ACRStealer The Silent Golang Threat Behind Credential and Wallet Theft
Overview
This week the SonicWall Capture Labs Threat Research Team analyzed a sample of ACRStealer, a Golang Malware-as-a-Service used by ShieldIO. This uses a binary to sideload a malicious DLL and evade AV products, harvest credentials for browsers and FTP programs, and target a number of crypto-wallets. It is highly evasive and uses a variety of techniques to prevent analysis.
Infection Cycle
Initial file detection shows a basic PE file with an expired signed certificate.
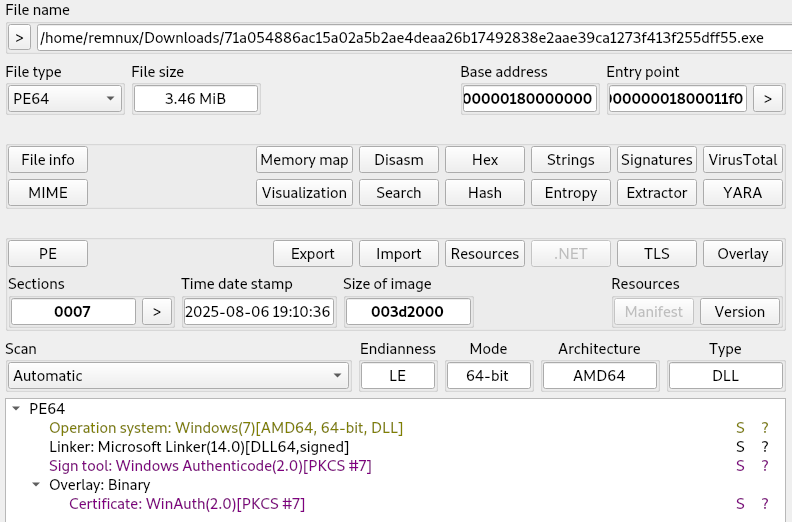
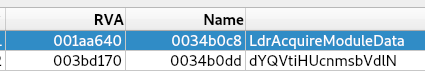
There are two exports, one of which is obfuscated.
Much of the program is obfuscated, and there are two TLS callbacks that are set to prevent active debugging as well as multiple debug checks that intermittently cause analysis software to fail.
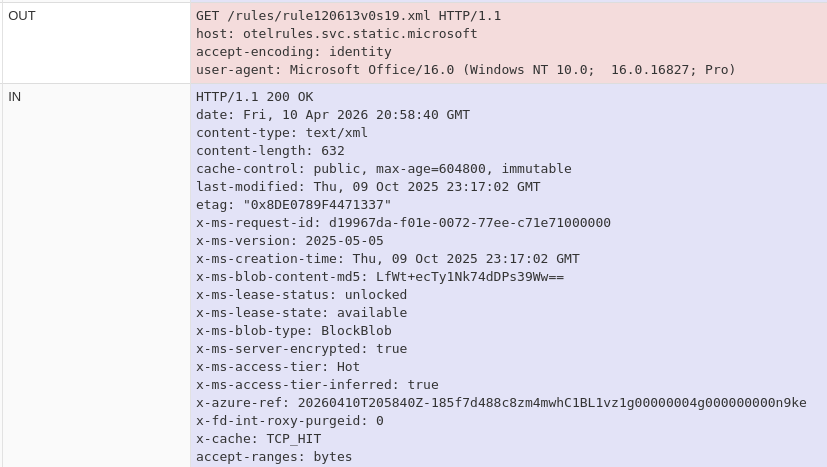
During runtime, the program will use ‘LdrAcquireModuleData’ to sideload malicious code into the rundll32 process and reach out to ‘https://cw.compactedtightness.cfd/VRqah_-.XZLecEZbgJA3G_Y@-vi8Abt_SWFoR’ to check in with C2 and update commands or upload harvested data. The following programs are targeted by ACRStealer when the malware has loaded:
The malware uses WMIC commands used to determine the environment:
- SELECT Family,VirtualizationFirmwareEnabled FROM Win32_Processor
- SELECT HypervisorPresent FROM Win32_ComputerSystem
This is followed by further checks for the following virtual services/programs:
- QEMU-GA.EXE
- KLIF.SYS (Kaspersky Lab Intruder Filter)
- KLDISK.SYS (Virtual Windows driver)
- KLHK.SYS (Kaspersky Hypervisor)
- KNEPS.SYS (Kaspersky AV)
- REGISTRY\MACHINE\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALLAGENT.EXE
- ARUNAGENT
- ANYRUN
- VBOXSERVICE
- VBOXTRAY
Debug Checks for anti-analysis and evasion:
- HideFromDebugger
- DebugPort
- DebugObjectHandle
- Rdtscp
A keylogger is set up using the following:
- GetRawInputBuffer
- GetRawInputData
FTP targets for credentials and potentially files:
| BitKinex | FTP Now | Estsoft\ALFTP | NppFTP |
| BlazeFtp | FTPBox | GHISLER | UltraFXP |
| Conceptworld\Notezilla | FTPGetter | GoFTP |
|
| DeluxeFTP | FTPInfo | NovaFTP |
|
Browsers:
- Chrome
- Firefox
- Cyberfox
- Edge
Password Managers:
- NordPass
- Bitwarden
- 1Password
Sonicwall Protection
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: ACRStealer.Go (Trojan)
This threat is also detected by SonicWall Capture ATP with RTDMI™ and the Capture Client endpoint solution.
IOCs
71a054886ac15a02a5b2ae4deaa26b17492838e2aae39ca1273f413f255dff55
Share This Article
An Article By
An Article By
Security News
Security News