Langflow AI Code Injection to RCE Flaw

Langflow AI Code Injection to RCE Flaw (CVE-2026-33017)
Overview
The SonicWall Capture Labs threat research team became aware of a code injection vulnerability in Langflow AI, assessed its impact and developed mitigation measures. Langflow AI is a Python based web application that provides a visual interface to build AI-driven agents and workflows.
The issue, tracked as CVE-2026-33017, affects all versions prior to 1.8.X got listed is CISA-KEV catalog. This flaw, categorized under CWE-94 (Improper Control of Generation of Code (Code Injection), allows an unauthenticated remote attacker to achieve remote code execution, earning a high CVSS score of 9.8. Langflow processes user-controlled JSON data and passes Python code embedded in node definitions directly to Python's exec() function, without sandboxing. As Langflow continues to gain popularity and broader adoption, the risk associated with this vulnerability increases significantly. Users are strongly encouraged to apply the vendor-provided updates without delay.
Technical Overview
This AI model offers a visual interface that makes it easy to design workflows, along with built-in APIs and MCP servers that allow these workflows to be used as tools in applications across different frameworks and technologies. It comes with many built-in features and supports major LLMs, vector databases, and a growing set of AI tools.
Figure 1 illustrates the overall Langflow Operation architecture. Users can visually build workflows, which are sent to the backend API server for management and execution. The execution engine processes the flow step-by-step, invoking AI models, tools, and external services as needed, and then returns the results while storing data in databases or file storage.
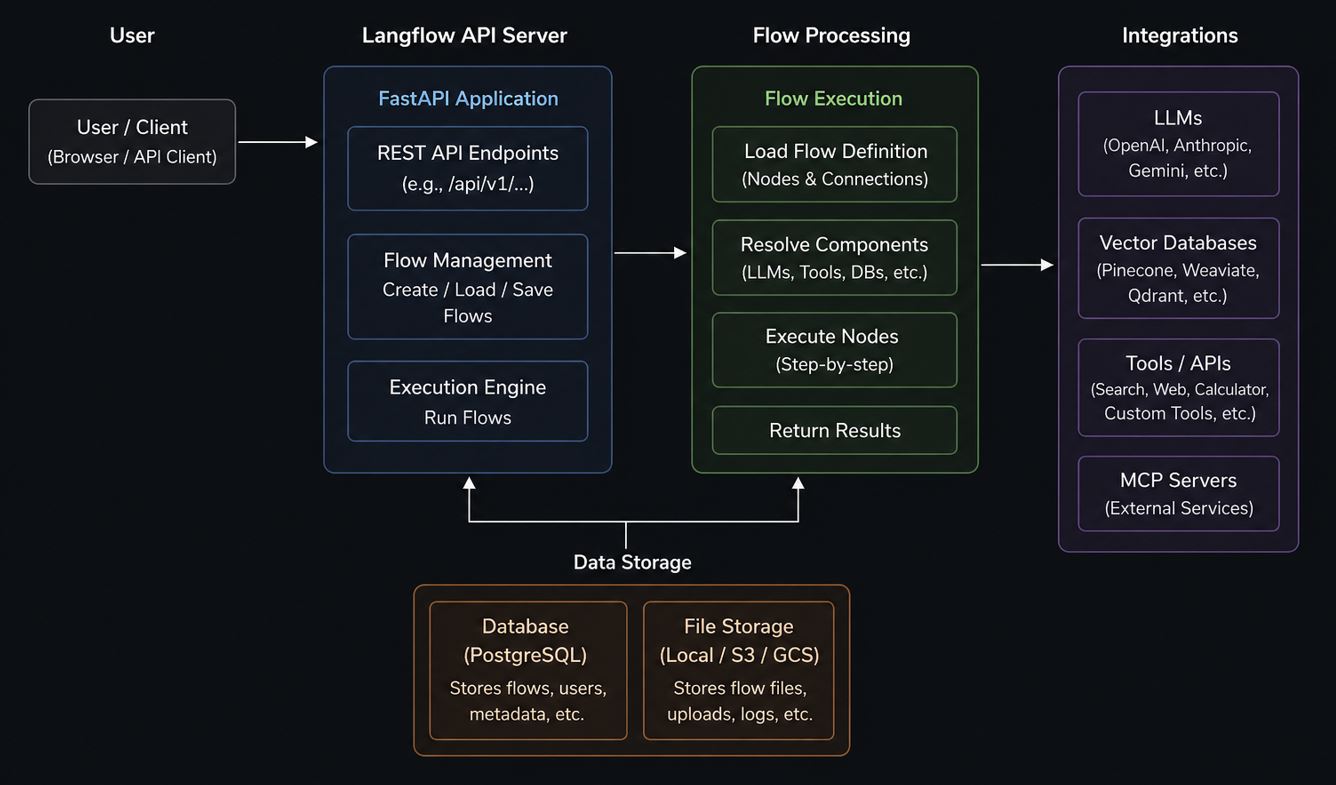
Key security characteristics of Langflow include:
- its modular flow-based architecture
- Support for integration with external services such as LLMs and APIs.
