-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
Using DNS Sinkhole feature to block DNS queries



Description
Firewall can block DNS queries to specific domains through its feature of DNS Sinkhole. The important step to achieve this requirement is to use split DNS tunneling so that firewall can receive the DNS queries at its end and take action rather than forwarding to internal or public DNS servers.
Resolution
 EXAMPLE: Lets take "yahoo.com" domain into consideration and we will block the DNS query of this domain via firewall with client PC configured with internal or public DNS servers.
EXAMPLE: Lets take "yahoo.com" domain into consideration and we will block the DNS query of this domain via firewall with client PC configured with internal or public DNS servers.
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
Configure Firewall in split tunnel and point the dns query for the domain towards firewall.
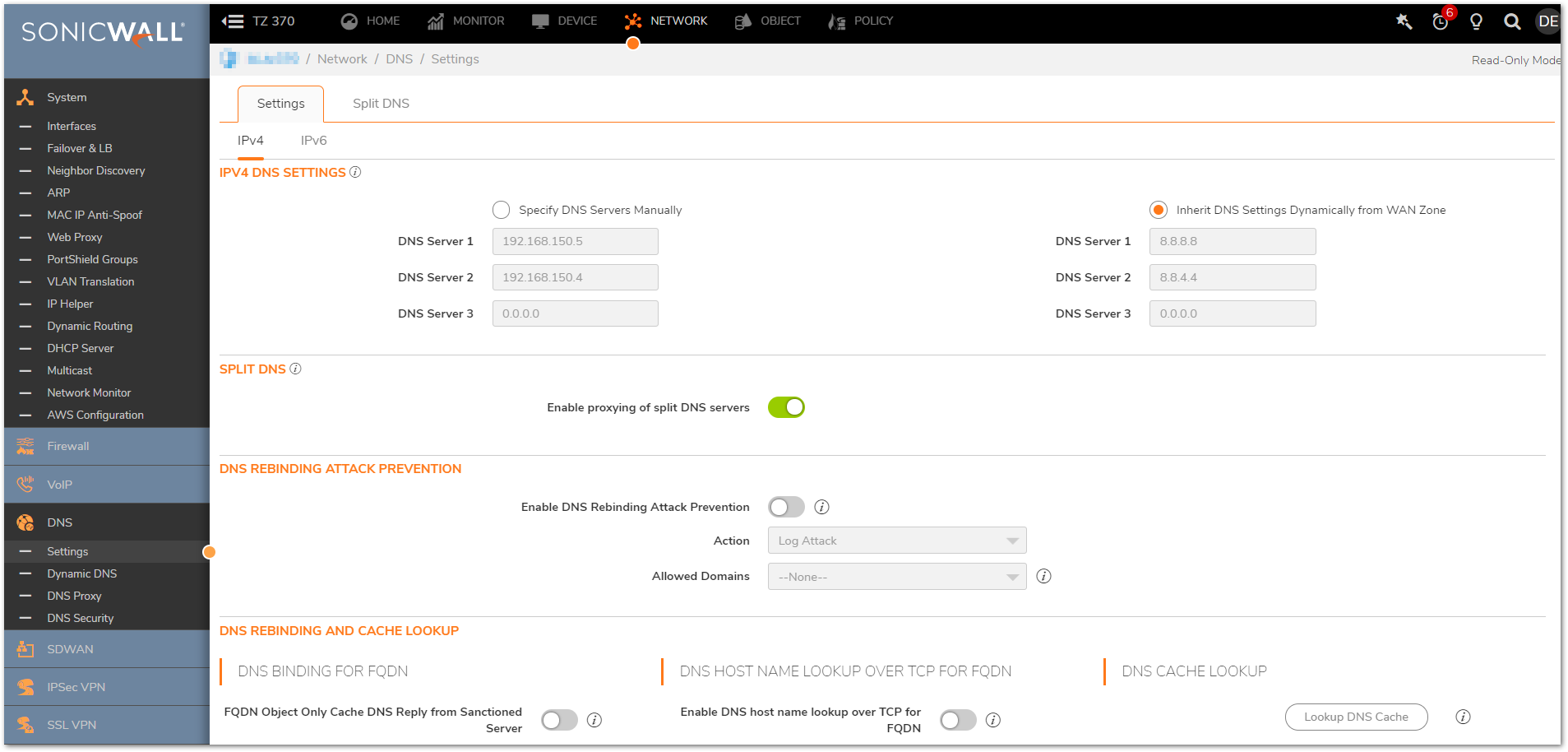
- To configure the split tunnel, navigate to Network|DNS| Settings.
