-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
How to Capture Traffic Using Access Rules



Description
Often it is useful to capture traffic that is going to a specific FQDN or IP address for auditing or reporting purposes. We can create an Access Rule and capture traffic that only applies to that rule. This can be useful when there is malicious traffic going out from a network. Administrators may want to block the traffic (via access rules) but also capture the traffic in the packet capture to view where the source is coming from to mitigate the incident.
Resolution
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
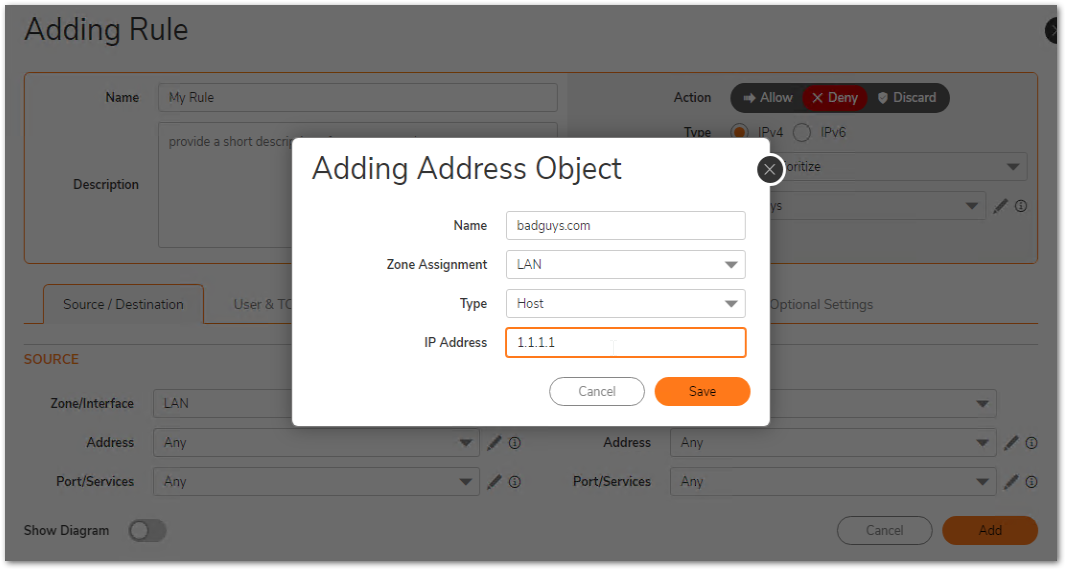
Step 1: Create an Access Rule for the traffic flow of your scenario. This example will block all outbound connections going to IP address 1.1.1.1.
Note: When creating the Access Rule select "Enable Packet Monitor". This will be important in later steps.
Go to Optional settings and click on Enable Packet monitor.
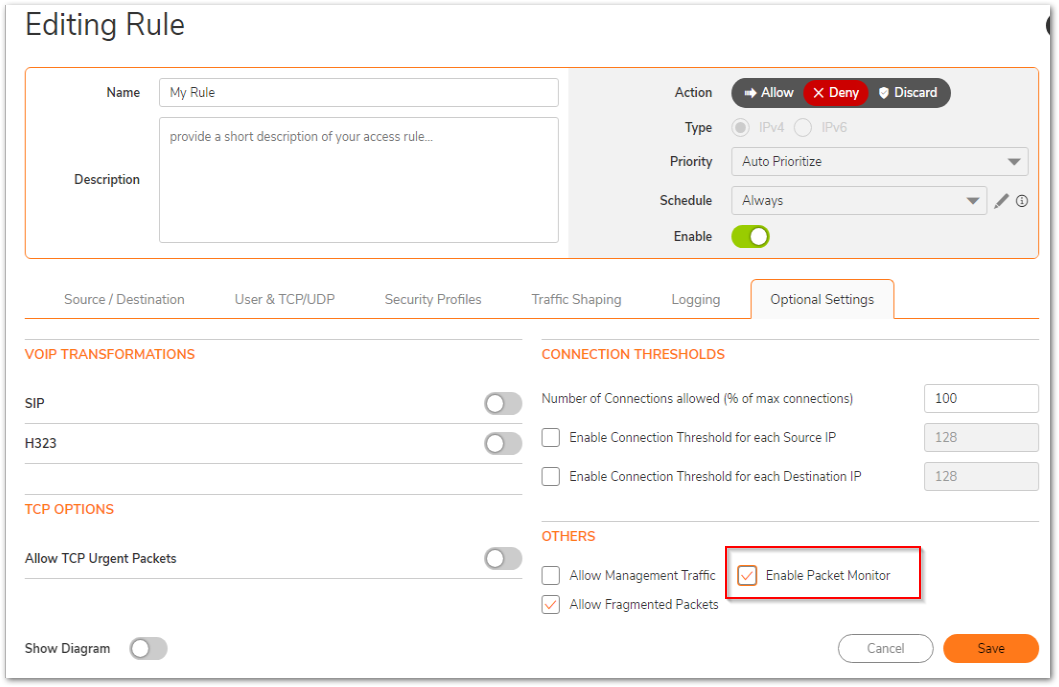
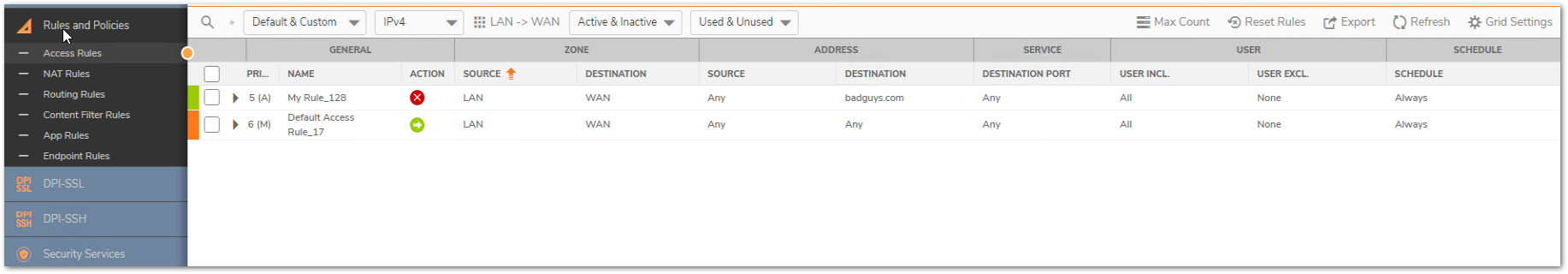
We can confirm that the Access Rule is in place and also confirm that packet monitor is enabled (see the Packet Monitor column within the access rule).