- The ability to execute dynamically defined workflows.
- In patched versions, Langflow enforces stricter trust boundaries by ensuring that only validated, server-side flow definitions are executed, thereby reducing the risk of code injection and unauthorized manipulation.
Root Cause
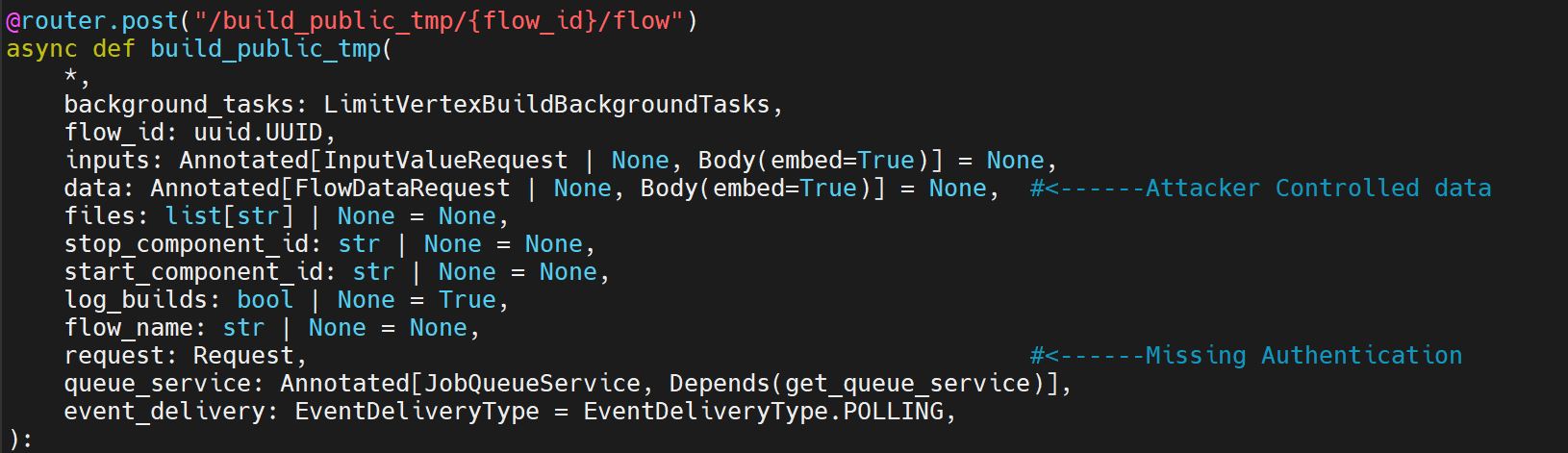
The vulnerability stems from the optional data parameter accepting attacker-controlled flow data (containing arbitrary Python code in node definitions) instead of the stored flow data from the database. The function build_public_tmp located in src/backend/base/langflow/api/v1/chat.py reads this parameter and applies it without validation.
The POST /api/v1/build_public_tmp/flow_id}/flow endpoint allows anyone to build public flows without authentication. Input submitted to this endpoint is executed directly via the exec () function without any form of sandboxing or input validation. This behavior introduces critical security vulnerability, enabling unauthenticated remote code execution (RCE). The affected code snippet that builds a public flow without requiring authentication is shown in Figure 2.
The endpoint:
1. Verifies the requested flow(s) are marked as public in the database.
2. Creates a deterministic UUID based on client_id and flow_id
3. Uses the flow owner's permissions to build the flow.
Requirements:
- The flow must be marked as PUBLIC in the database.
