-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
How to apply a passphrase to websites/web categories on SonicOSX 7.0



Description
Another restrict action, Passphrase can be used to restrict the web access instead of just blocking it. Once the Passphrase action has been selected, the user will be redirected to a passphrase page when attempting to access the specified website. From this page, the user will need to enter the preset password to continue to the intended site.
If the password is correct, web access will be allowed. Otherwise it will be blocked and a blocked page will be sent to the client.
If the user didn't enter the correct password the first time, the passphrase page will be sent to the client again to prompt for thepassword a second time. Currently, client users have three opportunities to enter their passwords, meaning that if a user makes three failed attempts to enter the correct password, the site will be blocked.
If client users don't know the password, they can click 'Cancel' and the site will be blocked immediately.
Resolution
The Passphrase action can be applied to the Web category, URI Lists, or both. For HTTPS websites, Client DPI-SSL must be enabled to apply Passphrase. We would need to perform the following steps for this setup.
 EXAMPLE: We would like to allow access to Web categories: News and Media, Search Engines and Portals, and allow access to the websites: monster.com and indeed.com only if the right passphrase is entered.
EXAMPLE: We would like to allow access to Web categories: News and Media, Search Engines and Portals, and allow access to the websites: monster.com and indeed.com only if the right passphrase is entered.
Steps:
- Create a Decryption Policy
- Create Security Policies with the right web categories and URI list selected, with CFS Action Profile to apply Passphrase.
Creating a Decryption Policy:
Decryption policy matches the traffic, and the only two actions we can take are Decrypt and Bypass. With decryption, we get more visibility to the data helping us in performing better matches and applying the right security policy.
- Make sure that Client DPI SSL is enabled globally based on the KB article: How to create a Decryption Policy on SonicOSX 7.0?
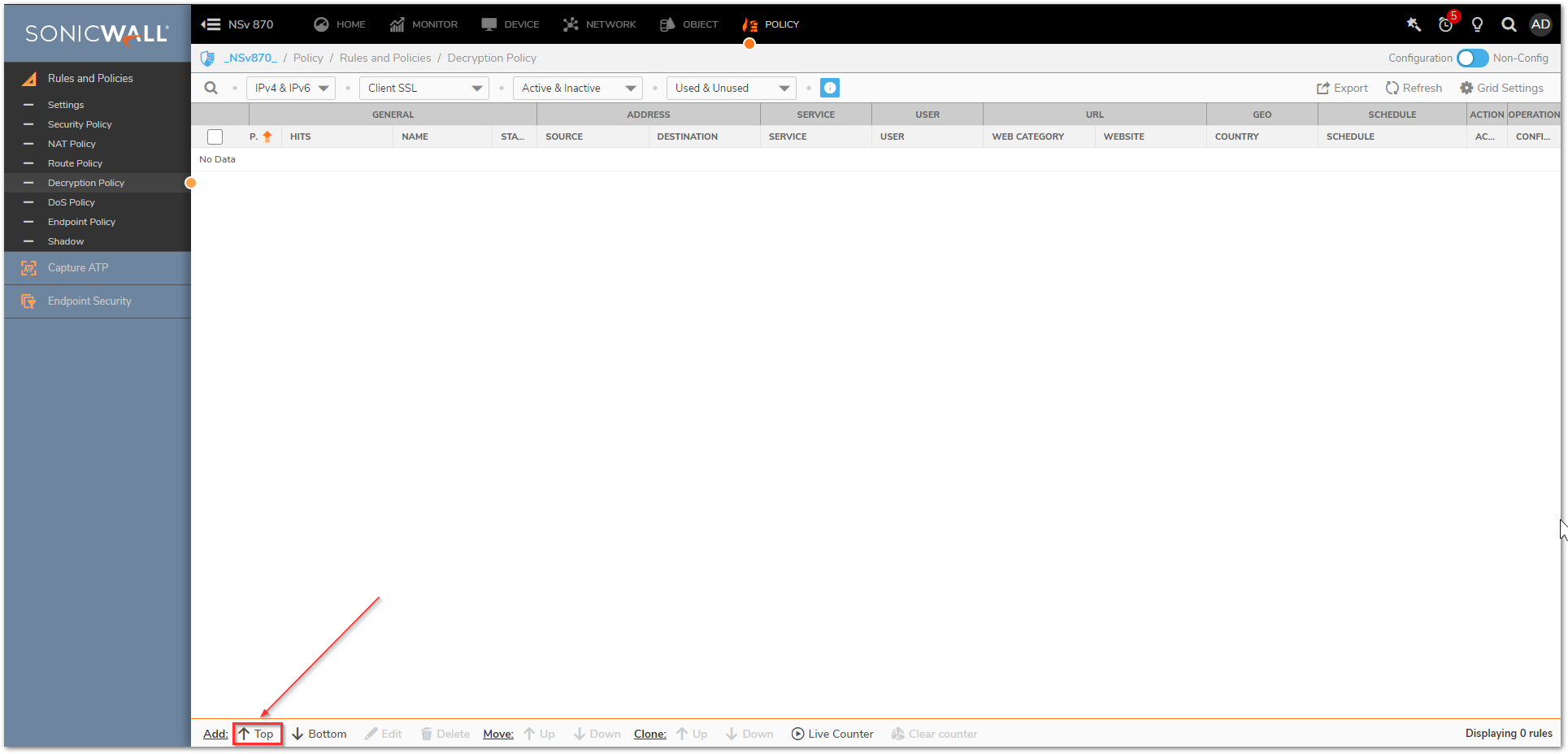
- Navigate to Policy | Rules and Policies | Decryption Policy tab and click on Top at the bottom of the screen. If you have multiple policies it is very important to choose the right priority to make sure that the decryption policy is getting applied to the necessary traffic.
