-
Products
-
Gen 7 Firewalls
SonicWall's Gen 7 platform-ready firewalls offer performance with stability and superior threat protection — all at an industry-leading TCO.
Read More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
Content Filtering Service (CFS) 4.0 Overview



Description
Starting with Sonic OS 6.2.6 SonicWall firewalls introduce Content Filtering Service 4.0. In this new version CFS is optimized and enhanced by including framework and workflow redesign, UI ease of use, improved filtering options, handling smaller packet sizes, etc.
This article describes all aspects of configuring Content Filtering Service 4.0.
Enhancements
- An option added to enable/disable CFS globally.
- Define URI List object, Profile object and Action object, which can be reused in multiple policies.
- Merge via Zones mode and via App Rules mode into one.
- Support Wildcard "*" matching for URI List.
- Introduce Passphrase and Confirm operations in CFS action object.
- Support more commands in html page editing, which including GET, HEAD, POST, PUT, CONNECT, OPTIONS, DELETE, REPORT, COPY and MOVE.
- Support the BWM.
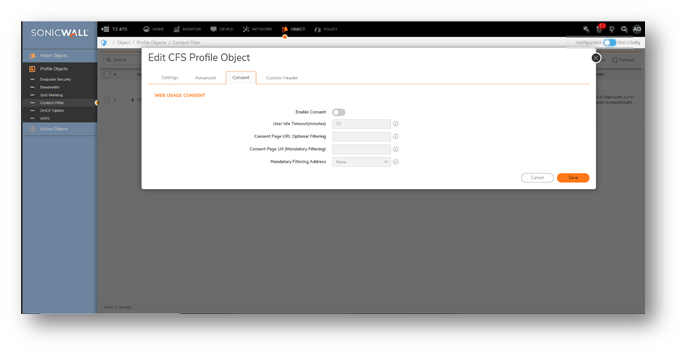
- Consent feature is per policy.
 NOTE: There are about ~42M URLs in CFS 4.0 database and the data is increasing day by day.
NOTE: There are about ~42M URLs in CFS 4.0 database and the data is increasing day by day.
Resolution
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
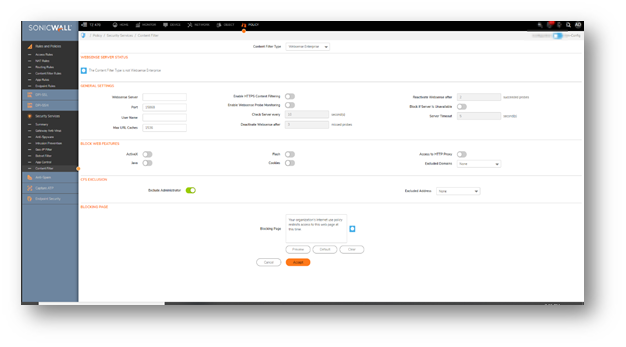
Content Filtering page:
- Navigate to Policy|Security Services|Content Filter, users are given a choice to select the content filter type: SonicWall CFS and Websense Enterprise.
- By default, the type is SonicWall CFS.
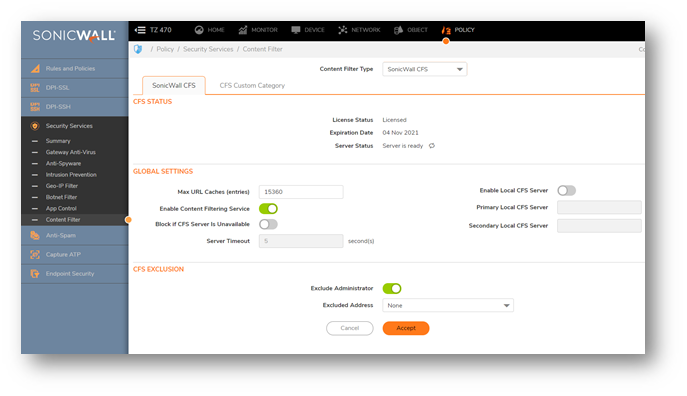
Global Settings:
- In this, we have the option to Enable/Disable Content Filtering Services Globally.