Step 2: Go to the Packet Monitor page via Tootls & Monitors | Packet Monitor and select General. Navigate to Monitor Filter and select Enable firewall based on the firewall/app rule:
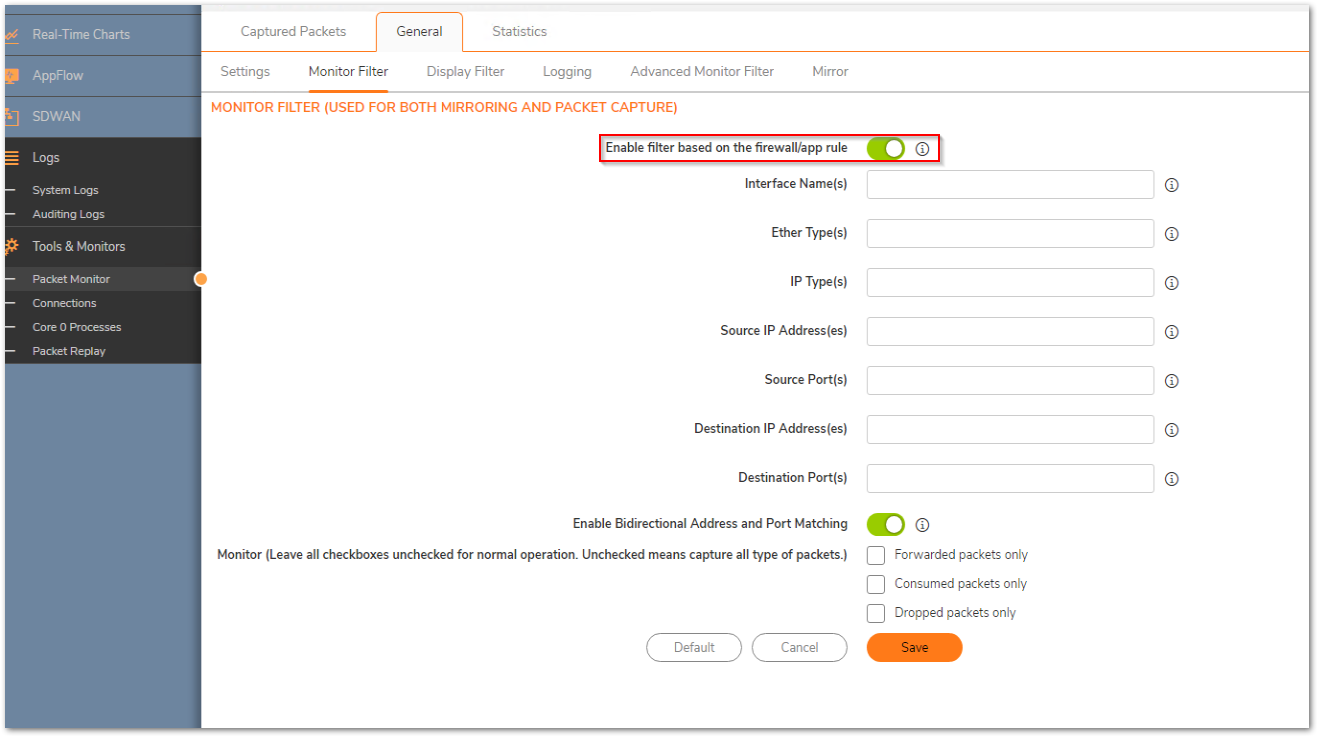
Note: No further information is needed because the traffic will be captured when the Access Rule is triggered. Entering any data into the monitor filter will only narrow down the traffic results.
Step 3: Select Save to capture.
How to Test:
Using a browser, access the IP address or FQDN that was recently added to the access rule. Our example blocks 1.1.1.1.
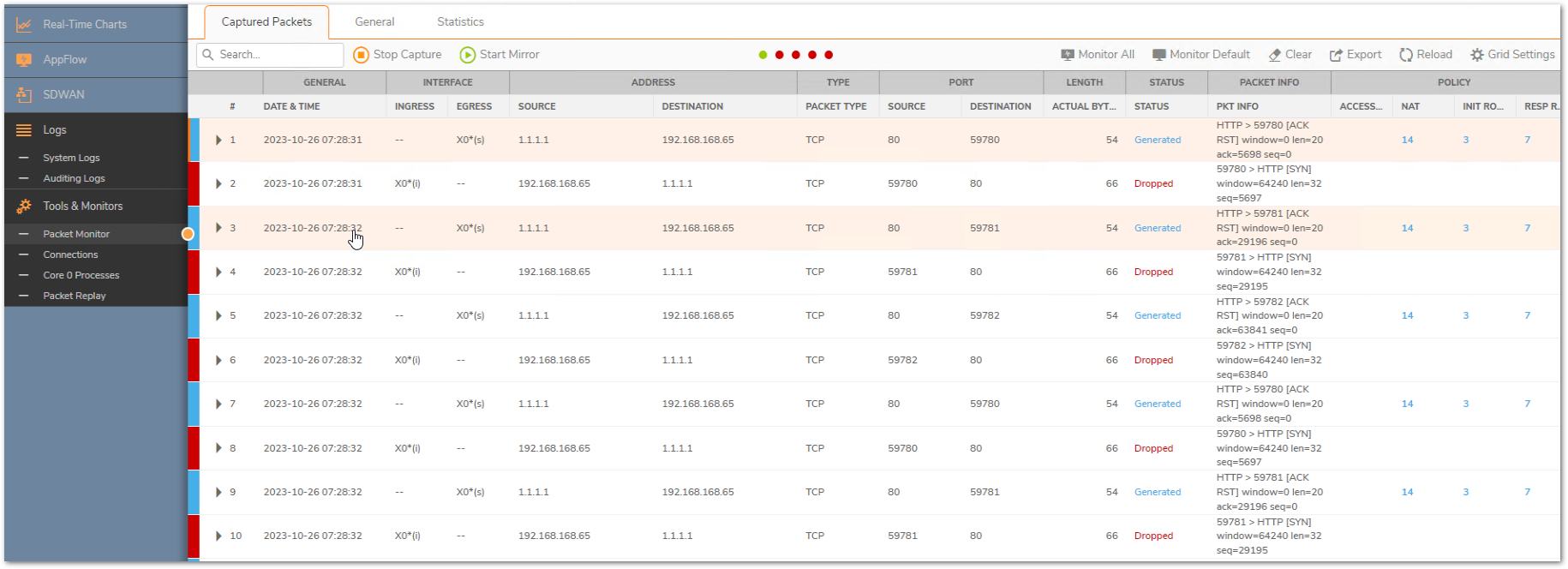
Notice that the traffic was blocked and also the internal IP address of where the traffic originated from.