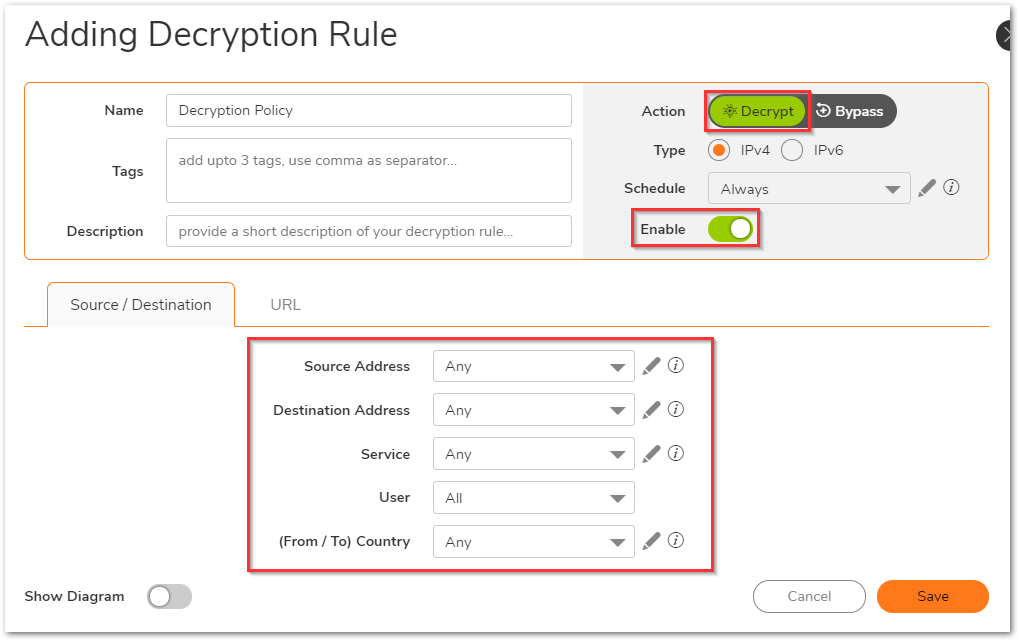
- Select the appropriate Source/Destination/Service or leave all options to Any to decrypt all traffic. Make sure that the action is set to Decrypt and the policy is enabled.
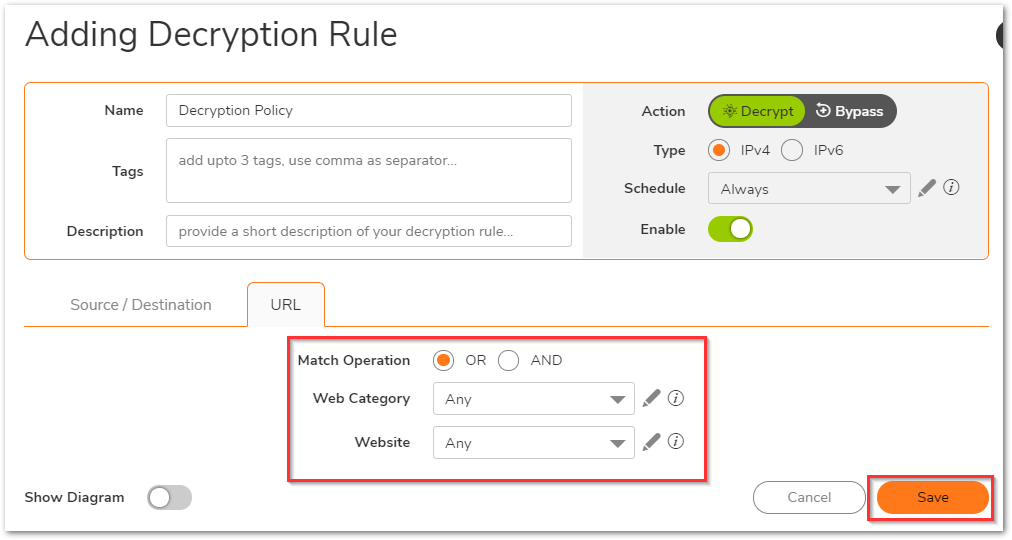
- On the URL tab, you can do this for specific web categories or to the URI list. In this example, they are left on Any. Click Save.
Creating a Security Policy
Security Policy ties together the URI list object, Web category and Security Rule Action so that we know what action needs to be taken for a specific match. Before an HTTP/HTTPS connection can be made, the end machine would need to perform DNS resolution of the URL. Since we have an implicit deny rule, DNS traffic needs to be allowed as well.