- The request must include a client_id cookie.
Because Langflow operates with full system access, including file operations and shell command execution, compromising a public flow creation with auto_login effectively grants complete control over the victim’s machine. Since there is no origin validation, authentication, or restriction on the data parameter in vulnerable versions, any attacker-controlled connection to endpoint is accepted.
Patch Analysis
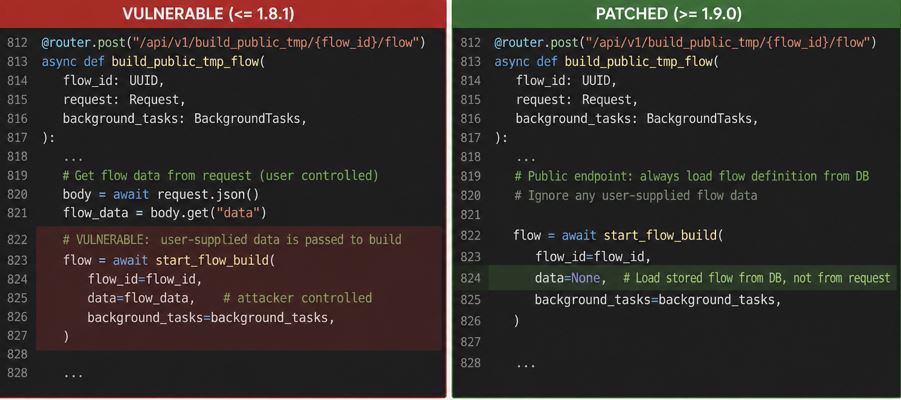
The security fix introduced in patched versions above 1.9.0, as shown in Figure 3, adds a confirmation prompt whenever the data is changed. It means that the operation executes only what is stored and trusted. This helps deter simple one-click exploitation by requiring user interaction.
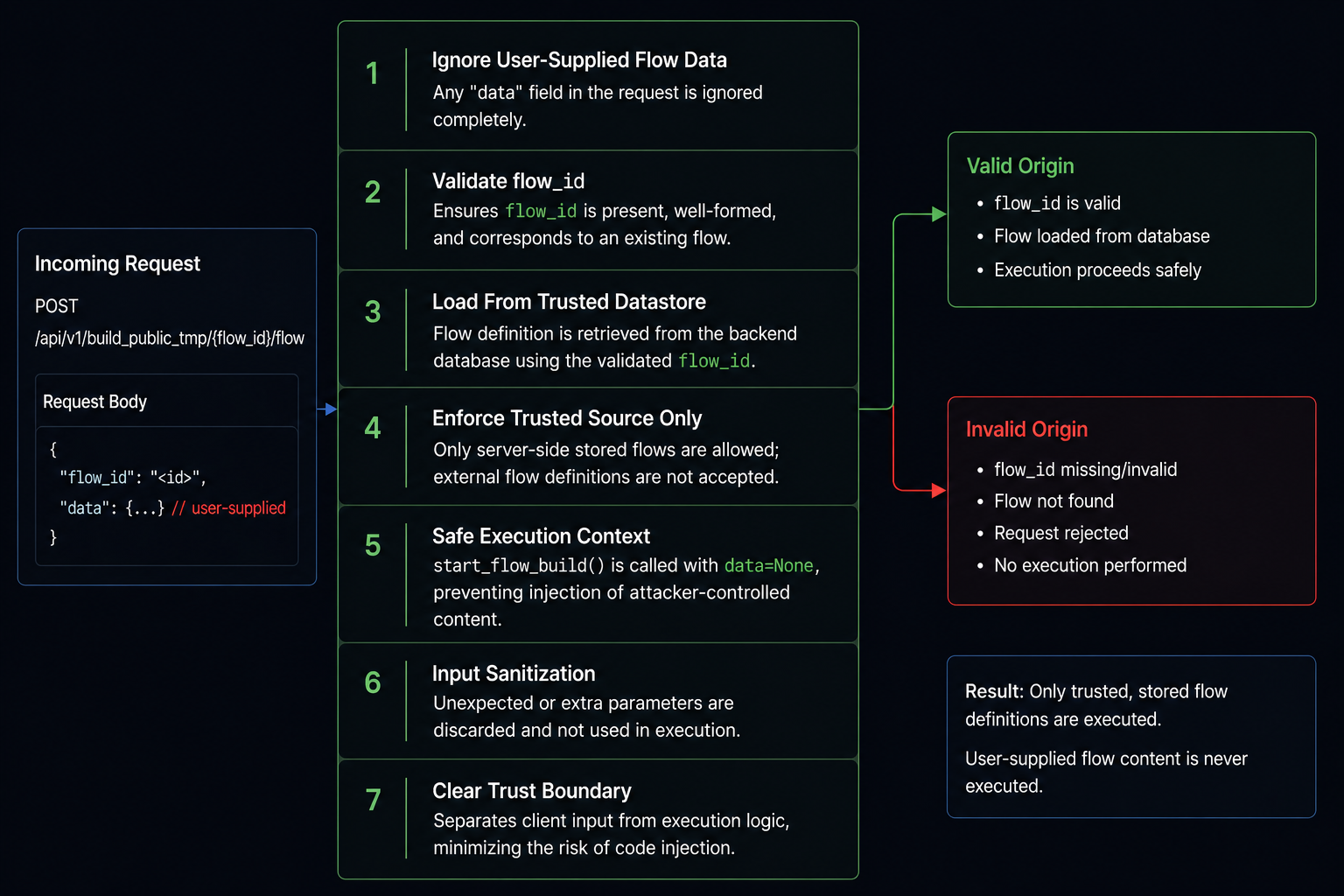
The Security updates implemented stringent origin validation controls, as shown in Figure 4. The new logic evaluates incoming requests using the following checks:
- The patched implementation ensures that user-supplied flow data is ignored for public flow execution endpoints.
- Incoming requests are validated such that only a valid flow_id is accepted, and no arbitrary flow definitions from the request body are processed.
- The system enforces that flow definitions are exclusively retrieved from the trusted backend datastore, eliminating reliance on external input.
- The execution function (start_flow_build) is invoked with data=None, preventing injection of attacker-controlled parameters.
- Requests are handled within a controlled execution context, ensuring that only predefined and stored node configurations are executed.
- The updated logic introduces a clear separation between client input and execution logic, reducing the attack surface for code injection.
- Any unexpected or malformed input is effectively disregarded, rather than being interpreted or executed.
Triggering the Vulnerability
The exploitation process typically follows these steps:
- The attacker targets the vulnerable endpoint via a POST request to vulnerable component build_public_tmp and a public flow id or UUID such as:
