An In-Depth Look at Scarface Stealer

Overview
This week, the SonicWall Capture Labs Threat Research team analyzed a sample of ScarfaceStealer, a Go-compiled information stealer that utilizes sophisticated anti-analysis techniques including:
- Heavy String Obfuscation - Uses space/rocket-themed junk strings to evade detection
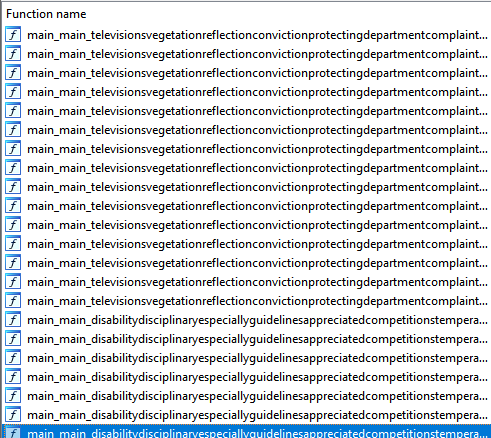
- Function Name Obfuscation - Main functions use randomly concatenated English words
- Go Embed Package - Embeds configuration/payloads within the binary
- Minimal Visible Strings - Only 47 strings visible through Ghidra's string analysis
Technical Overview and Infection Cycle
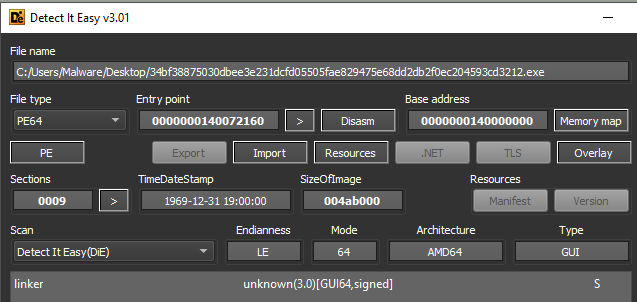
Initial detection shows an unknown file type, but sections and section data show that the file is a Golang binary. The timestamps have also been tampered with to show a compile time of 1969.
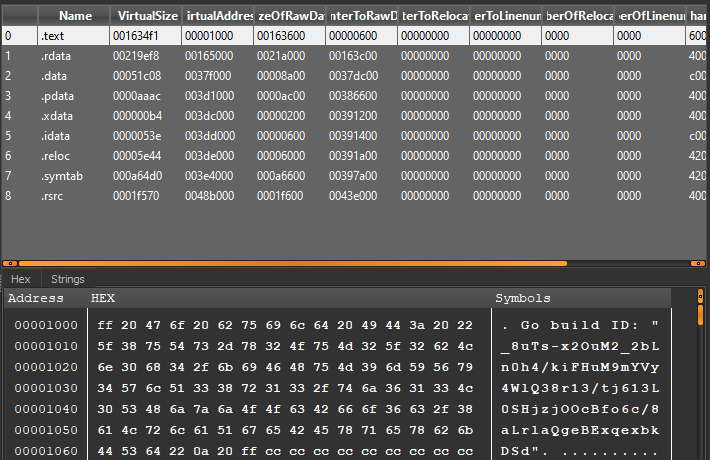
The file is heavily obfuscated with both function calls and strings. During runtime, these do not decode or rename themselves.
At runtime, the following is executed:
Phase 1: Initialization
- main.Introducing - Initializes malware components
- main.Impossible - Performs anti-VM/sandbox checks
- main.Existence - Checks for existing infections
Phase 2: Target Identification
- main.Identifying - Fingerprints the system
- main.Selecting - Identifies valuable targets (browsers, wallets)
Phase 3: Data Collection
- main.Solutions - Core stealing functionality
- main.Microphone - Audio capture
- main.Thumbnails - Screenshot capture
- main.Demonstrate - Extensive data gathering
Phase 4: Staging
- main.Preparing - Stages collected data
- main.Allowance - Manages resource allocation
Phase 5: Exfiltration
- main.Coordinate - Coordinates with C2
- main.Descending - Exfiltrates data
LAUNCH_COMMAND, trajectory_calibration, TELEMETRY, orbital_insertion, IGNITION, HANDSHAKE_COMPLETE, MISSION_ABORT, FUEL_SYSTEM_NOMINAL Stage1, Stage2, Stage3, prelaunch, countdown, liftoff ALPHA_ZULU, BRAVO_TANGO, GPS-Galileo-GLONASS trajectory_optimization_score, gravitational_alignment_value quaternary_stabilization_node, quantum_entanglement
Configuration and payloads may be embedded within the binary using Go's embed package.
