Another TLS Vulnerability – Logjam Found Last Week (May 28, 2015)
Another major vulnerability Logjam in TLS was released last week. Logjam actually involve two related but separated vulnerabilities, one is man-in-the-middle security suite downgrade, which is similar to FREAK vulnerability in TLS released in March 2015; the other is exploiting EXPORT cryptography or small DH parameters encrypted traffic by force. An attacker can exploit the vulnerabilities and eavesdrop all of the encrypted traffic without target's knowledge.
To accomplish an attack by exploiting the first vulnerability, a man-in-the-middle attacker needs to intercepts the target's traffic to the server with the following steps:
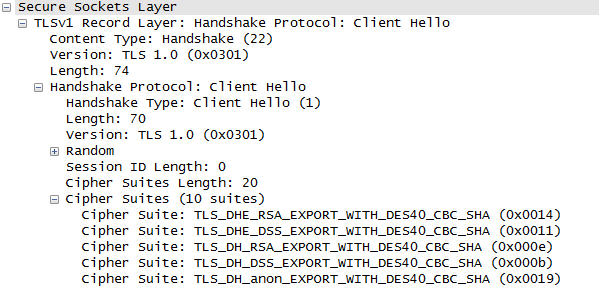
- The client hello info with accepted cipher suites should be replaced with only DHE_EXPORT ones. A sample of DHE_EXPORT client hello is showed below:
- The server accepted and pick a DHE_EXPORT cipher suite and send it back to client.
- The attacker should be able to decrypt the weak DHE_EXPORT encryption, then recover the keys with further attacks without target's knowledge.
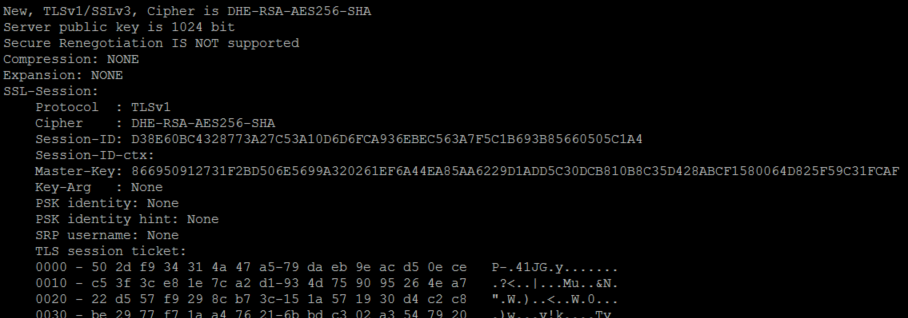
To decide if the server is vulnerable, OpenSSL suggests using the following commands to verify the length of the key and the support of Export cipher suites:
- $ openssl s_client -connect .com:443 -cipher "EDH"
- $ openssl s_client -connect www.example.com:443 -cipher "ECDHE"
- $ openssl s_client -connect www.example:com:443 -cipher "EXP"
A typical reply for DH configuration test is listed below. It comes with 1024 bit server public key and DHE RSA encryption:
Dell SonicWALL threat team has created the following IPS signatures to protect their customers:
- IPS:6366 "Client Hello with EXPORT Cipher Suites 1"
- IPS:6412 "Client Hello with EXPORT Cipher Suites 2"
- IPS:6428 "Server Hello with EXPORT Cipher Suite"
Share This Article
An Article By
An Article By
Security News
Security News