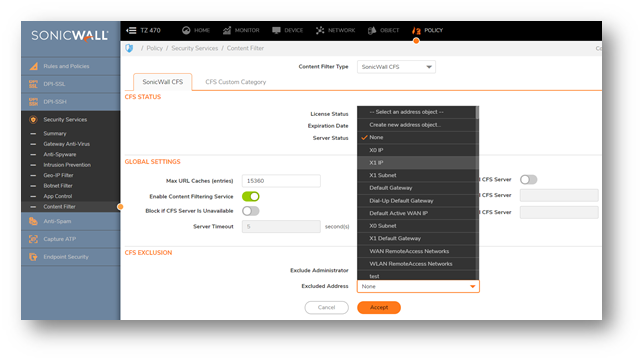
CFS exclusion:
- On the CFS exclusion, we can Exclude administrator from the Content Filtering Policies, and we can use address objects of the IP addresses for the exclusion.
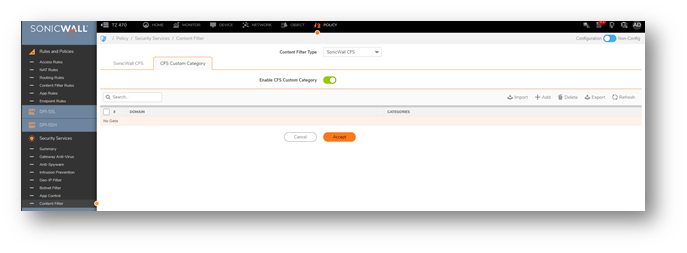
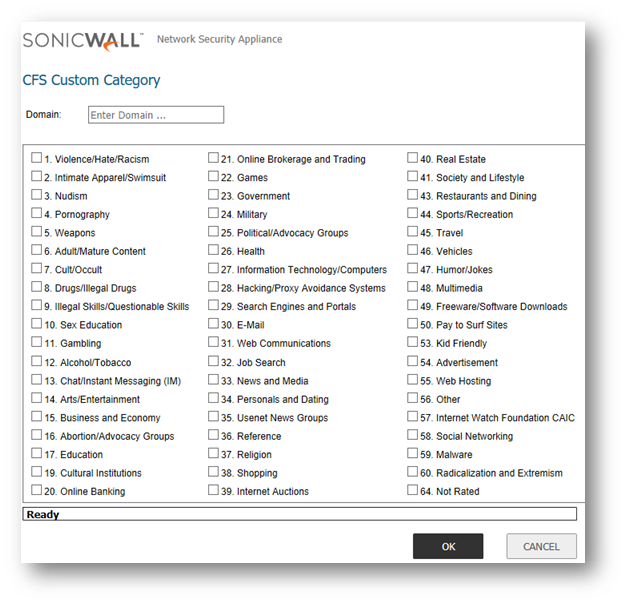
CFS custom Category:
- Navigate to Policy|Security Services|Content Filter page and you can Enable CFS custom Category.
