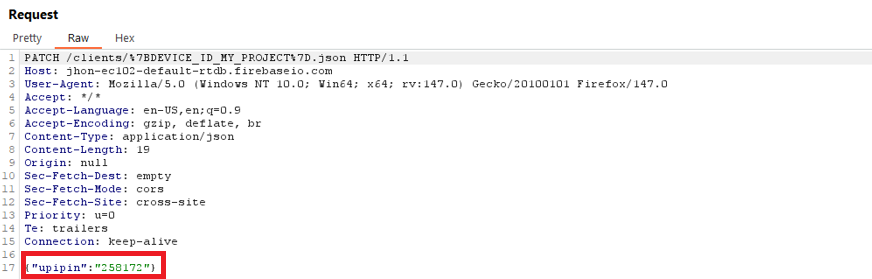
The app asks the user to make a UPI payment and secretly captures the entered UPI PIN and payment details, sending them to an attacker-controlled Firebase database
Using a Telegram bot token and chat ID, can access victims’ personal information and stolen card details.
SonicWall Protections
SonicWall Capture Labs provides protection against this threat via the SonicWall Capture ATP w/RTDMI.
Indicators of Compromise (IOCs)
APK file’s Sha-256
- 062064dee2e7da5c5891c9c649ce1a6ab020ba641e025743882412519573a4a
- 050a7a439a90132f171f6db3204ea3c83ede55d5b99727003b27115805733e39
- 289685e41ee3d8de8fbd752b417931f282ae4b1df1b0655c2c5d48f9db0270fe
- 2f4b62e3769e985cdc0a1b72152b2c490893603da1721288a3bed54d21426101
- 57ae96091e3b291e2605cacd06a82bef532f4018ade371544576847b8fe33c06
- 63c57600a8c3c60d9e510f8c018ae49bb317d2172984f575f38ab5fbf5e6a7d0
- 85854ca0db5537b05de925193b8cdebe244f75c672c21d55b61914ede1d930d0
- b63b44590cb88deb2dd670251af9d501272605aa55f3b53cc880328e0c63d4e9
- 9138da79c1048a998775df77dd82230ab3575e162b282ae8ea8fd7b3eb67fad6
- db138a9045435c1ebad73bebfba92d2728f7b11f3daf2cf58fca0b969f73438e
- dde1445eeefb056afad4aa70c3e106801f432a25b52b63274261f0ae2f560e35
- ff9f4c85bdd75b622aa3f21729000afa1a53141e07baacacf6820e1b87023688
Network:
- hxxps[:]//api[.]telegram[.]org/bot7978134875[:]AAEq6r0Yd6FoRcBptYvVj_0sdQzMyYzvRFw/SendMessage
Share This Article

An Article By
An Article By
Anand Singh
Anand Singh