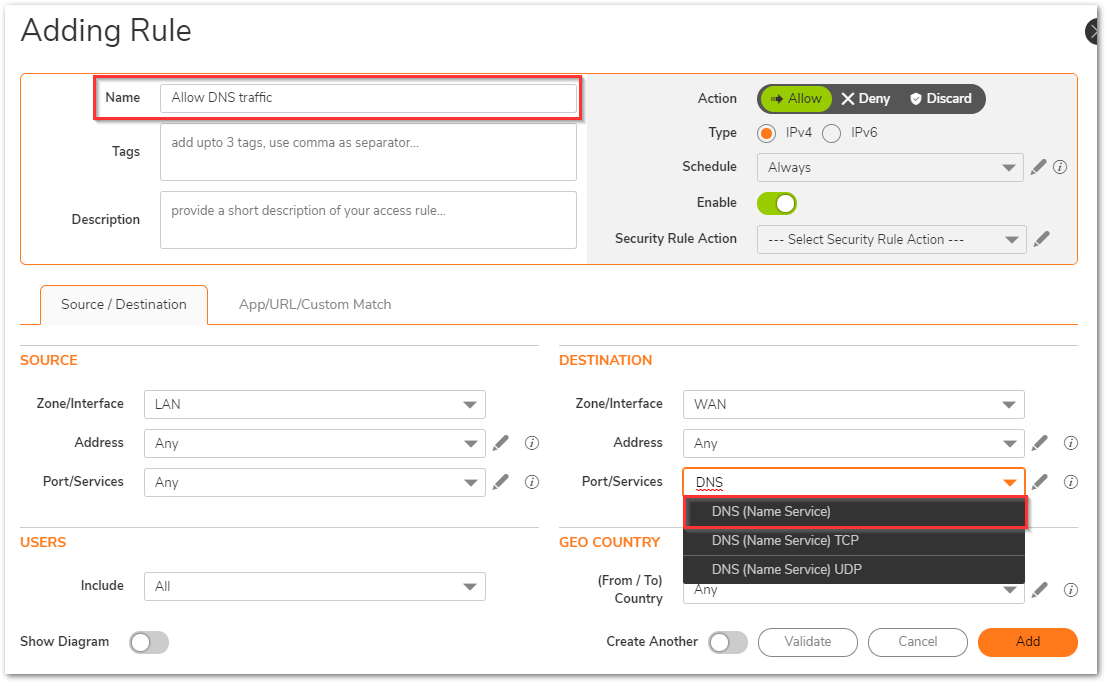
To create the DNS-related Security Policy:
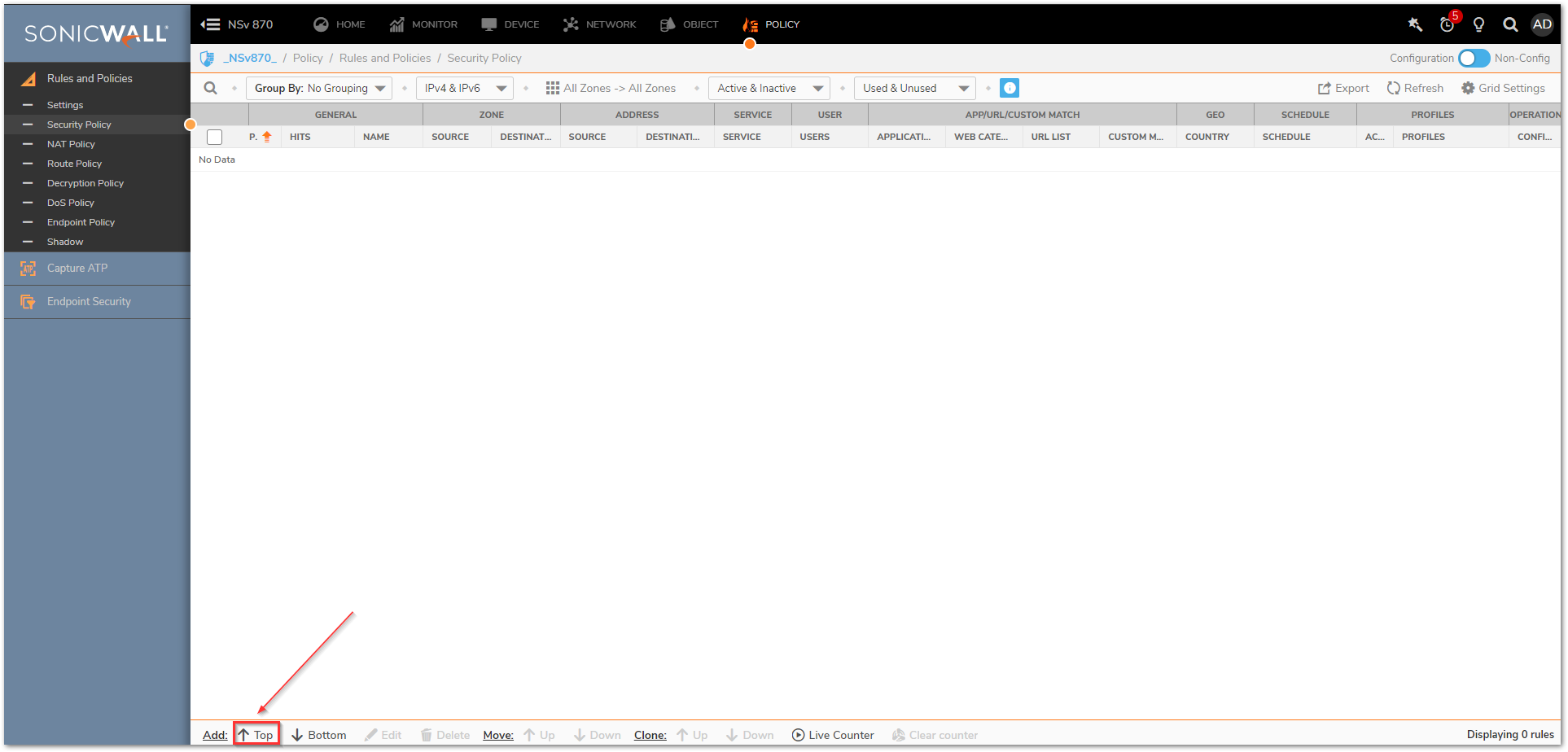
- Navigate to Policy | Rules and Policies | Security policy tab and click on Top at the bottom of the screen. This adds the new Policy at the top of the list. You might need to adjust its priority based on other rules you have.
- Assign a relevant name and in the Source/Destination tab, you can select many fields like source/destination zones, address, services, users and geo-location settings. Select the destination Port/Services as DNS (Name Service).
- Under App/URL/Custom Match tab leave everything on defaults.
- Select the Default Profile as the Security rule action. Make sure that the Action is set to Allow and the policy is in Enable state. Click Save.

 NOTE:This policy can also be created using the DNS protocol application signature, but this example is configured using the services.
NOTE:This policy can also be created using the DNS protocol application signature, but this example is configured using the services.