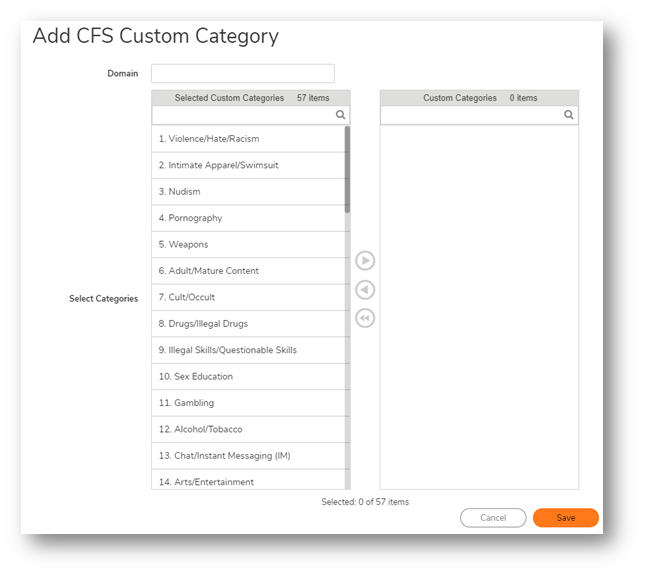
- In this section, users can add custom categories and customize the ratings for the certain URI, When CFS checks the ratings for one URI, it will check the user ratings first, then check for the ratings from backend. When users try to add/edit a custom category, they will need to input a valid URI, and select up to 4 kinds of categories for this URI.
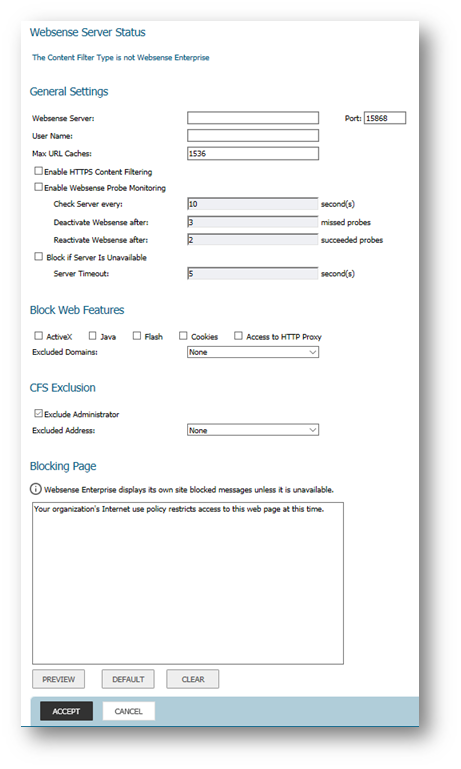
Websense Enterprise:
- Websense configuration can be done under the Policy|Security Services with content filter type as Websense Enterprise.
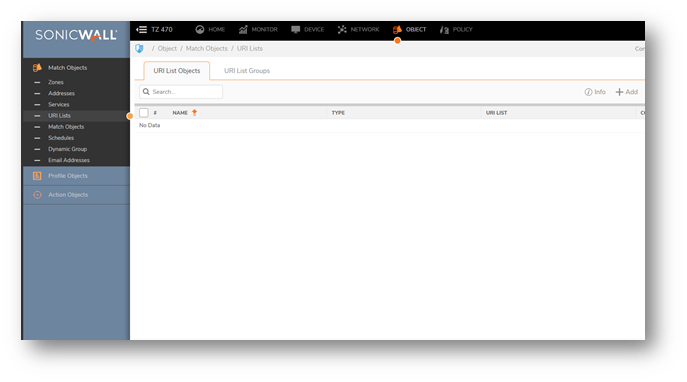
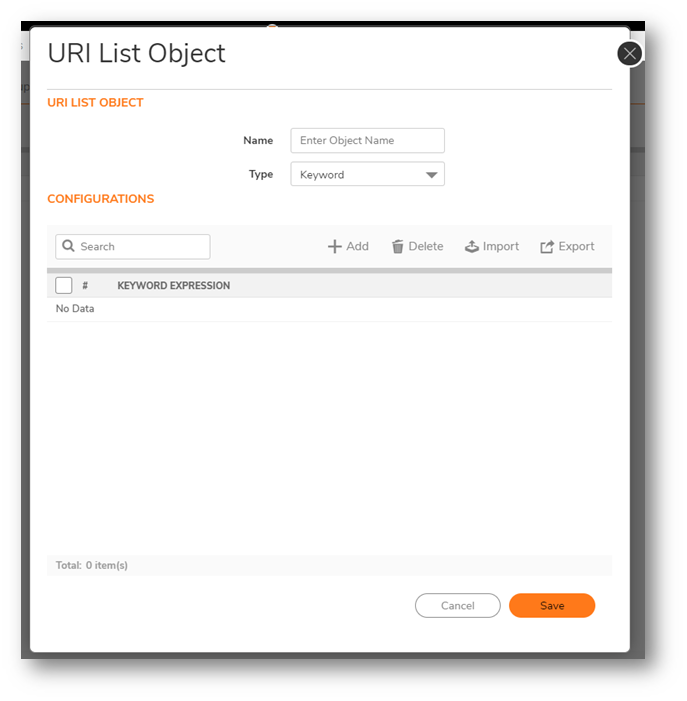
CFS URI Lists:
- Navigate to Objects|Match objects|URI Lists, to configure CFS URI objects which can be used to add the domains, URL’S into the list, and set this list as custom Allowed or Forbidden.