- Enable the checkbox for IPv4 Split DNS which states Enable proxying of split DNS servers.
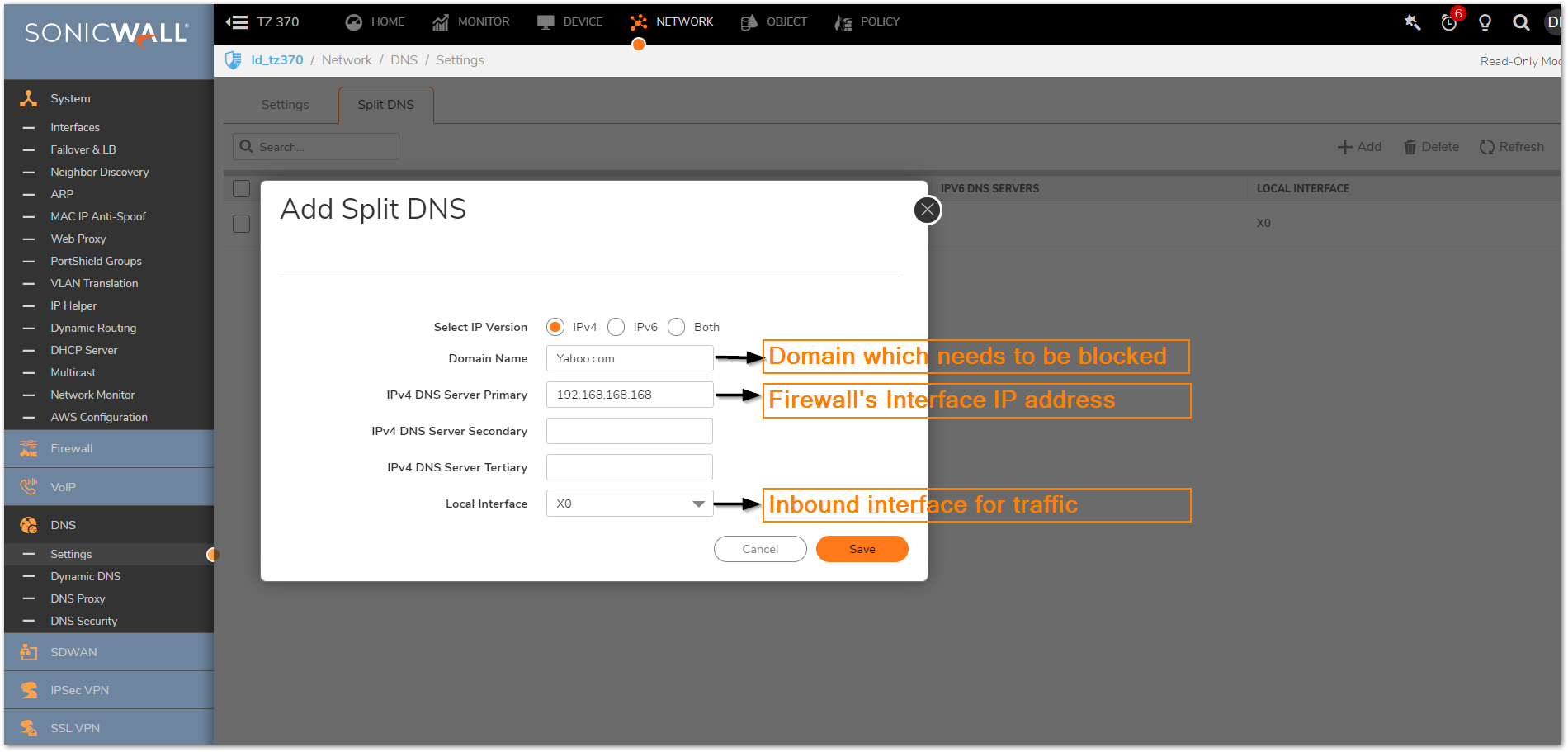
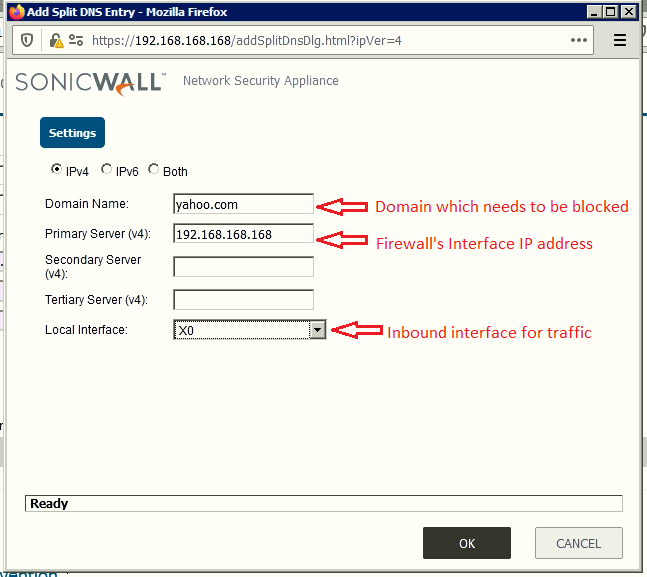
To configure the domain which you want to block and point its dns query towards