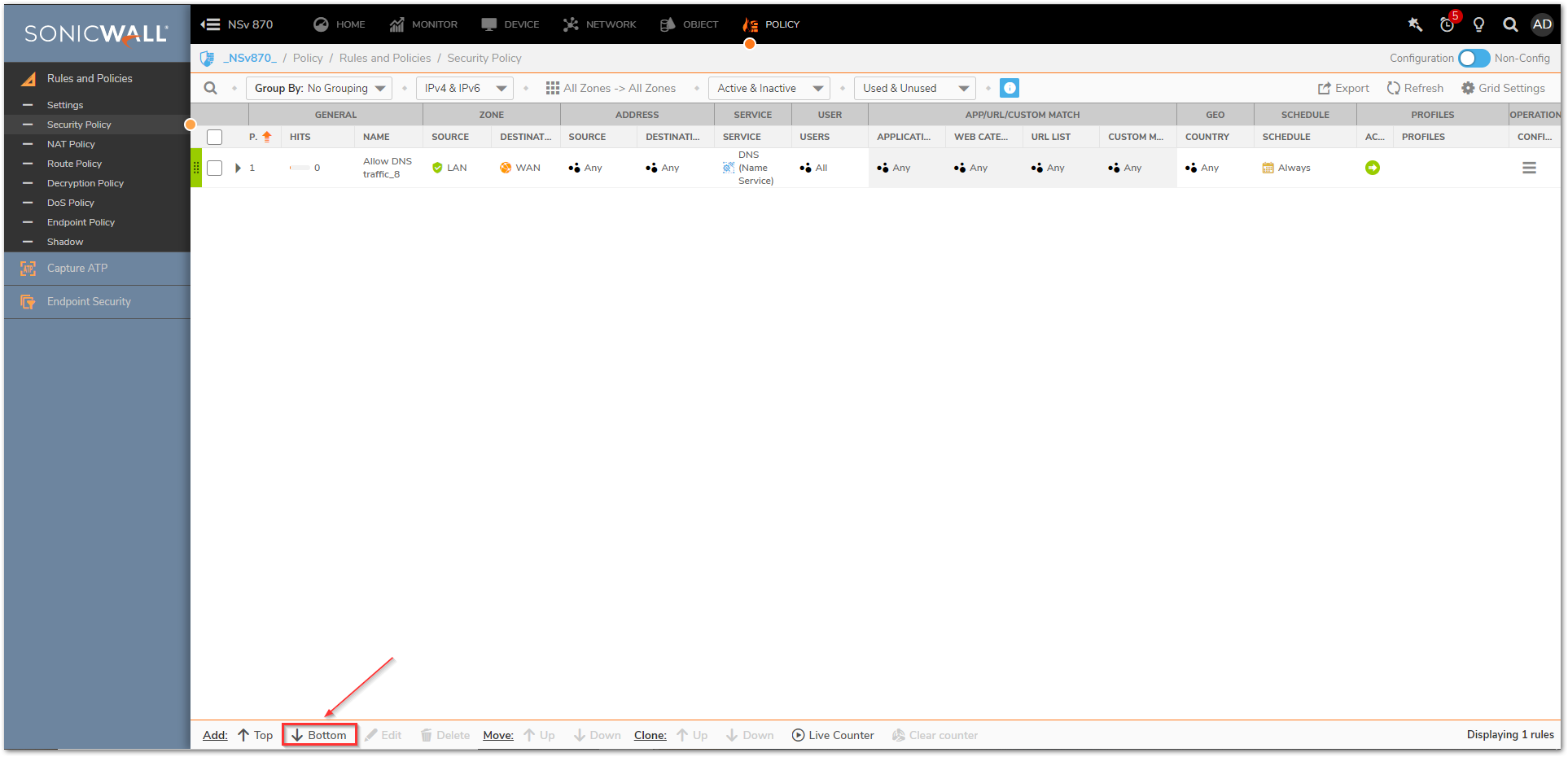
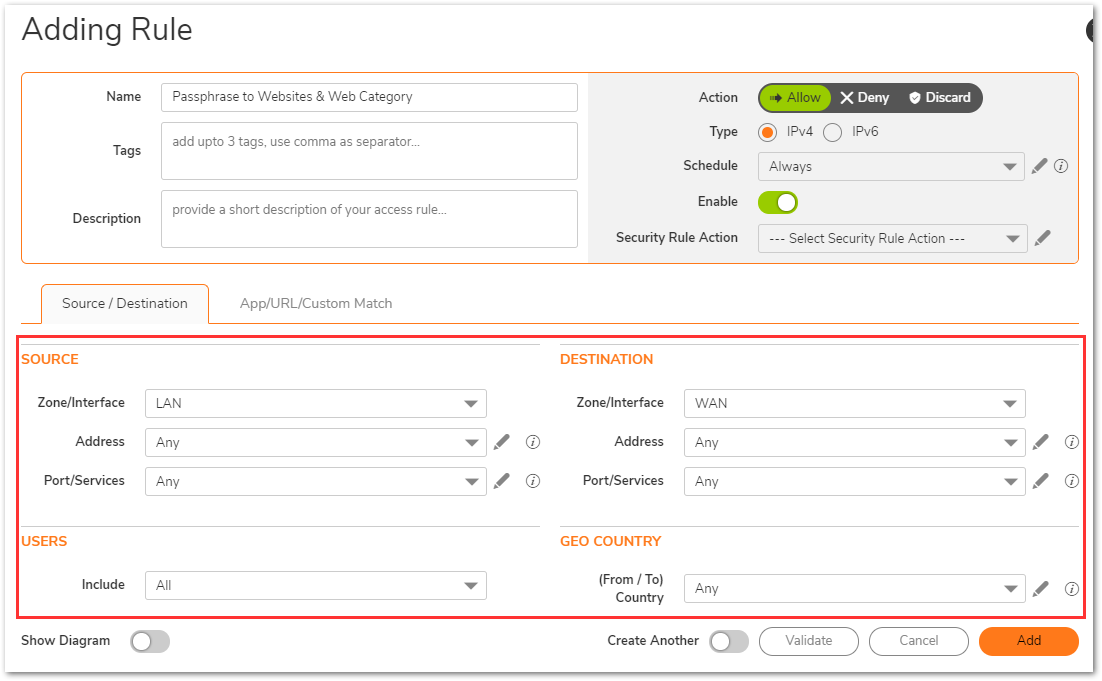
To create the passphrase action to allow websites and web categories related Security Policy
- Navigate to Policy | Rules and Policies | Security policy tab and click on Bottom at the bottom of the screen. This adds the new Policy at the bottom of the list. You might need to adjust its priority based on other rules you have.