Imported DLLs and Capabilities
DLL Dependencies
| DLL | Purpose |
| kernel32.dll | Core Windows operations (file I/O, memory management, process control) |
| ntdll.dll | Low-level NT functions |
| advapi32.dll | Registry operations, security functions |
| ws2_32.dll | Winsock networking |
| dnsapi.dll | DNS query operations |
| crypt32.dll | Cryptographic functions |
| mswsock.dll | Microsoft Windows sockets extensions |
| secur32.dll | Security support provider interface |
| shell32.dll | Shell operations |
| userenv.dll | User environment management |
| iphlpapi.dll | IP helper API (network configuration) |
| netapi32.dll | Network management |
Key Windows API Functions
File Operations
- CreateFileW, DeleteFileW, MoveFileW
- ReadFile, WriteFile, SetEndOfFile
- GetFileAttributesW, SetFileAttributesW
- GetTempPathW, GetCurrentDirectoryW
- FindClose, CreateFileMappingW
Process/Thread Operations
- CreateThread, CreateProcessAsUserW
- OpenProcess, ExitProcess
- GetCurrentProcessId, GetExitCodeProcess
- TerminateProcess, WaitForSingleObject
Memory Management
- VirtualAlloc, VirtualFree, VirtualQuery, VirtualLock
- LocalAlloc, LocalFree
Registry Operations
- RegCloseKey, RegCreateKeyExW
- RegQueryValueExW, RegQueryInfoKeyW
- RegLoadMUIStringW, RegDeleteValueW
Network Operations
- WSAStartup, WSACleanup, WSAIoctl
- WSARecvFrom, WSASendTo
- closesocket, getsockname, getpeername
- getsockopt, setsockopt
- DnsQuery_W, DnsRecordListFree
- GetAddrInfoW, TransmitFile, AcceptEx
Cryptographic Operations
- CryptAcquireContextW, CryptReleaseContext
- CertOpenSystemStoreW, CertGetCertificateChain
Security/Authentication
- GetTokenInformation, LookupAccountSidW
- LookupAccountNameW, ConvertSidToStringSidW
- ConvertStringSidToSidW, GetLengthSid
Readable Main Functions
The following exported functions likely contain the core malware logic:
| Function | Likely Purpose |
| main.Allowance | Resource allocation/permission checks |
| main.Coordinate | Data coordination/C2 communication |
| main.Demonstrate | Core functionality (multiple sub-functions) |
| main.Descending | Data exfiltration/download |
| main.Existence | Persistence mechanism checks |
| main.Identifying | Target identification/fingerprinting |
| main.Impossible | Anti-analysis/VM detection |
| main.Introducing | Initialization routines |
| main.Investing | Resource gathering |
| main.Masturbation | Data stealing |
| main.Microphone | Audio capture capability |
| main.Preparing | Pre-exfiltration staging |
| main.Selecting | Target selection |
| main.Solutions | Core stealer logic |
| main.Thumbnails | Image/screenshot capture |
| main.Typically | Standard operations |
Suspected Capabilities
Based on code analysis, this stealer likely targets:
Browser Data
- Cookies
- Saved passwords (Login Data)
- Browser history
- Autofill data
System Information
- Hardware fingerprinting
- Network configuration
- User account details
- Installed software
Communication
- Uses net/http for HTTP communications
- TLS support (crypto/tls, crypto/x509)
- DNS operations for domain resolution
Audio Capture
- main.Microphone function suggests audio recording capability
Screen Capture
- main.Thumbnails function suggests screenshot capability
The following ciphers are referenced throughout the file:
| Algorithm | Usage |
| AES256 | Data encryption |
| ChaCha20 | Stream cipher |
| SHA3-512 | Hashing |
| BLAKE2b | Hashing |
| RSA1024/RSA2048 | Asymmetric encryption |
| Whirlpool | Hashing |
| TLS 1.0/1.3 | Secure communication |
MITRE ATT&CK Mapping
| Technique ID | Technique Name | Evidence |
| T1059 | Command and Scripting Interpreter | os/exec package |
| T1005 | Data from Local System | File access APIs |
| T1012 | Query Registry | Registry API imports |
| T1082 | System Information Discovery | System info collection |
| T1083 | File and Directory Discovery | File enumeration APIs |
| T1071 | Application Layer Protocol | HTTP/TLS communication |
| T1027 | Obfuscated Files or Information | Space-themed string obfuscation |
| T1041 | Exfiltration Over C2 Channel | Network APIs |
| T1123 | Audio Capture | main.Microphone function |
| T1113 | Screen Capture | main.Thumbnails function |
| T1056 | Input Capture | Credential stealing |
Conclusion
This ScarfaceStealer sample represents a moderately sophisticated Go-based information stealer that employs creative obfuscation techniques to evade detection and hinder analysis. The space/rocket mission themed strings are a unique fingerprint of this malware family. The use of Go provides cross-platform potential while complicating reverse engineering due to Go's unique calling conventions and runtime. The embedded configuration via Go's embed package suggests the malware may be easily repackaged with different C2 configurations.
Sonicwall Protection
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: ScarfaceStealer.Rocket (Trojan)
This threat is also detected by SonicWall Capture ATP with RTDMI™ and the Capture Client endpoint solution.
IOCs
34bf38875030dbee3e231dcfd05505fae829475e68dd2db2f0ec204593cd3212
Share This Article

An Article By
An Article By
Security News
Security News