-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
Overview of Personal Device Authorization feature in SMA 8.5



Description
Resolution
Enable PDA feature
To enable PDA feature, login the management interface and navigate to Device management > Settings > Register Settings, select Enforce Device Register, then click Accept button to save the changes.
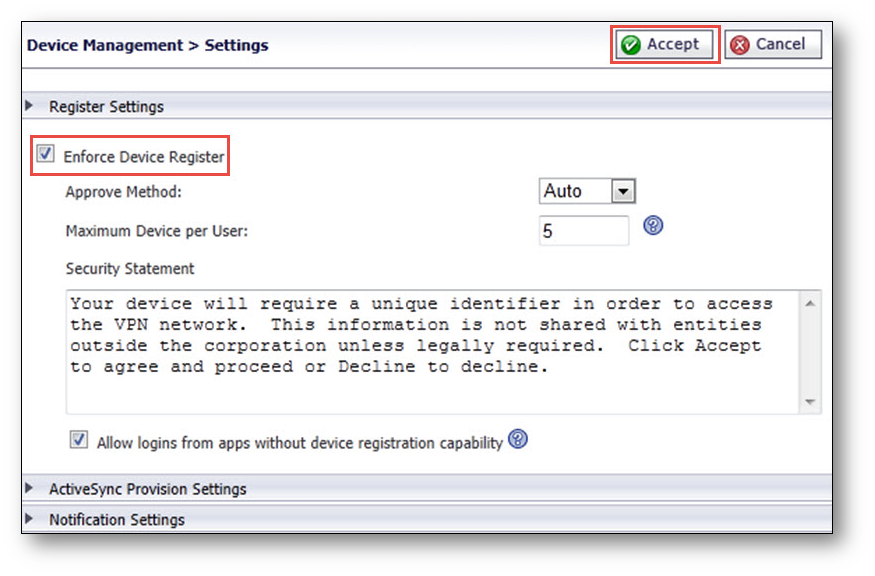
There are two options under Approve Method: Auto and Manual. The Manual mode means that each device first registered by one user is set to the “pending” or “wait for the administrator to approve” status. The Auto mode matches the registered devices with the device policies created by you. The device takes on the policies defined action when a policy is matched. If no matches are found, the device is set as approved by the system. The Auto mode can reduce your workload.
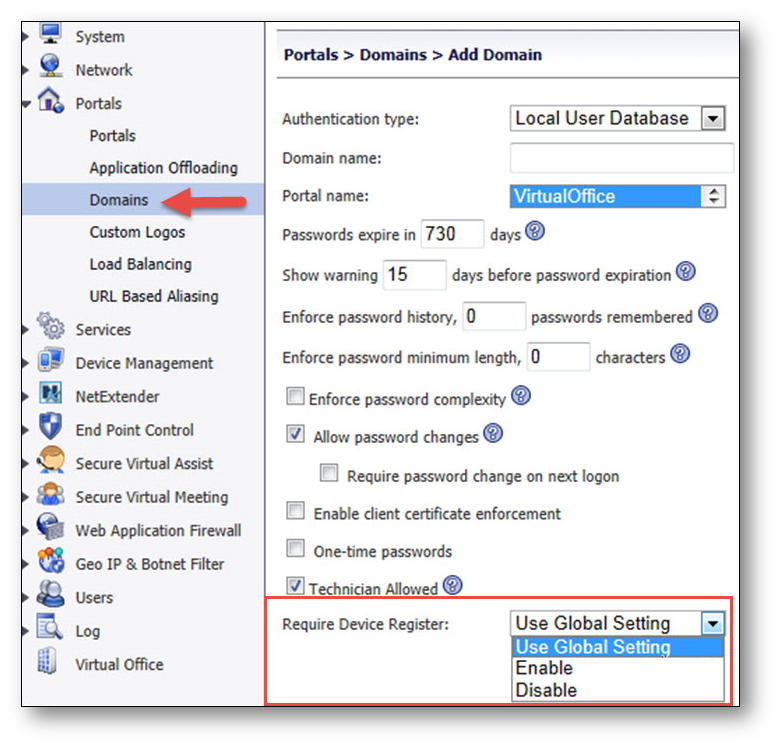
Note: You can customize register settings in domain level as well. And the domain level settings have a high priority than global settings.