- Assign a relevant name and in the Source/Destination tab, you can select many fields like source/destination zones, address, services, users and geo-location settings.
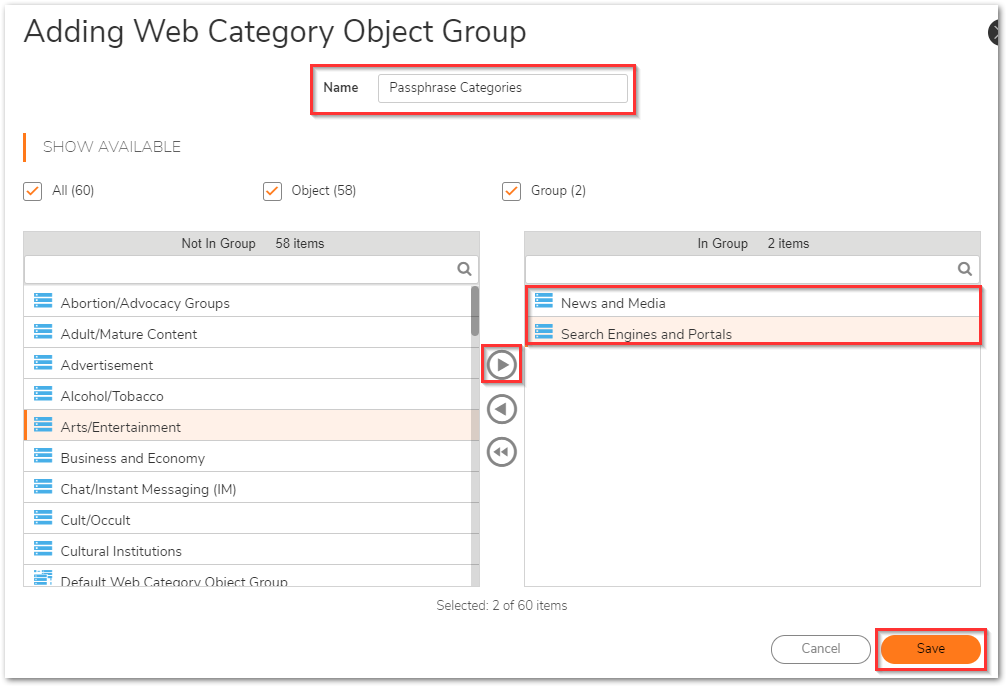
- Under App/URL/Custom Match, set the radio button for 'Match Operation' to OR. Select the pencil icon next to Web Category to add a new Web Category Group.
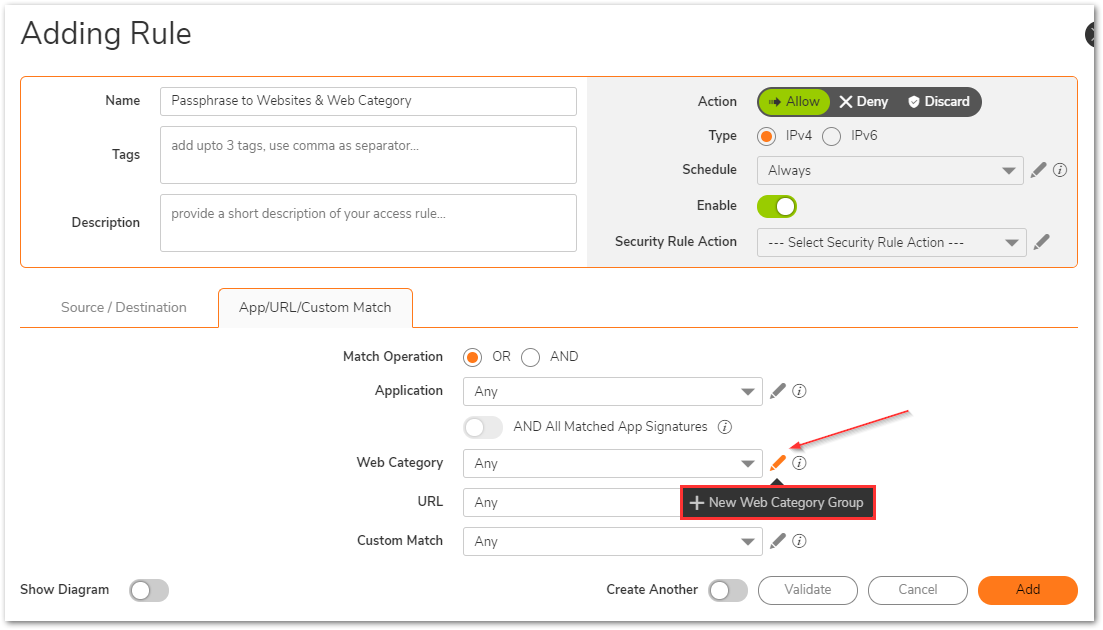
- Give this new Web Category Group a relevant name. Add the required web categories to the right menu using the right arrow and click Save.
- Then, select the pencil icon to add a new URI List object. For more details on creating URI List objects, refer to the KB article, "How to create URI List Objects/Groups on SonicOSX 7.0?"