Resolution for SonicOS 6.2 and Below
The below resolution is for customers using SonicOS 6.2 and earlier firmware. For firewalls that are generation 6 and newer we suggest to upgrade to the latest general release of SonicOS 6.5 firmware.
Step 1: Create an Access Rule for the traffic flow of your scenario. This example will block all outbound connections going to IP address 1.1.1.1.
Note: When creating the Access Rule select "Enable Packet Monitor". This will be important in later steps.
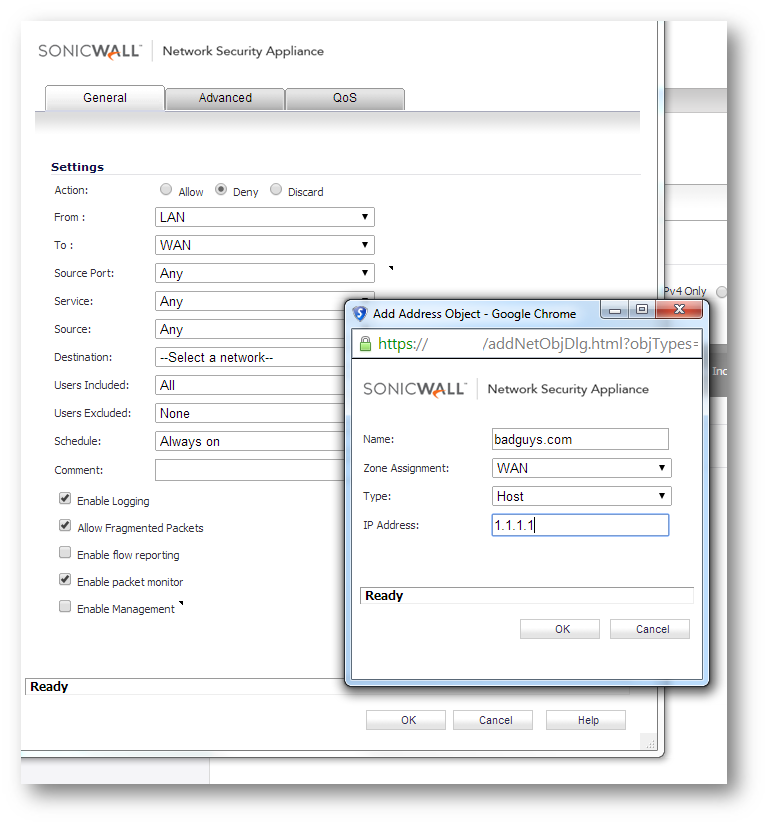
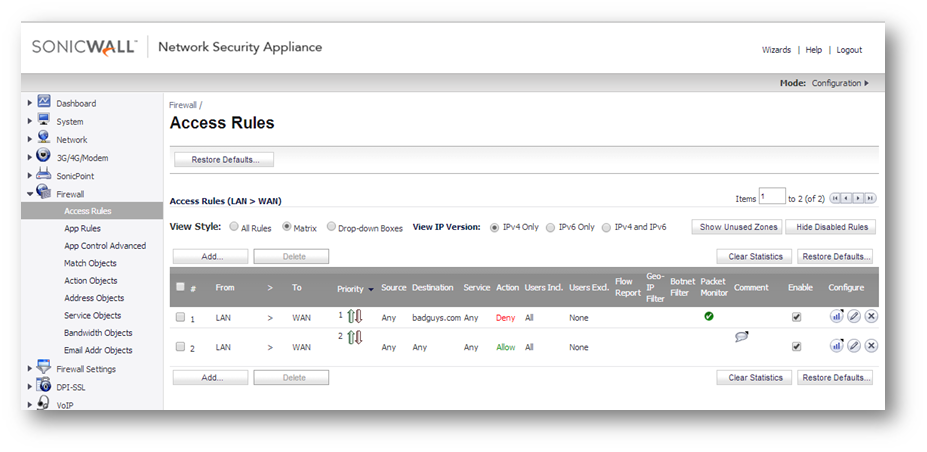
We can confirm that the Access Rule is in place and also confirm that packet monitor is enabled (see the Packet Monitor column within the access rule).