- The URI list can be grouped together as well, and this list will have higher priority than the CFS category and it will check the list before checking for the category for an URI.
-
Users can also add Wildcard character “*” is supported in the URI string, for instance *.yahoo.com
- The URI list object will be used in Profile objects|Content Filter.
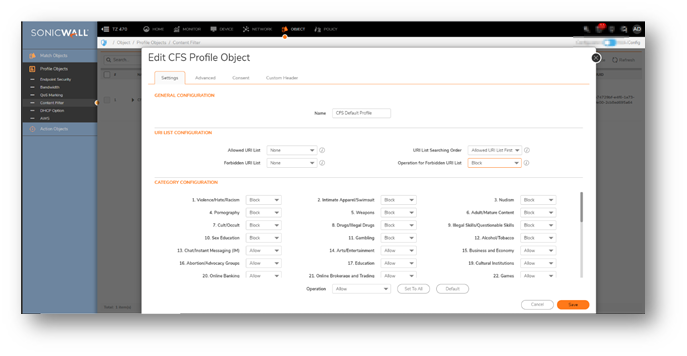
CFS profile:
- Navigate to Object|Profile Objects|Content Filter for the CFS default profile.
- CFS Profile object defines the type of operation which will be triggered for each HTTP/HTTPS connections and this same profile will be used in the CFS policy.
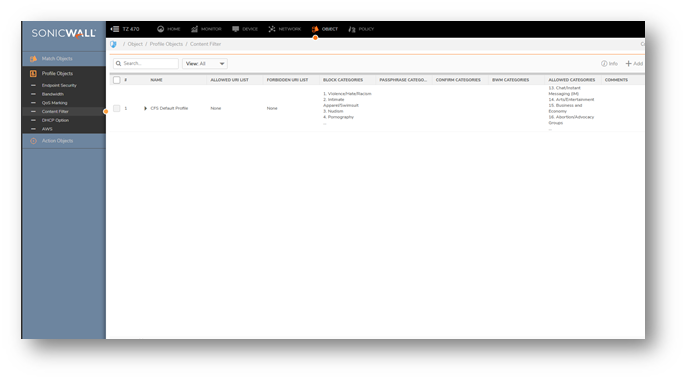
URI list Configuration:
- Allowed URI List and Forbidden URI list can be selected according to the URI list object created, when searching the URL inside Allowed/Forbidden URL lists, we will start the searching from which one.
Category Configuration:
- For each category, users can define the operation for it if the URI is belonged to the category. By default, the operation for category 1 ~ 12 is blocked, the operation for other categories is allowed.