- http://<target-ip>:7860/api/v1/build_public_tmp/ANY_UUID/flow
- The attacker creates a JSON payload that mimics a standard Langflow graph. The "payload" is hidden inside a PythonFunction or CustomComponent.
- The Environment Variable LANGFLOW_AUTO_LOGIN=True is a prerequisite.
- Langflow initiates a connection and sends attacker's data passed directly to graph builder along with authentication token and Flow ID.
- The attacker captures the authentication token.
- The attacker reconnects to the legitimate gateway using the stolen token and flow id.
- This code is passed to exec() with zero sandboxing, resulting in unauthenticated remote code execution.
Exploitation
Successful exploitation enables a remote, unauthenticated attacker to steal an authentication token and use it to gain full control of the affected system. Figure 5 demonstrates a real-world proof of concept, showing successful token capture and creating a public flow id, using a publicly available exploit. Given Langflow’s extensive system privileges, this vulnerability can result in complete compromise of the operator’s machine. Figure 6 verifies the exploitation along with the Langflow’s logs.
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:
- IPS: 22070 Langflow Public Flow Build Endpoint RCE
- IPS: 22098 Langflow Public Flow Build Endpoint RCE 2
Remediation Recommendations
With Langflow’s growing user base and increasing deployment footprint, organizations and individual users should upgrade to the latest patched version as outlined in the official vendor advisory.
Relevant Links
Share This Article

An Article By
An Article By
Dhiren Vaghela
Dhiren Vaghela
Dhiren Vaghela has over a decade of experience in the IPS domain, with a strong focus on defensive security. His expertise lies in identifying, analyzing and mitigating vulnerabilities. Dhiren is well-versed in content-based signature writing, scanner-based alert generation and technical blog writing. By leveraging emerging technologies, he has developed numerous IPS signatures across various protocols. Known for his exceptional signature writing skills and collaborative team spirit, Dhiren is a valuable asset in the field of cybersecurity.