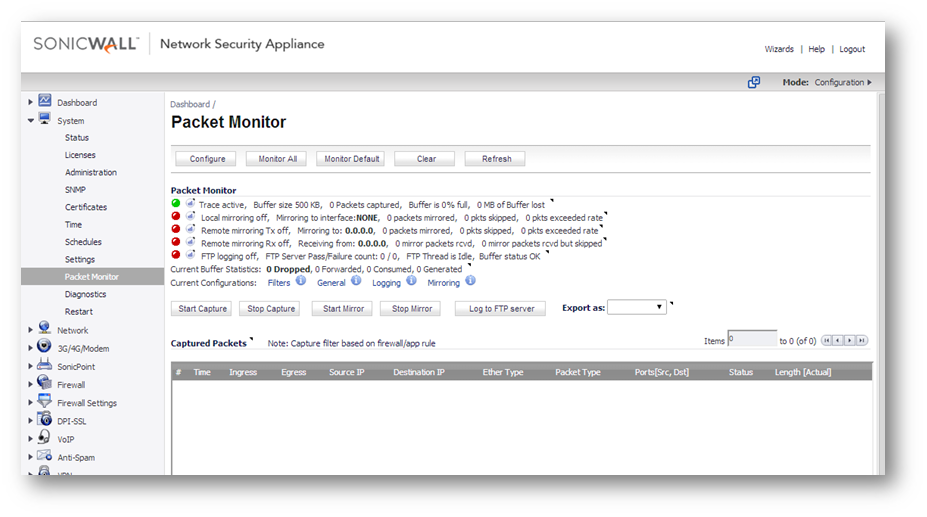
Step 2: Go to the Packet Monitor page via System | Packet Monitor and select Configure. Navigate to Monitor Filter and select Enable firewall based on the firewall/app rule: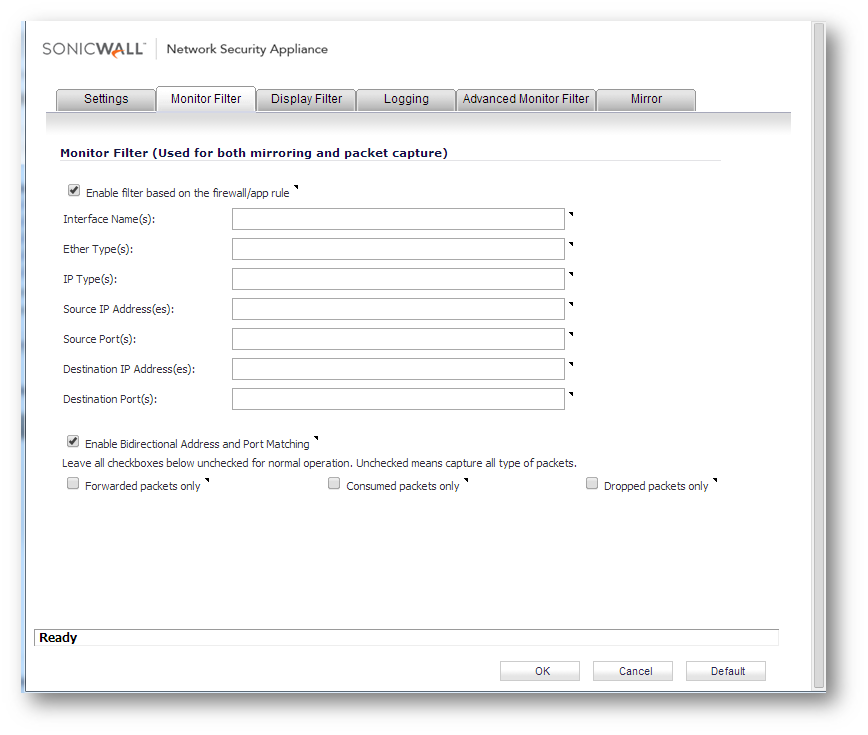
Note: No further information is needed because the traffic will be captured when the Access Rule is triggered. Entering any data into the monitor filter will only narrow down the traffic results.