In this example, we have added indeed.com, monster.com, and naukri.com to the URI list object.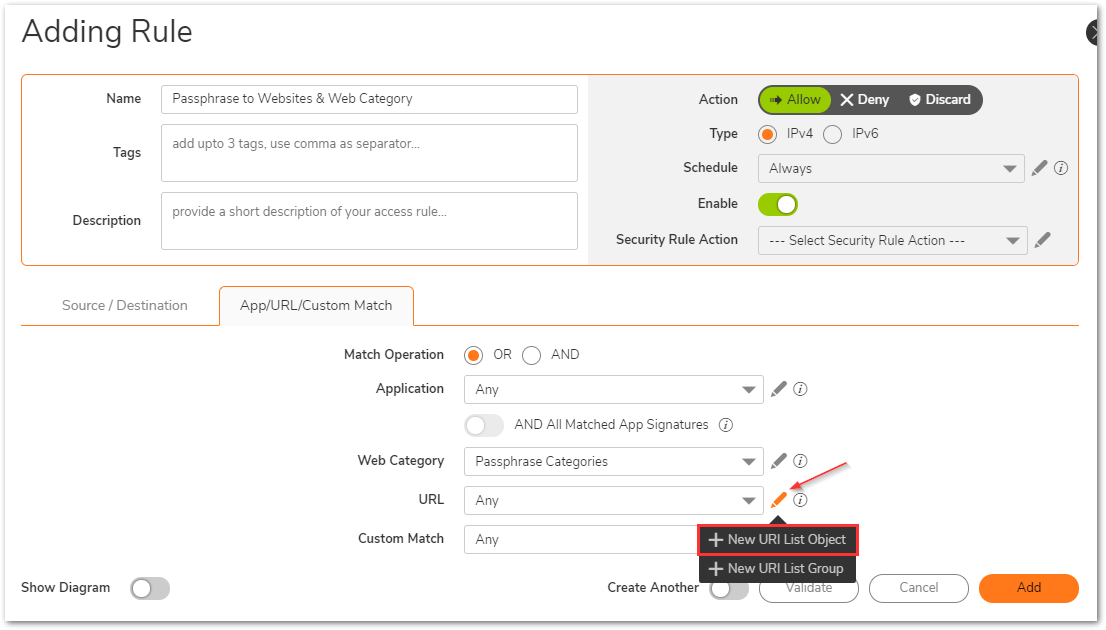
- Under the Security rule action dropdown, click on the pencil icon to create a new Security Action.
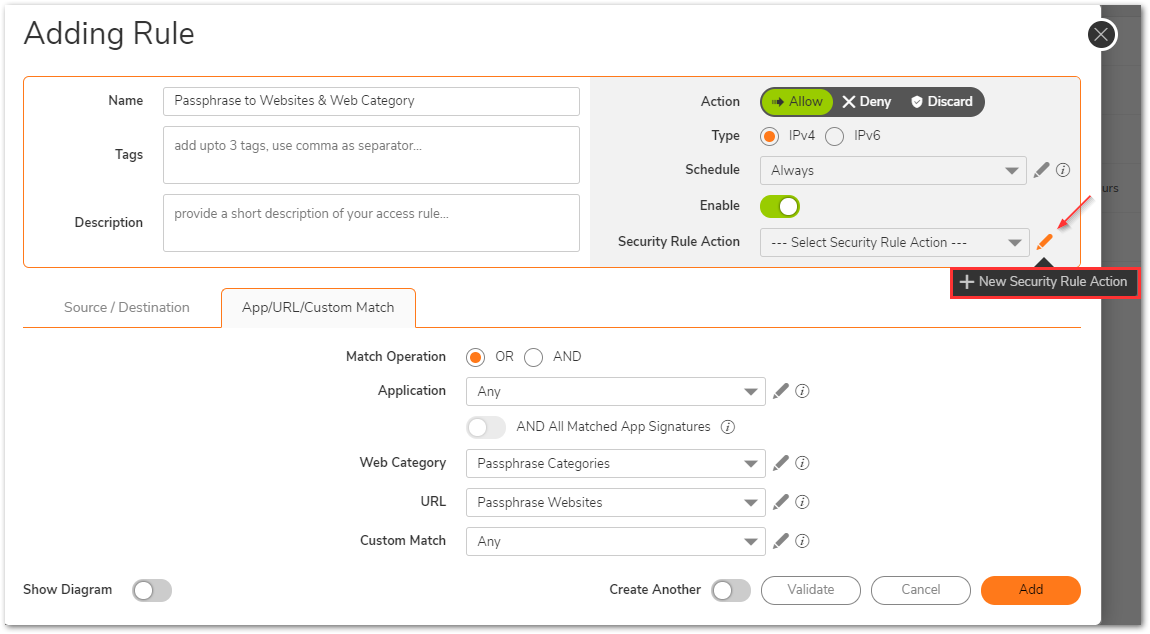
- Give it a relevant name. You can then set several security parameters, but the most important section for this setup is Content Filter. Navigate to the Content Filter tab and move the toggle button to turn on Enable Content Filtering. The Content Filter Action should be set to Passphrase.
- Under the Passphrase tab, you can set the password that the end-user will be required to enter before visiting these websites.
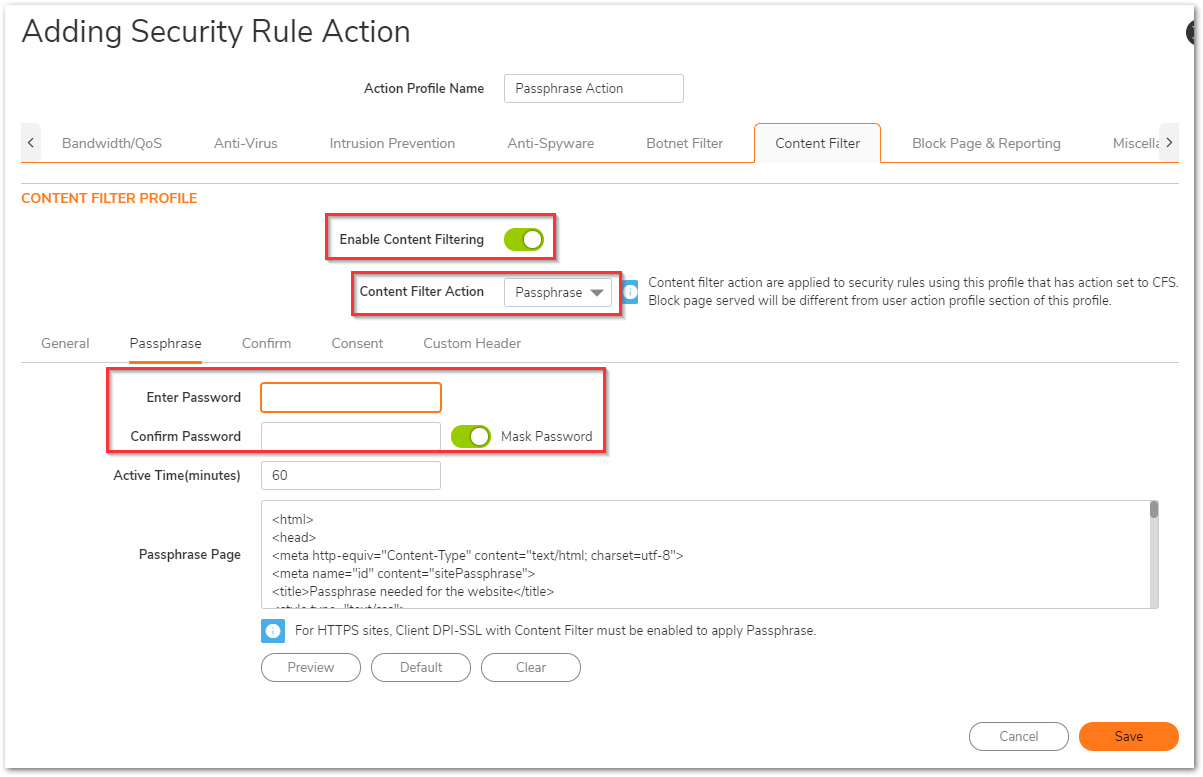
- At this point, you can also make additional changes that will apply to other security features. Click Save when done.
