Comparison of CFS 3.0 to CFS 4.0



Description
This article will discuss the differences between the new CFS 4.0 and the old CFS 3.0.
You can also check "Upgrade from CFS 3.0 Zones and Users Mode to CFS 4.0 (Best Practice)" and "KB210386 Upgrade from CFS 3.0 Zones and Users Mode to CFS 4.0 (Best Practice)" for more CFS upgrading information.
Please, note the following:
- there are no significant changes for Websense between CFS4.0 and the previous releases, the upgrading process for Websense will not be discussed in these articles.
- Restrict Web Features has been removed from CFS 4.0 , if you would like to do the similar configurations, you can refer to the "KB 212681: How to realize Restrict Web Features in CFS 4.0".
Cause
CFS 4.0 is available from SonicOS version 6.2.6 and above for NSA and above appliances. As there are big changes between the new 4.0 and the old 3.0 CFS, it's really important to know about the differences between this two versions, especially when you need to do the upgrade.
Resolution
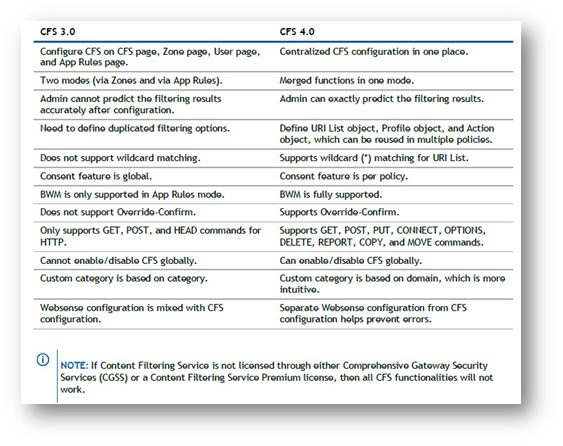
The following table summaries the differences of the user experience for various aspects between the old 3.0 and the new 4.0 CFS.
2. New CFS Objects
CFS 4.0 uses an object based model. A new Content Filter Objects page has been introduced under the Firewall menu with three CFS objects listed. These CFS objects replaces several features in CFS 3.0.
- URI List Objects: This replaces the features Custom Allowed List, Custom Forbidden List, Keywords List, CFS Allowed/Forbidden List in App Rules, and part of Restrict Web Features (per file extensions) in CFS 3.0.
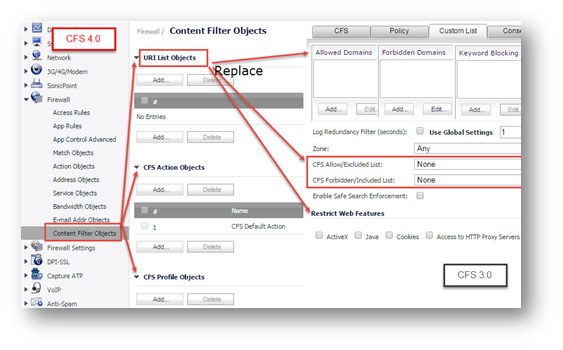
- CFS Action Objects: This is a new concept in CFS 4.0. Compared with CFS 3.0, it provides detailed configurations for actions (Block, Confirm, Passphrase and BWM).
Note: Confirm, Passphrase and BWM are the new actions in CFS 4.0.
3. New CFS Policy
The new CFS policy engine allows administrators to define the following matching conditions (Source Zone, Destination Zone, Address Object, Users/Groups, Schedule, Enabled, CFS Profile, and CFS Action) for a CFS Policy.When a packet is processed, the conditions (Source Zone, Destination Zone, Address Object, Users/Groups, Schedule, Enabled) are checked. If all of these conditions are matched, the packet is filtered by the corresponding CFS Profile. Then the CFS Action is invoked according to the filtering results.

CFS policies now follow a priority defined by the order set in the Content Filter page. CFS 3.0's least restrictive and most permissive policies follow a new, high-to-low priority model in CFS 4.0. When matching policies, a CFS Policy with higher priority is checked earlier. Priority is determined by position in the policy list, with the highest priority given to the policy at the top. As a general practice, the highest priority should be assigned to specific/granular policies and lower priority to more generic policies that apply to a broader set of users.
Related Articles
- How to enable DNS Doctoring?
- Understanding TCP Handshake violation
- How can I Install SonicWall NSv on AWS ?
Categories
- Firewalls > TZ Series
- Firewalls > SonicWall SuperMassive E10000 Series
- Firewalls > SonicWall SuperMassive 9000 Series
- Firewalls > SonicWall NSA Series






 YES
YES NO
NO