Step 3: Select OK and click Start to capture.
How to Test:
Using a browser, access the IP address or FQDN that was recently added to the access rule. Our example blocks 1.1.1.1.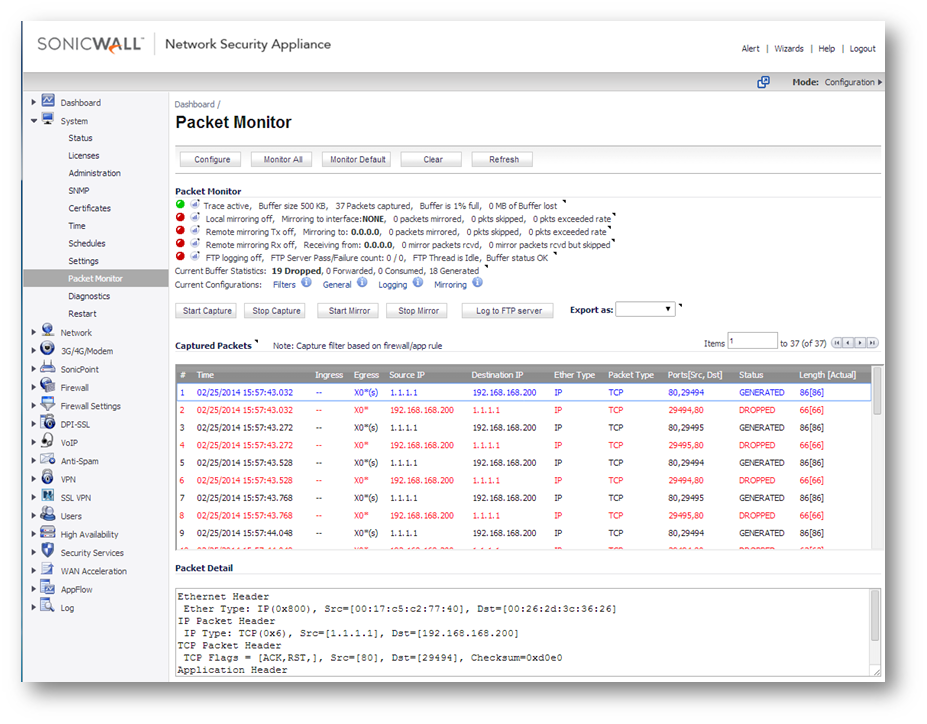
Notice that the traffic was blocked and also the internal IP address of where the traffic originated from.
Related Articles
- Error:"Invalid API Argument" when modifying the access rules
- Cysurance Partner FAQ
- Configure probe monitoring for WAN Failover and Loadbalancing - SonicWall UTM
Categories
- Firewalls > TZ Series
- Firewalls > SonicWall SuperMassive E10000 Series
- Firewalls > SonicWall SuperMassive 9000 Series
- Firewalls > SonicWall NSA Series






 YES
YES NO
NO