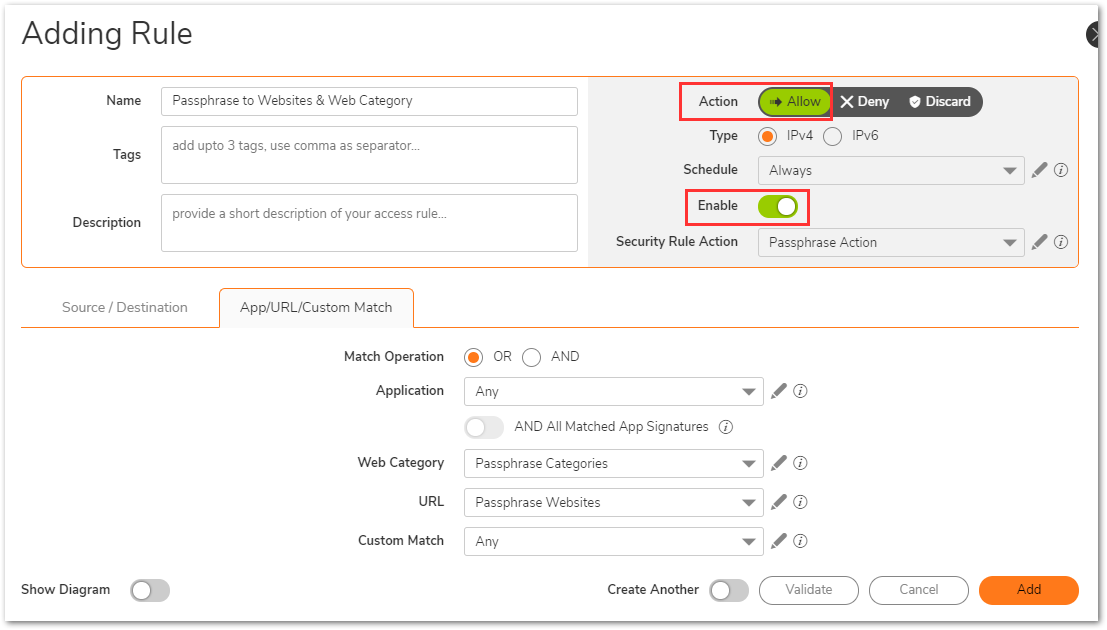
- On the Security Policy, make sure that the Action is set to Allow and the policy is in Enable state. Click Add.
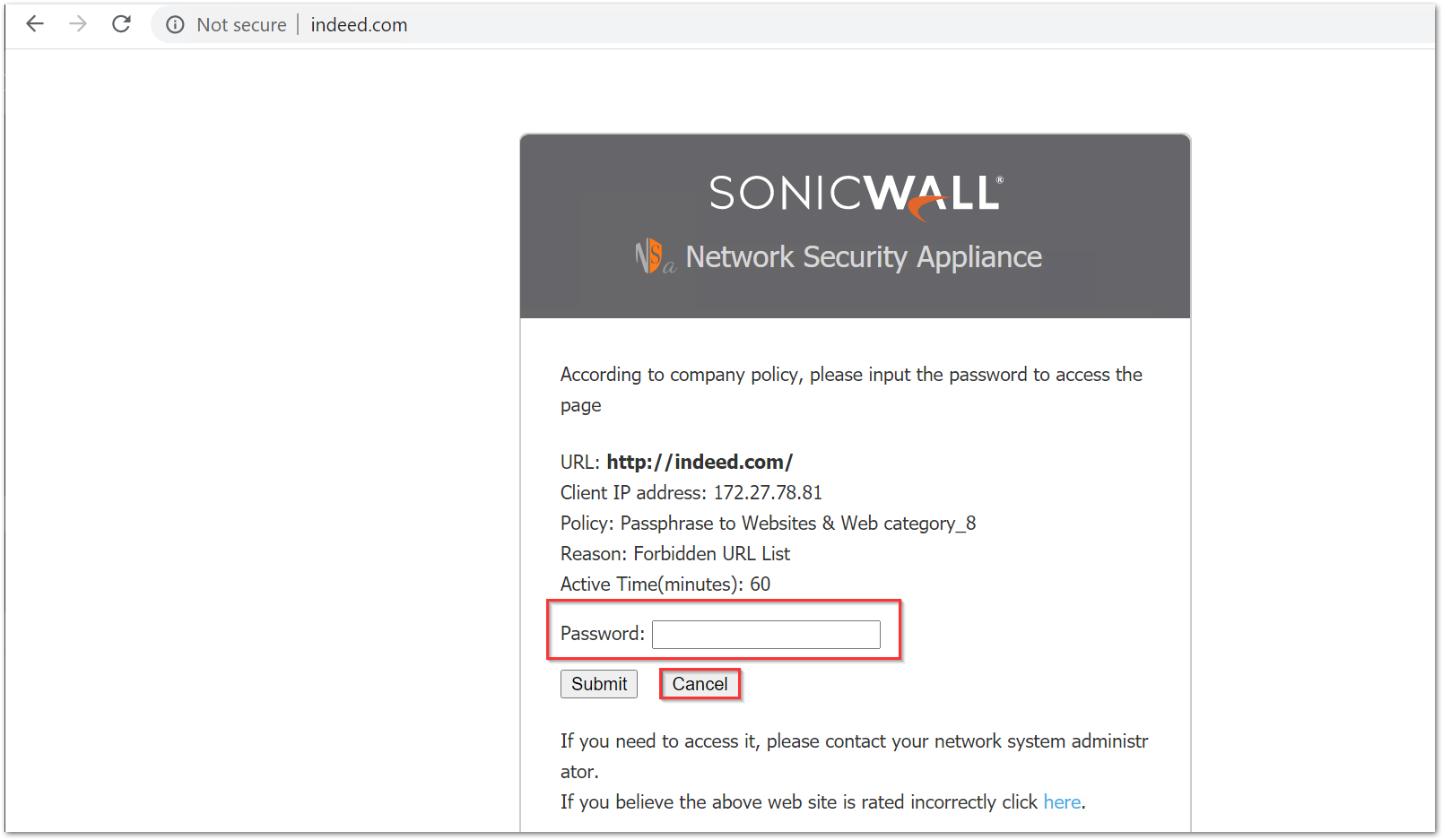
While visiting websites like indeed.com or monster.com, You can enter the password to continue or hit cancel, which will automatically block the page.