firewall interface IP address, navigate to Network | DNS | Settings | Split DNS and click Add.
Enabling DNS Sinkhole and configuring it
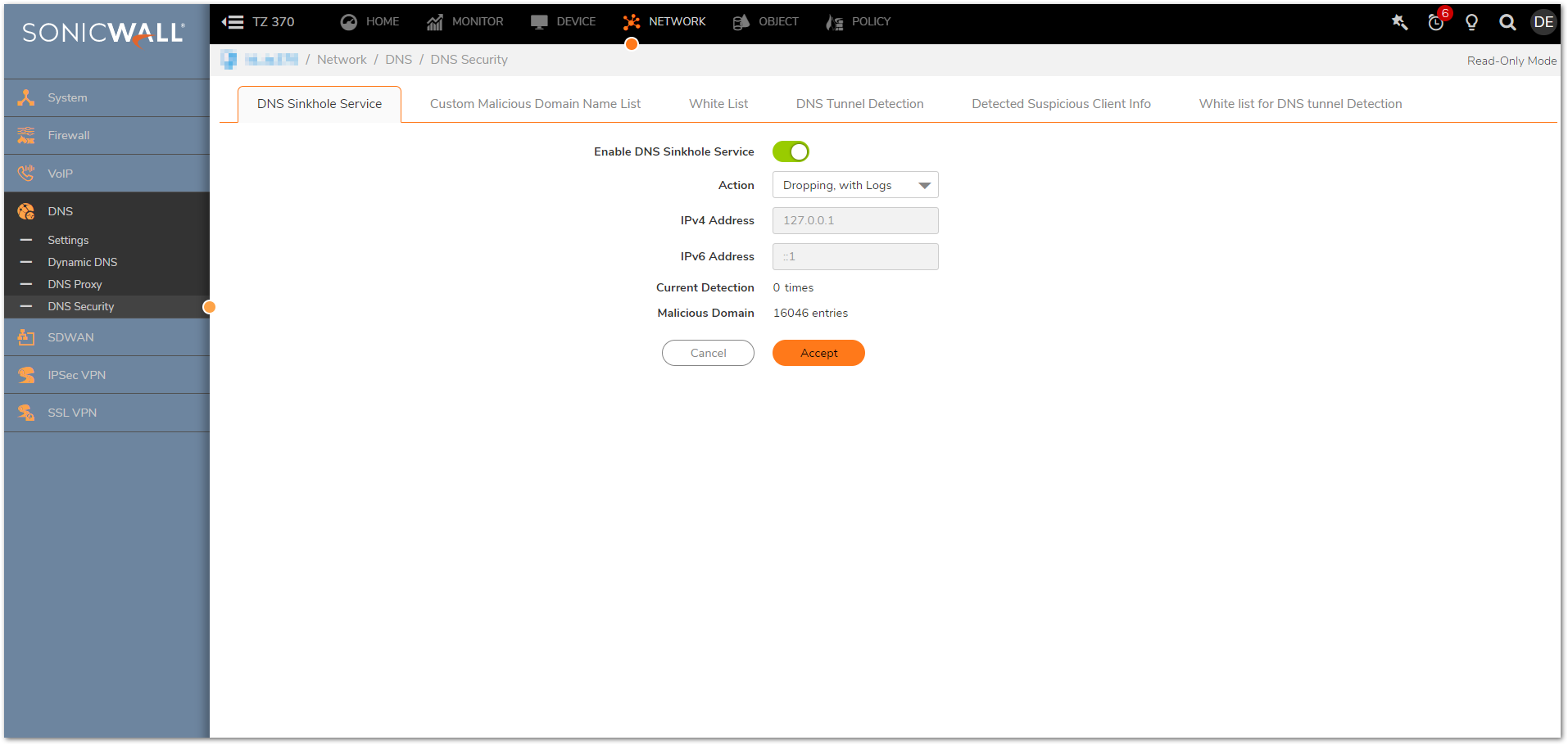
- Navigate to Network |DNS | DNS Security | DNS Sinkhole Service.