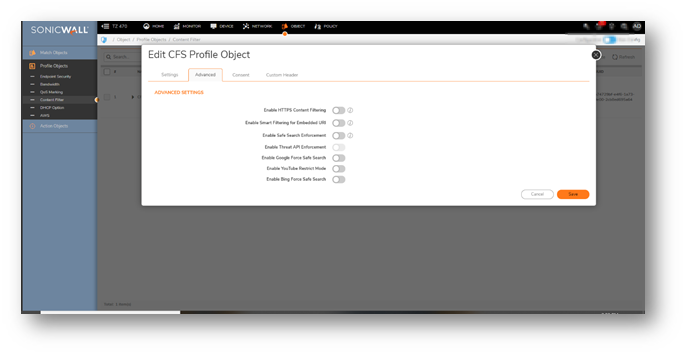
We have multiple advanced options the CFS profile object which includes:
- Enable Smart Filtering for Embedded URI: Google Translate https://translate.google.com provides the capability to translate one site from one language to another. Because the website to be translated is embedded inside Google Translate URI, user can bypass CFS with it. With this new feature, if users want CFS to detect the embedded URI inside Google Translate, users can enable this option and then the embedded URI will be filtered.
- Enable Safe Search enforcement: When searching from these websites www.google.com, www.yahoo.com, www.bing.com, www.dogpile.com, www.lycos.com, www.ask.com, Safe Search will be turned on.
- Enable YouTube Restrict Mode: When accessing to YouTube, student can only view the video predefined by the school administrator. If enabling this option, user will need to provide a valid school ID.
 NOTE: All these options only support for the HTTP request. For the HTTPS request, DPI-SSL needs to be used cooperatively.
NOTE: All these options only support for the HTTP request. For the HTTPS request, DPI-SSL needs to be used cooperatively.
- We can also define the Web usage content under Consent in CFS profile Objects.
CFS Action Objects:
- Navigate to Object|Action objects|Content filer Actions to define how CFS deal with the packet after it is filtered.
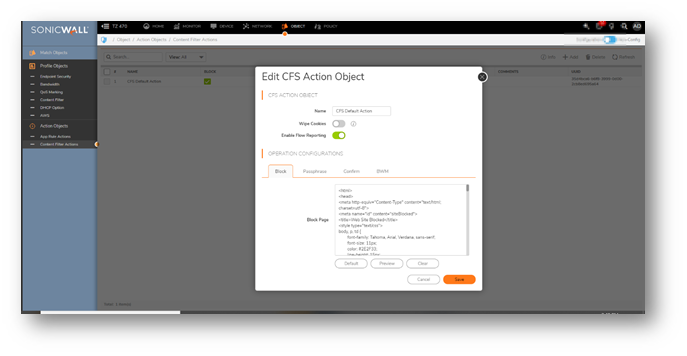
- There are four actions supported in CFS:
- Block: Users can define the blocking page to display if the connection is blocked.
- Passphrase: Users can define the passphrase page to display and the password needed before continue.
- Confirm: Users can define the confirm page to display.
- BWM: Users can configure Bandwidth Aggregation Methodas Per Policy or Per Action. Users can also configure the detailed BWM status and objects for Egress Bandwidth Management and Ingress Bandwidth Management.
 TIP: The Action Objects will be used by CFS Policy.
TIP: The Action Objects will be used by CFS Policy.
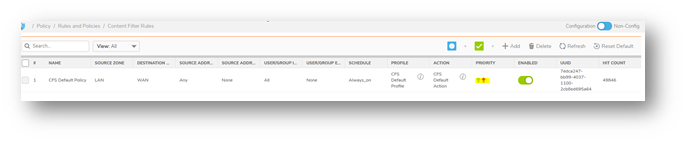
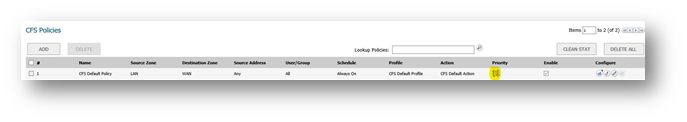
Content Filer Policies :
- Navigate to Policy|Rules and Policies|Content Filer Rules and add the CFS policies with the specific URI list objects and action objects.
- By default, a CFS default policy exists with the CFS default profile and CFS default action, Users can either edit the existing Policy or can add the new policy as well.