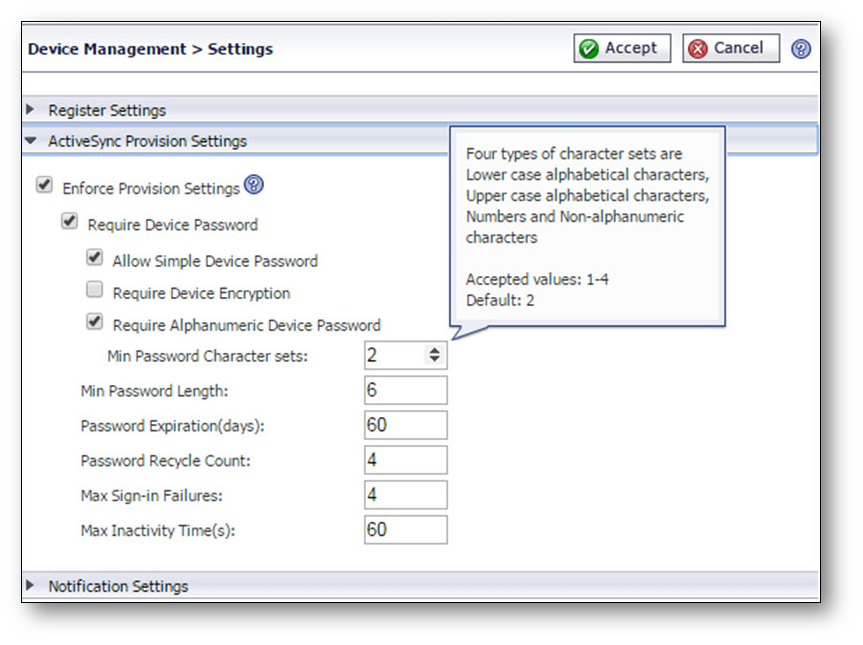
ActiveSync Provision Settings
ActiveSync Provision Settings can be applied specifically to ActiveSync devices. Provision settings can override the settings on a backend Exchange server. Mobile devices are not able to sync when the Provision settings are not satisfied.
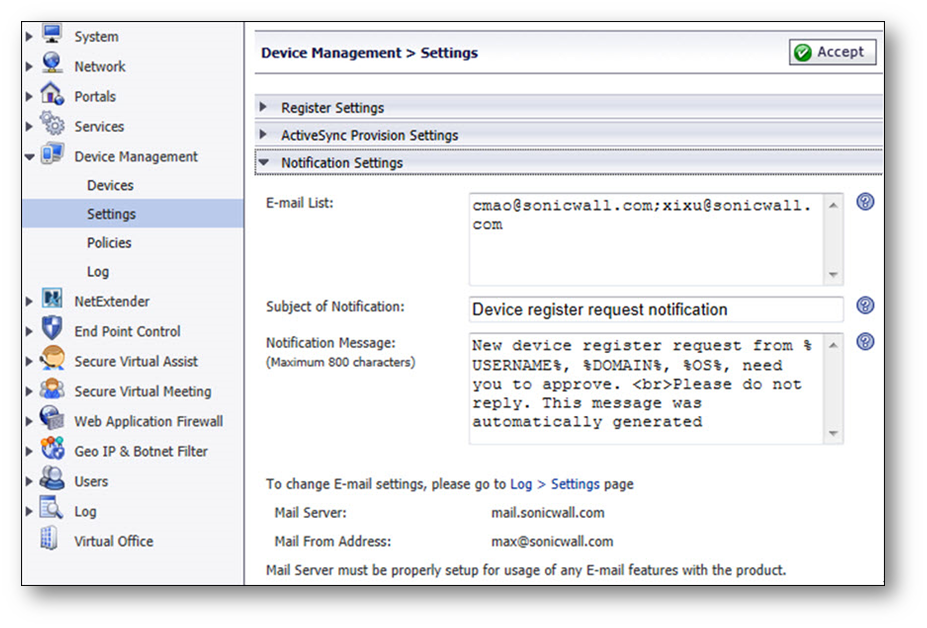
Notification Settings
You can list a set of email addresses here. When a new registration request arrives, an email notification is sent to these addresses notifying the recipients to handle the request. The notification email’s Subject and Message can be customized.
Policies
Device policies are applied to the situation when the approve method is set to Auto. This can reduce your workload.
