How to Block Freegate using App Control Advanced



Description
How to Block Freegate using App Control Advanced
Resolution
Feature/Application:
Freegate is a web proxy that uses a proprietary, obfuscated/encrypted application layer protocol to thwart content filtering and application control by firewalls. In addition to Freegate specific signatures, blocking this application requires Signature ID 5 and 7 to be enabled.
This KB articles describes how to block Freegate traffic.
These are the signatures to be enabled for effectively blocking Freegate:
-
PROXY-ACCESS > Freegate signatures - Identify HTTPS handshake between Freegate client and servers.
-
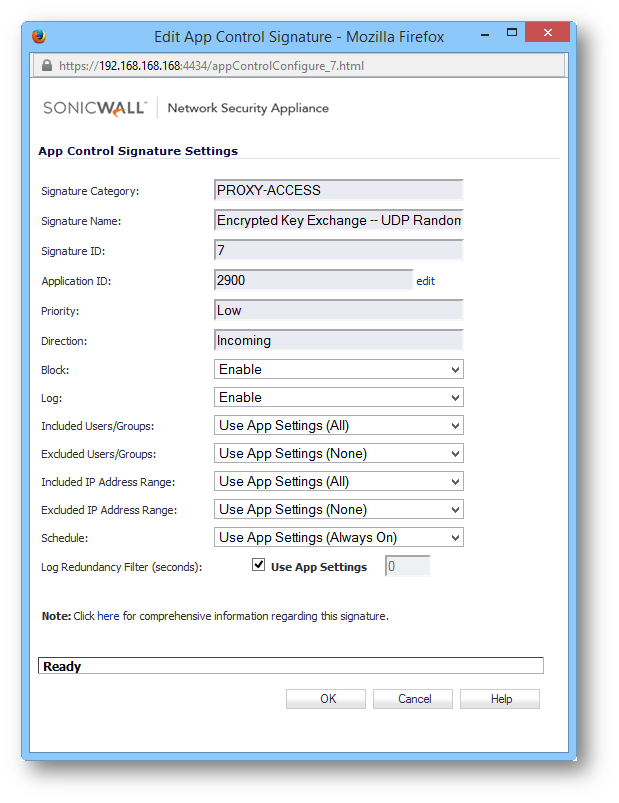
PROXY-ACCESS > Encrypted Key Exchange -- UDP Random Encryption - SID 7 - blocks UDP tunnel traffic. Enabling this signature will not only block encrypted Freegate traffic over UDP but also block other encrypted UDP traffic like IPSec VPN traffic passing through the SonicWall.
Note: Before enabling this signature, exclude the outside or inside IP addresses of legitimate IPSec traffic. -
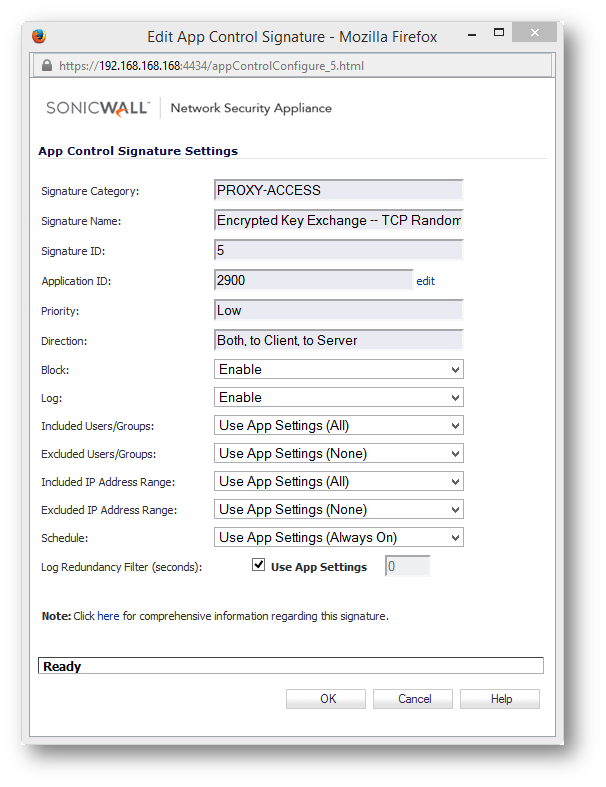
PROXY-ACCESS > Encrypted Key Exchange -- TCP Random Encryption - SID 5 - blocks TCP tunnel traffic. Enabling this signature will not only block encrypted Freegate traffic over TCP but also block other encrypted TCP traffic passing through the SonicWall.
Note: Before enabling this signature, exclude the outside or inside IP addresses of such legitimate traffic.
Procedure:
- Login to the SonicWall Management GUI.
- Navigate to the Firewall > App Control Advanced page. In Gen5 TZ devices this page is under Security Services > App Control
- Check the box under Enable App Control and click on the Accept button at the top to enable App Control.