-
Users can define matching conditions to hit a CFS Policy: Enabled, Source Zone, Destination Zone, Address Object, Users/Groups, Schedule, CFS Profile, and CFS Action.
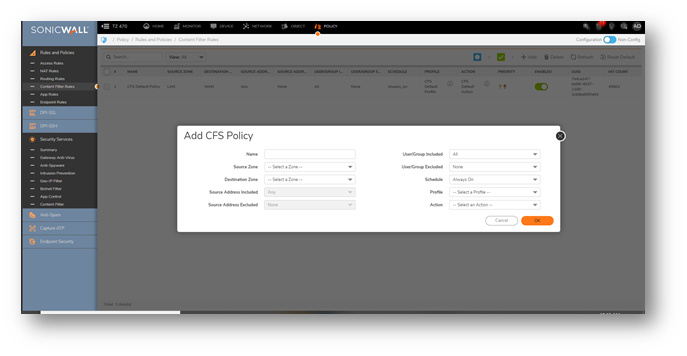
-
If a packet is detected and all these conditions are matched, it will be filtered by the corresponding CFS Profile. Then the CFS Action will be invoked after filtering.
- There is priority for each CFS Policy. The matched CFS Policy with higher priority will always be checked earlier.
Resolution for SonicOS 6.5
This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware.
Content Filter page
- On the Manage |Security Configuration | Ssecurity Services | Content Filter page, users are given a choice to select the Content filter type between SonicWall CFS and Websense Enterprise. By default the type is SonicWall CFS.
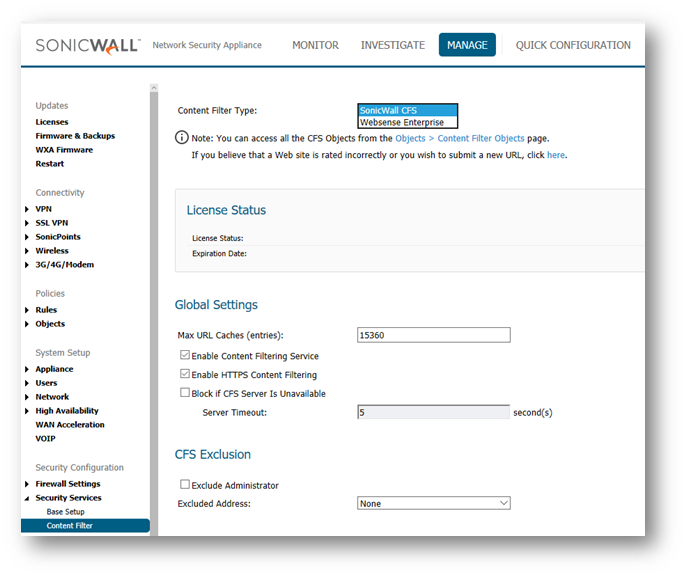
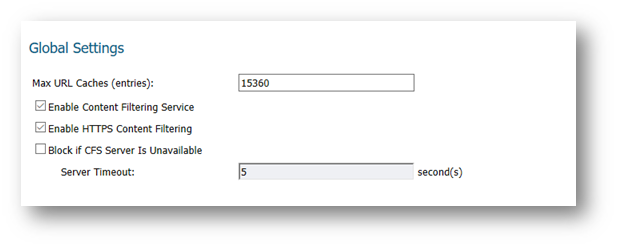
Global Settings
- Unlike previous CFS versions CFS4.0 is implemented by CFS Policies. Hence the options in SonicWall Filter Properties window are moved to Content Filter page and optimized under Global Settings section. The option Enable Content Filtering Service is added to enable/disable CFS globally.
CFS Objects
- To make the configurations reusable and easy to manage, three objects are introduced in CFS. They are URI List Objects, CFS Action Objects and CFS Profile Objects. Navigate to Manage | Policies | Objects | Content Filter Objects page to configure them.
