-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
Integrating SonicWall Capture Client with Stellar Cyber's OpenXDR platform



Description
Stellar Cyber’s Open XDR is a single open security operations platform for detection, investigation and automatic response by ingesting, normalizing, enriching, analyzing and correlating data from hundreds of tools, including SonicWall's Next-gen Firewall and Capture Client. In this article, we describe how to integrate Stellar Cyber's Open XDR with SonicWall Capture Client.
Resolution
A SonicWall Capture Client connector allows you to disconnect host, initiate scan, restart machine, or shut down using Starlight (as long as those hosts are managed by SonicWall Capture), and ingest SonicWall Capture Client logs, discover assets, and see vulnerabilities.
Adding a SonicWall Capture Connector
There are two pre-requisite actions to be taken to sccessfully integrate with Stellar Cyber:
- You will need to use an Administrator user in the Capture Client tenant. We recommend creating a dedicated user account to audit activity for this integration. For instructions on how to do create a new user in Capture Client, see this KB article
- You will need to keep the Capture Client Tenant ID handy - this is available from the Tenant Settings of your Tenant
To add a SonicWall Capture connector in Starlight:
1. Log in to Starlight.
2. Click Collect | Connectors. The Connector Overview appears.

3. Click . The General tab of the Add Connector screen appears. The information on this tab cannot be changed after you add the connector.
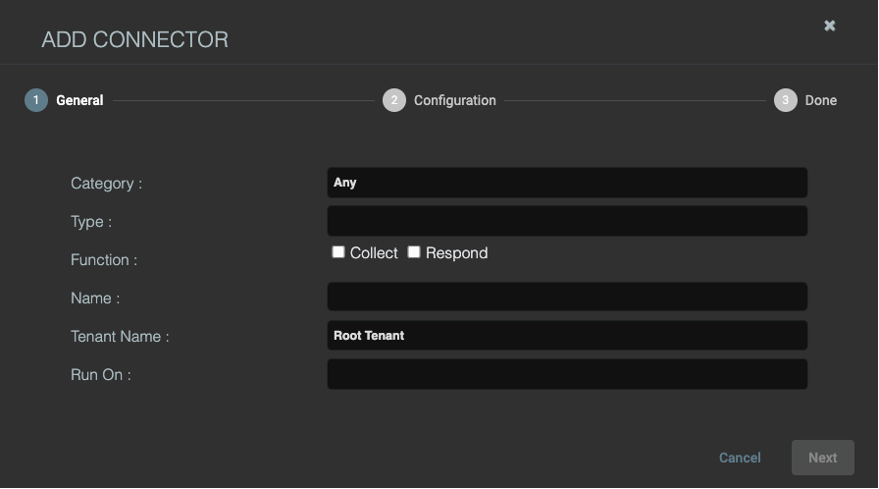
4. Choose Endpoint Security from the Category drop-down.
5. Choose SonicWall Capture Client from the Type drop-down.
6. Choose the Function: Collect to collect logs; Respond to enable endpoint actions.
7. Enter a Name. This field is required, and does not accept multibyte characters.
8. Choose a Tenant Name. The Interflow records created by this connector include this tenant name.
9. Choose the device to run the connector on.
10. Click Next. The Configuration tab appears.
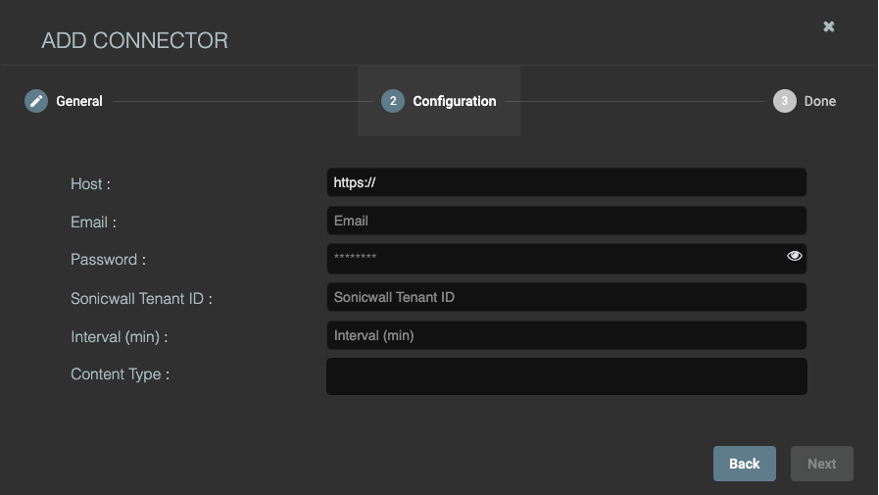
11. Enter the Host - captureclient.sonicwall.com
12. Enter the Email address of the SonicWall Capture Client user account you want to use for the integration
13. Enter the Password for the SonicWall Capture Client user account you want to use for the integration
14. Enter the Sonicwall Capture Client Tenant ID if you chose Collect.
15. Enter the Interval (min) if you chose Collect. This is how often Starlight collects the information.
16. Enter the Content Type that you want to collect, if you chose Collect.
17. Click Next. The final confirmation tab appears.
18. Click Submit. A dialog box appears, prompting you to add the connector to the default data analyzer profile.
19. Click OK to add it, or Cancel to leave it out of the default profile. A connector must be included in a data analyzer profile. If you leave it out of the default profile, you must add it to another profile.
20. The Connector Overview appears.
The new connector is immediately active.
Testing the Connector
To test the connector:
1. Click Collect | Connectors. The Connector Overview appears.
2. Click Test for the connector you want to test. The test runs immediately.
Starlight conducts a basic connectivity test for the connector. A successful test indicates that you entered all of the connector information correctly.
Verifying Ingestion
To verify ingestion:
1. Click Investigate | Threat Hunting. The Interflow Search tab appears.
2. Change the Index to Syslog if you chose the log or threat content type. The table immediately updates to show ingested Interflow records.
3. Change the Index to Assets if you chose the host content type. The table immediately updates to show ingested Interflow records. Also, hosts discovered through this connector show SonicWall Capture Client as a data source.
4. Change the Index to Linux Events if you chose the vulnerabilities content type. The table immediately updates to show ingested Interflow records.
5. Change the Index to Scans if you chose the atp content type. The table immediately updates to show ingested Interflow records.
Related Articles
- SentinelOne agent command line tool
- Capture Client Agent Return Codes - Phase 1
- Configure Email and Notification(Alerts) in Capture Client for Tenants






 YES
YES NO
NO