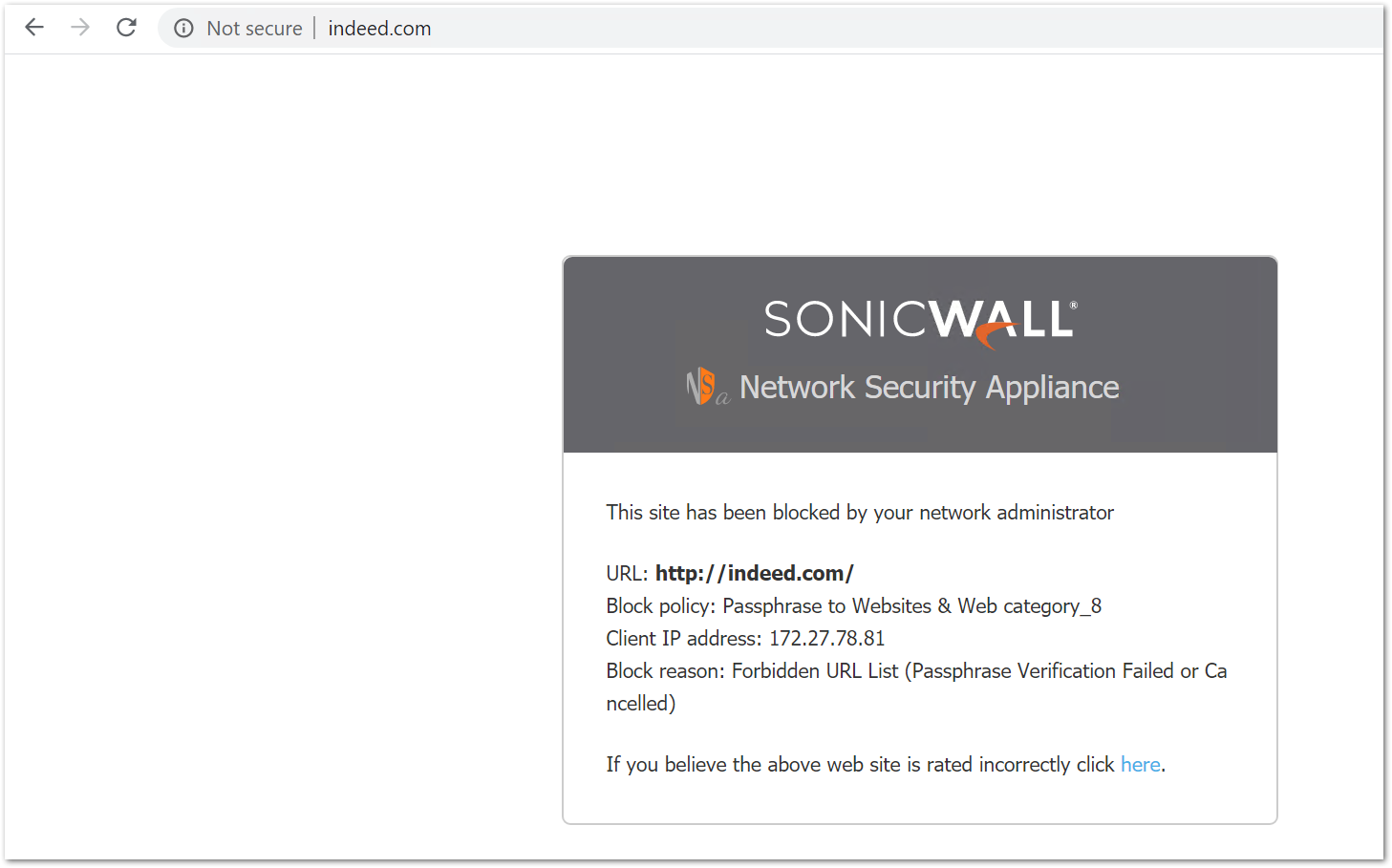
Users will have three chances to enter the right password. If all three enteries are incorrect, the user is blocked automatically.
Related Articles
- How to Block Google QUIC Protocol on SonicOSX 7.0?
- How to block certain Keywords on SonicOSX 7.0?
- How internal Interfaces can obtain Global IPv6 Addresses using DHCPv6 Prefix Delegation






 YES
YES NO
NO