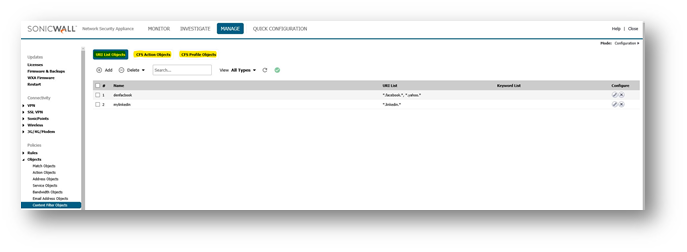
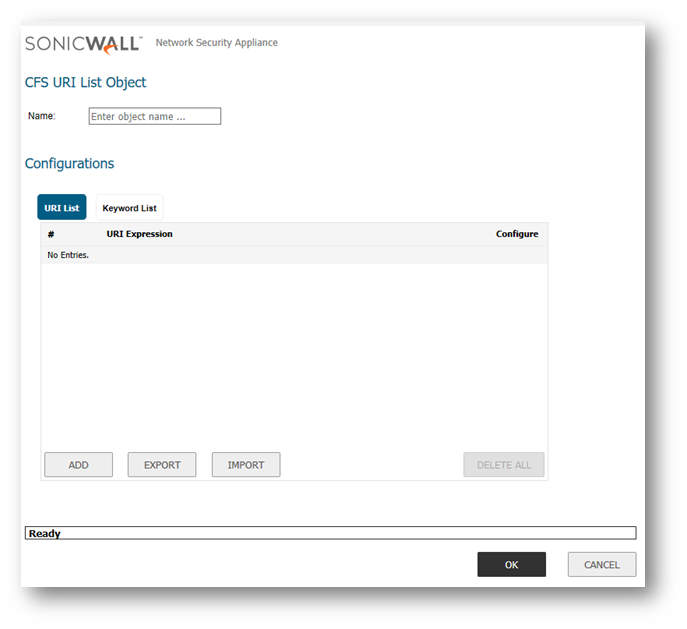
URI List Objects
- With this object, users can add the domains, URIs into the list, and set this list as custom Allowed or Forbidden. The lists will have higher priority than the category. CFS will check the lists before checking for the category for an URI. And Wildcard character "*" is supported in the URI string, for instance *.google.com.
- The URL List Object will be used by a CFS Profile Object.
CFS Action Objects
- This object defines how CFS will deal with the packet after it is filtered.
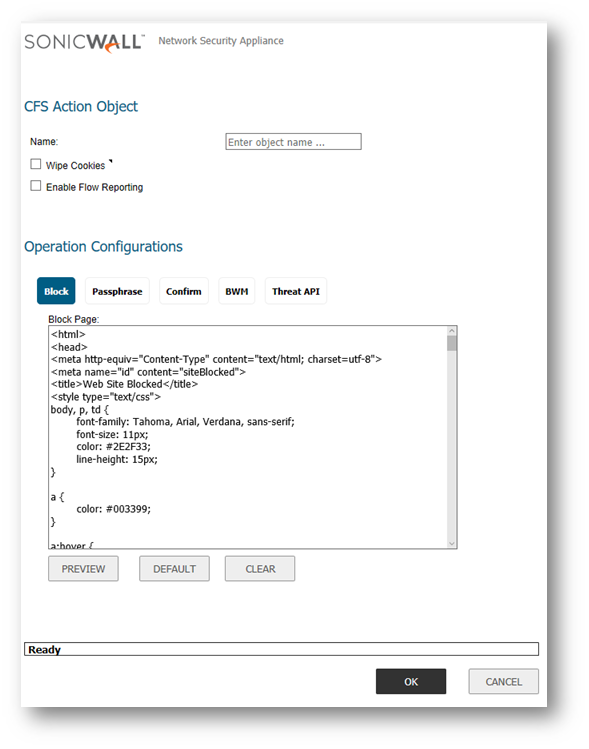
Wipe Cookies: The cookies inside the HTTP request will the removed to protect privacy.