- Enable the option Enable DNS Sinkhole Service.
- Select one of the available three options from Action dropdown.
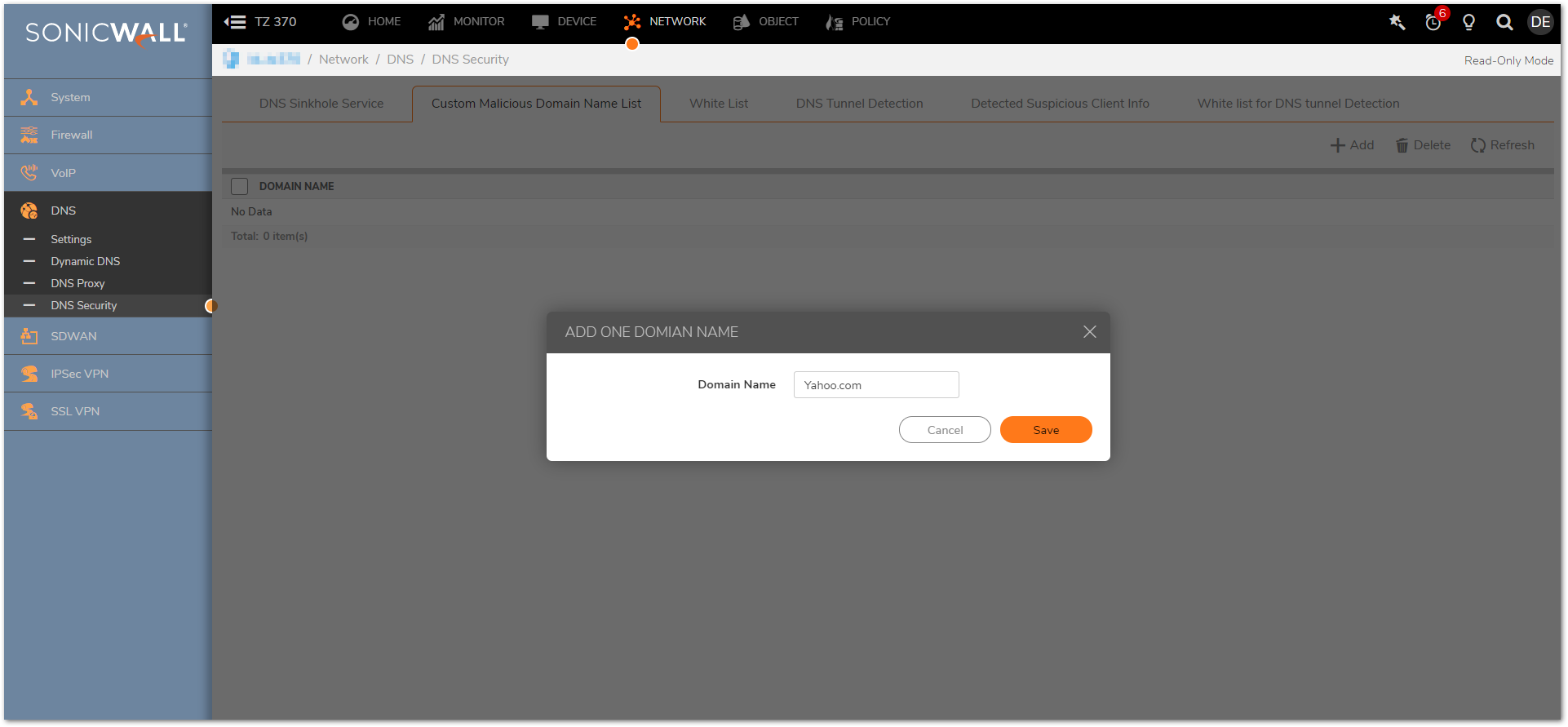
- Navigate to Custom Malicious Domain Name List and click Add. Enter domain name Yahoo.com and click Save.