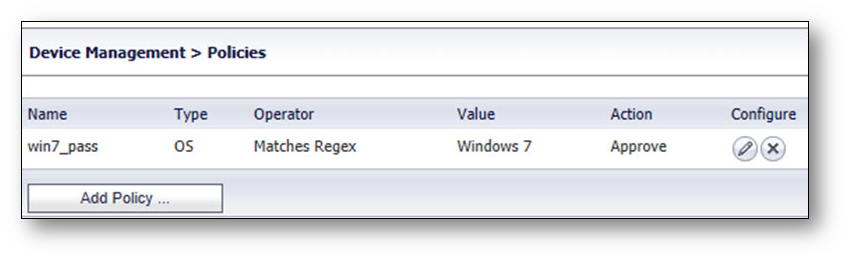
There are two types of device policies: Device Id and OS. The Device Id has a higher priority than OS by default.
The Action option has three choices: Pending, Approve, and Reject. The device takes on the defined action when it matches the policies.


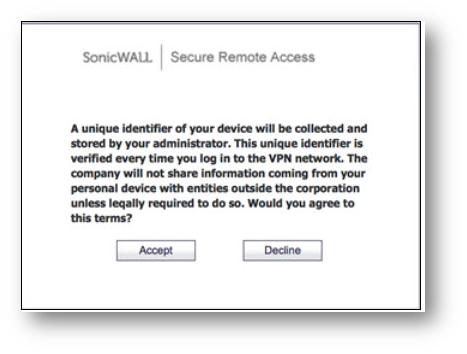
PDA for portal login
1, Upon first login, a security statement pops up after login authentication.
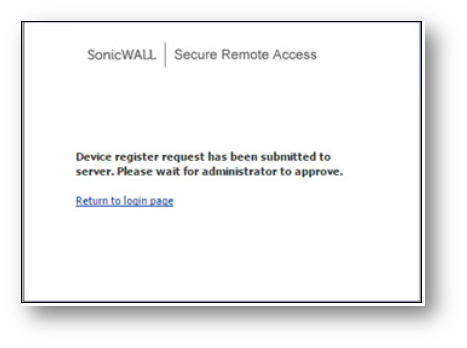
2, You would not be allowed access even if you accept to register your device when the device approval method is set to “Manual.” You must still wait for an administrator to approve your device.
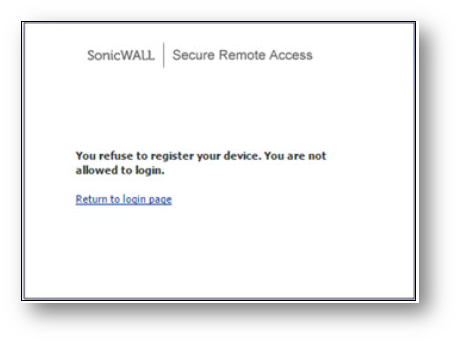
3, However, you would not be allowed access if you have refused to register your device.
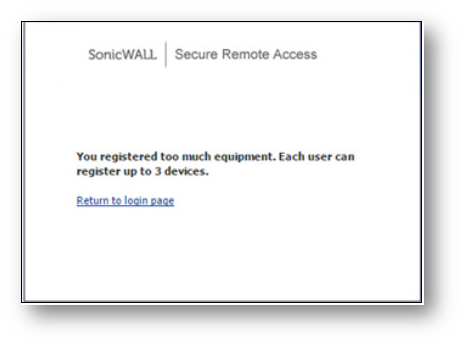
4, Also, you would not be allowed to register your device or gain access for it if you had already registered three devices.
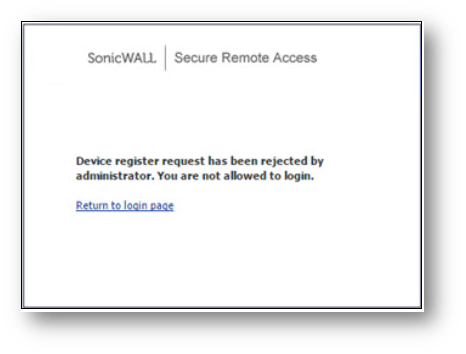
5, Finally, you also cannot register your device or gain access for it if your “register device” request has been rejected by the administrator.
PDA for SMA Clients
Clients including Mobile Connect, NetExtender, Virtual Assist, and Virtual Meeting are currently not supported for the PDA feature in the RTQA build (no need to support “guest login”). Clients will be supported in a future build.
Related Articles
- How to Set Timeout for Inactive Tunnel Connections
- Commands for silent installation of NetExtender via CMD line
- Users on Netextender 10.3.0 version failing to connect with the following error message " Cannot get a response from the server "






 YES
YES NO
NO