 NOTE: If Wipe Cookies is enabled, it may break the Safe Search Enforcement function for some search engines.
NOTE: If Wipe Cookies is enabled, it may break the Safe Search Enforcement function for some search engines.
There are five actions supported in CFS
- Block: Users can define the blocking page to display if the connection is blocked.
- Passphrase: Users can define the passphrase page to display and the password needed before continue.
- Confirm: Users can define the confirm page to display.
- BWM: Users can configure Bandwidth Aggregation Method as Per Policy or Per Action. Users can also configure the detailed BWM status and objects for Egress Bandwidth Management and Ingress Bandwidth Management.
- Threat API: Shows Threat API Block page message.
 TIP: The Action Objects will be used by CFS Policy.
TIP: The Action Objects will be used by CFS Policy.
CFS Profile Objects
- CFS Profile Object defines what kind of operation will be triggered for each HTTP/HTTPS connections and will be used by CFS Policy.

- URI List Searching Order: When searching the URL inside Allowed/Forbidden URL lists, we will start the searching from which one.
- Category Configuration: For each category, users can define the operation for it if the URI is belonged to the category. By default, the operation for category 1 ~ 12 is blocked, the operation for other categories is allowed.
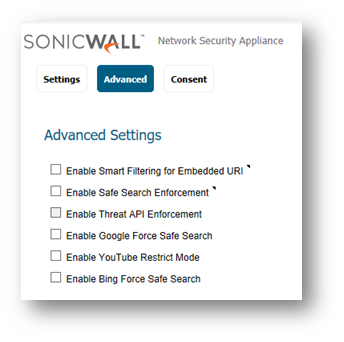
- Enable Smart Filtering for Embedded URI: Google Translate https://translate.google.com provides the capability to translate one site from one language to another. Because the website to be translated is embedded inside Google Translate URI, user can bypass CFS with it. With this new feature, if users want CFS to detect the embedded URI inside Google Translate, users can enable this option and then the embedded URI will be filtered.
- Enable Safe Search enforcement: When searching from these websites www.google.com, www.yahoo.com, www.bing.com, www.dogpile.com, www.lycos.com, www.ask.com, Safe Search will be turned on.
- Enable YouTube Restrict Mode: When accessing to YouTube, student can only view the video predefined by the school administrator. If enabling this option, user will need to provide a valid school ID.
 NOTE: All these options only support for the HTTP request. For the HTTPS request, DPI-SSL needs to be used cooperatively.
NOTE: All these options only support for the HTTP request. For the HTTPS request, DPI-SSL needs to be used cooperatively.
CFS Policies
- Users are able to define matching conditions to hit a CFS Policy: Enabled, Source Zone, Destination Zone, Address Object, Users/Groups, Schedule, CFS Profile, and CFS Action.

- If a packet is detected and all these conditions are matched, it will be filtered by the corresponding CFS Profile. Then the CFS Action will be invoked after filtering.
- There is priority for each CFS Policy. The matched CFS Policy with higher priority will always be checked earlier.
CFS Customer Category
- Users can customize the ratings for certain URI. When CFS checks the ratings for one URI, it will check the user ratings first, then check for the ratings from backend. When users try to add/edit a custom category, they will need to input a valid URI, and select up to 4 kinds of categories for this URI.

Websense Enterprise
- Comparing with the previous version, CFS 4.0 separates the Websense configuration from SonicWall CFS. This is to avoid confusion between the two content filter Types.
Related Articles
- Configuring split DNS over site to site VPN
- How to enable DNS Doctoring?
- Understanding TCP Handshake violation
Categories
- Firewalls > TZ Series > Content Filtering Service
- Firewalls > NSa Series > Content Filtering Service
- Firewalls > NSv Series > Content Filtering Service






 YES
YES NO
NO