Resolution for SonicOS 6.5
This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware.
Configure Firewall in split tunnel and point the dns query for the domain towards firewall.
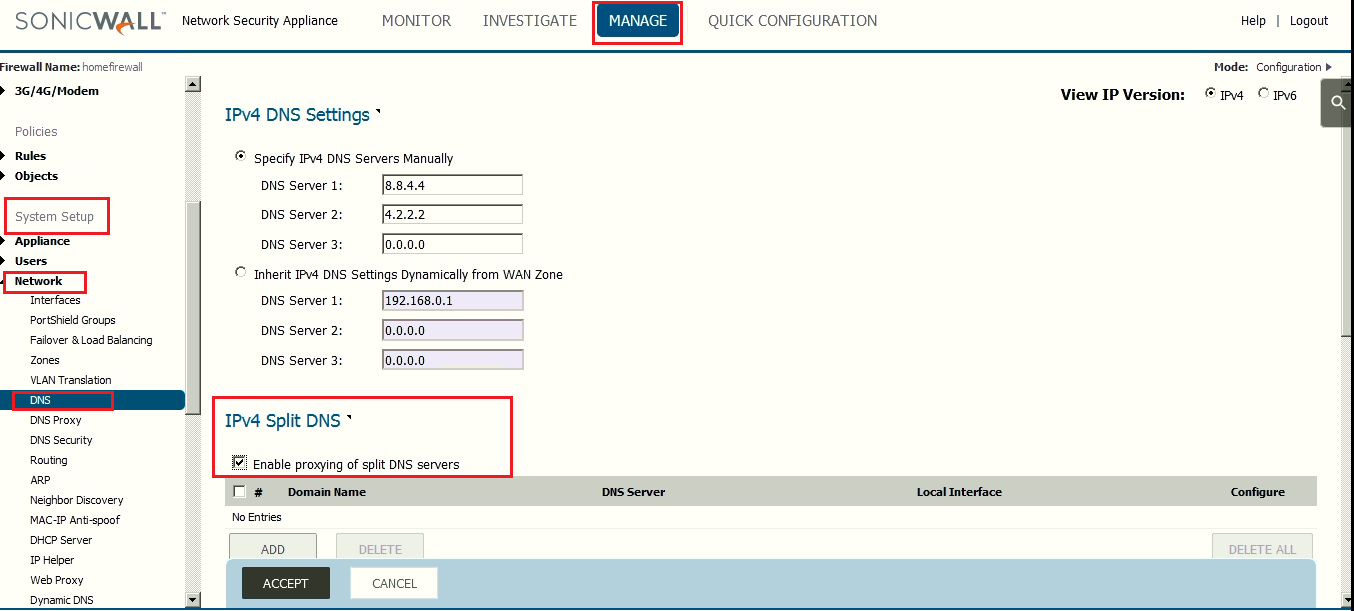
- To configure the split tunnel, navigate to Manage |System Setup | Nnetwork | DNS .
- Enable the checkbox for IPv4 Split DNS which states Enable proxying of split DNS servers.
- Configure the domain which you want to block and point its dns query towards firewall interface IP address.