- Under App Control Advanced > View Style select PROXY-ACCESS under Category;
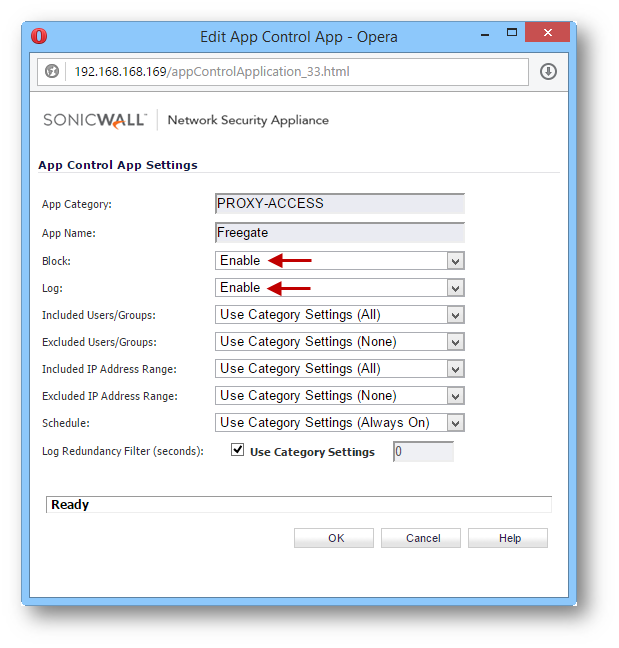
- From the drop-down under Application, select Freegate.
- Click on Configure alongside Application with Freegate selected
- In the new window, select Enable under the Block and Log fields.
- Click on OK to save
- In the Lookup Signature ID field, enter 5
- Click on the search icon
- In the new window, select Enable under the Block and Log fields.
- Click on OK to save
- In the Lookup Signature ID field, enter 7
- Click on the search icon
- In the new window, select Enable under the Block and Log fields.
- Click on OK to save
Enabling Application Control Service on zones
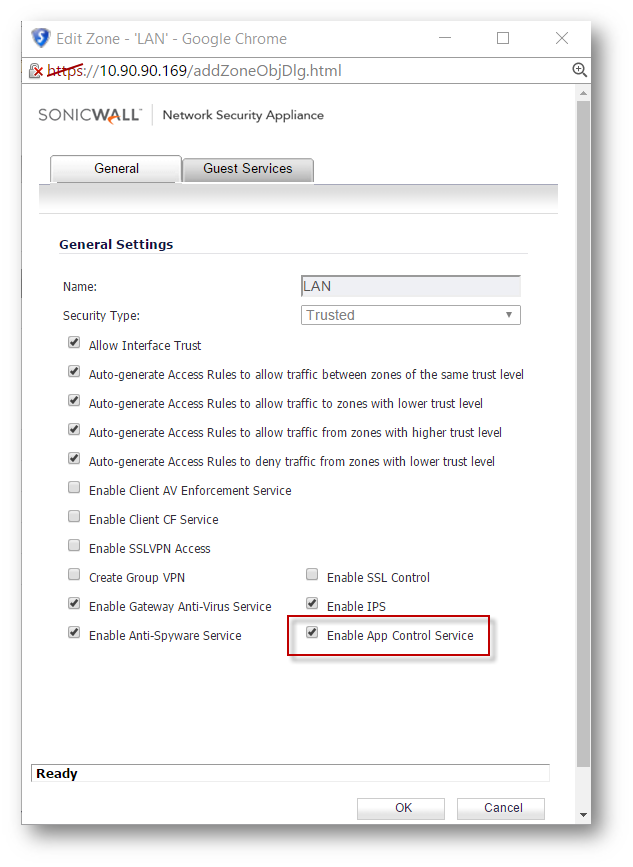
- Navigate to Network > Zones
- Click on the configure button under the zone where you want to enable App Control.
- Check Enable App Control Service.
- Click on OK to save.
Testing
From a host behind the SonicWall, launch the Freegate application and try to connect. The application will not be able to establish a tunnel.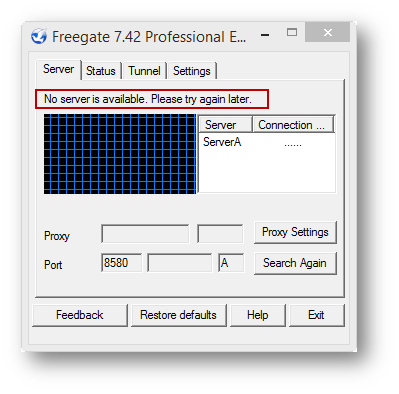
Under SonicWall logs, log messages similar to the following will be generated: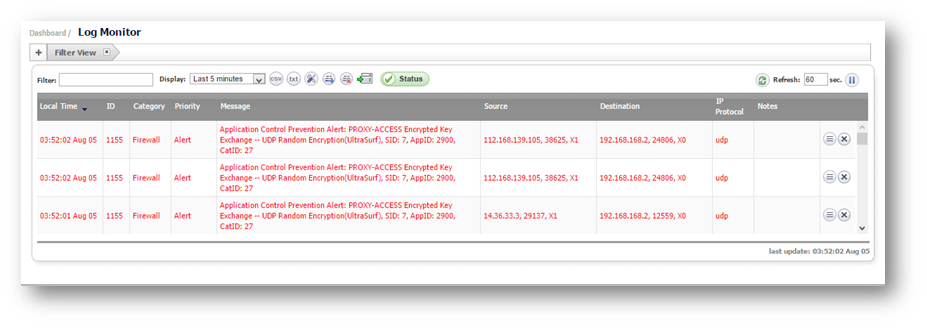
Related Articles
- How to enable DNS Doctoring?
- Understanding TCP Handshake violation
- How can I Install SonicWall NSv on AWS ?
Categories
- Firewalls > TZ Series
- Firewalls > SonicWall SuperMassive E10000 Series
- Firewalls > SonicWall SuperMassive 9000 Series
- Firewalls > SonicWall NSA Series






 YES
YES NO
NO