Enabling DNS Sinkhole and configuring it
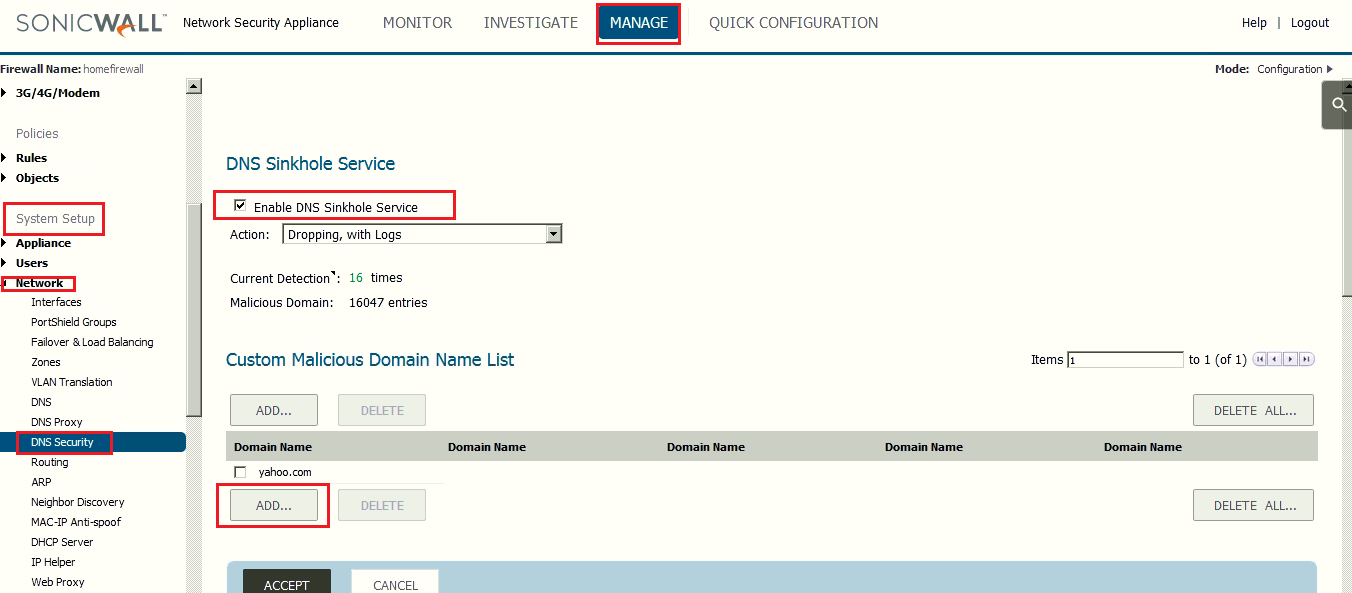
- Navigate to Manage |System Setup | Nnetwork | DNS Security.
- Enable the option Enable DNS Sinkhole Service.
- Select one of the available three options.
- Click ADD and enter the domain yahoo.com into the Custom Malicious Domain Name List.
How to Test :
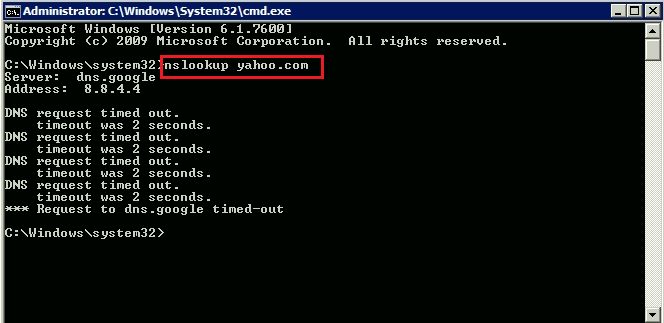
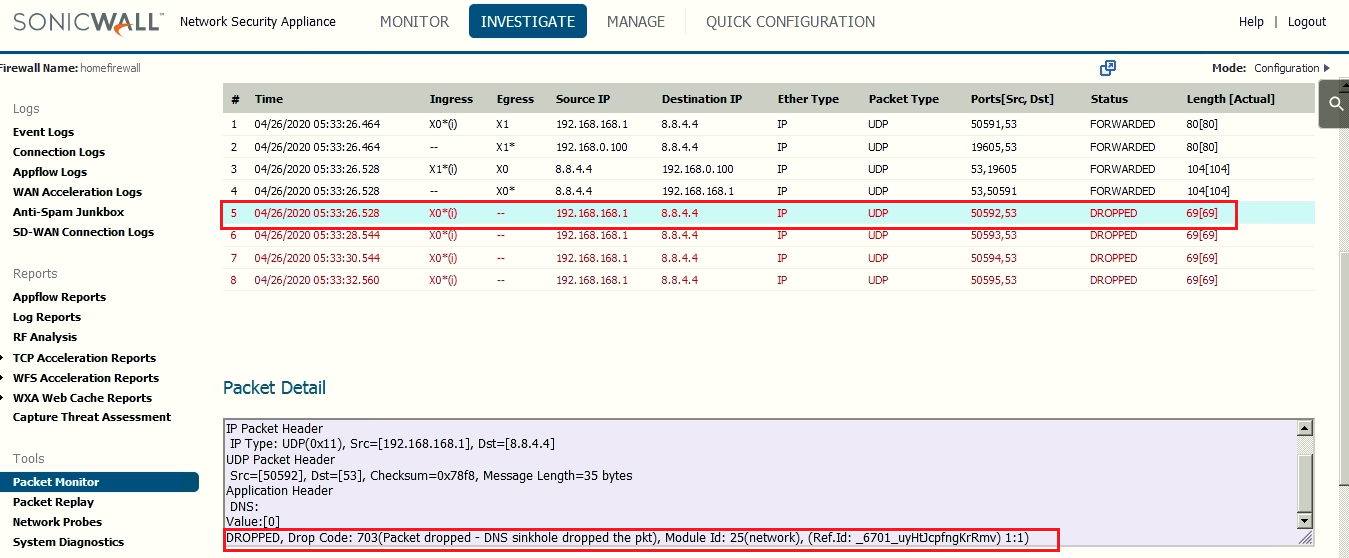
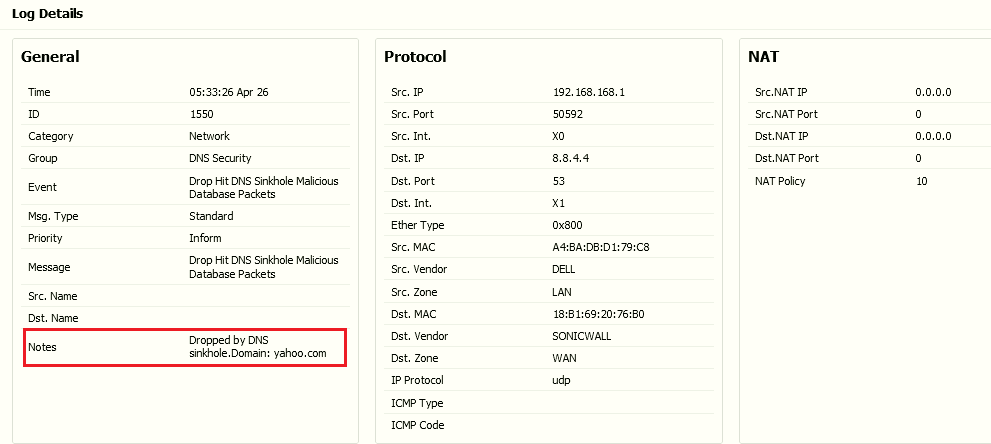
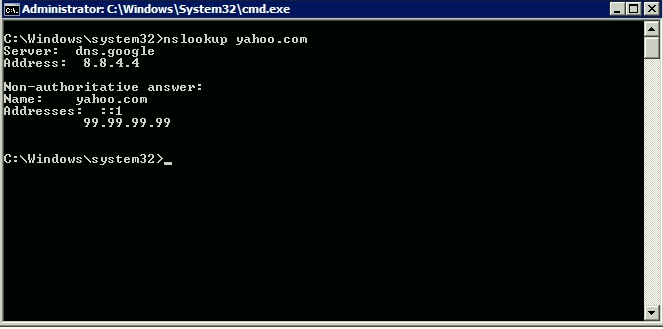
- Run nslookup command to generate the DNS query from a PC behind X0 network of SonicWall and check the SonicWall Logs and Packet monitor with UDP 53 traffic as :
 NOTE: With DNS Sinkhole Service action selected as 'Dropping, with DNS reply of forged IP', we need to configure the forged or masked IP address so that firewall can return the dns query with that IP.
NOTE: With DNS Sinkhole Service action selected as 'Dropping, with DNS reply of forged IP', we need to configure the forged or masked IP address so that firewall can return the dns query with that IP.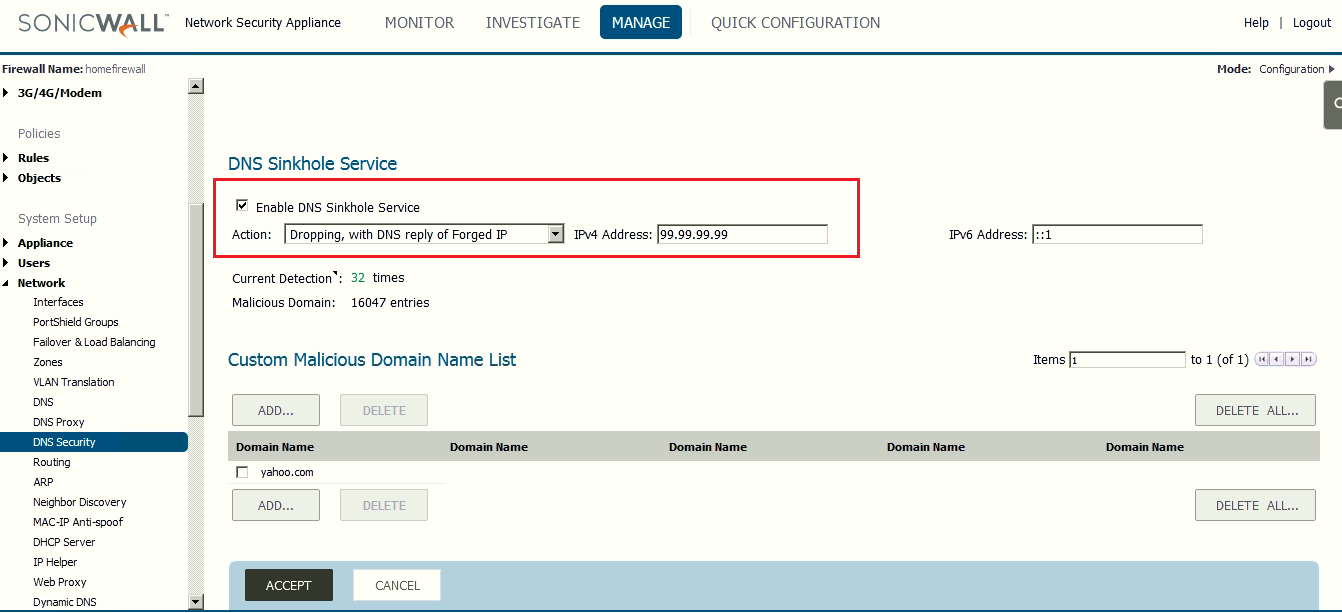
 TIP: The above requirement can also be achieved by creating FQDN object of "yahoo.com" and blocking the DNS (Name Service) through access-rule, but it is always recommended to limit the usage of FQDN objects to avoid unnecessary CPU spikes in firewall.
TIP: The above requirement can also be achieved by creating FQDN object of "yahoo.com" and blocking the DNS (Name Service) through access-rule, but it is always recommended to limit the usage of FQDN objects to avoid unnecessary CPU spikes in firewall.
Related Articles
- Error:"Invalid API Argument" when modifying the access rules
- Cysurance Partner FAQ
- Configure probe monitoring for WAN Failover and Loadbalancing - SonicWall UTM
Categories
- Firewalls > NSa Series > Networking
- Firewalls > NSv Series > Networking
- Firewalls > SonicWall NSA Series > Networking
- Firewalls > SonicWall SuperMassive 9000 Series > Networking
- Firewalls > TZ Series > Networking






 YES
YES NO
NO