Critical XWiki Sensitive Information Disclosure Vulnerability (CVE-2025-55748)
Overview
The SonicWall Capture Labs threat research team became aware of a sensitive information disclosure vulnerability in XWiki, assessed its impact and developed mitigation measures. XWiki is an open-source platform that enables organizations to build and manage internal knowledge bases and documentation systems.
A critical vulnerability, tracked as CVE-2025-55748, has been discovered in XWiki, affecting versions prior to 17.4.0-rc-1 and 16.10.7. This flaw allows remote attackers to access sensitive files on the server by exploiting an underlying path traversal issue. Given that another recently disclosed XWiki vulnerability is already being actively exploited in the wild, this new weakness is likely to draw attention from threat actors. Hence, organizations using XWiki are strongly advised to update their instances to the latest patched version as soon as possible to minimize exposure and potential compromise.
Technical Overview
The vulnerability resides in the SxResourceSource.java file, where user-supplied input from the resource parameter is not properly validated before being used to access files. As shown in Figure 1, the vulnerable version of the getContent() method directly passes the user-controlled value this.resourceName to the getResourceAsStream() method without sanitization.
The getResourceAsStream() method interprets the input path as relative to the classpath root and, importantly, does not validate or restrict path traversal attempts. This flaw enables remote attackers to exploit directory traversal sequences (../) to navigate outside the intended directory and access sensitive files on the server.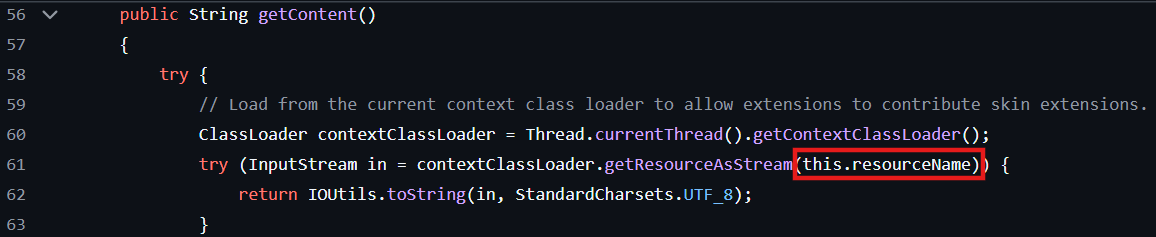
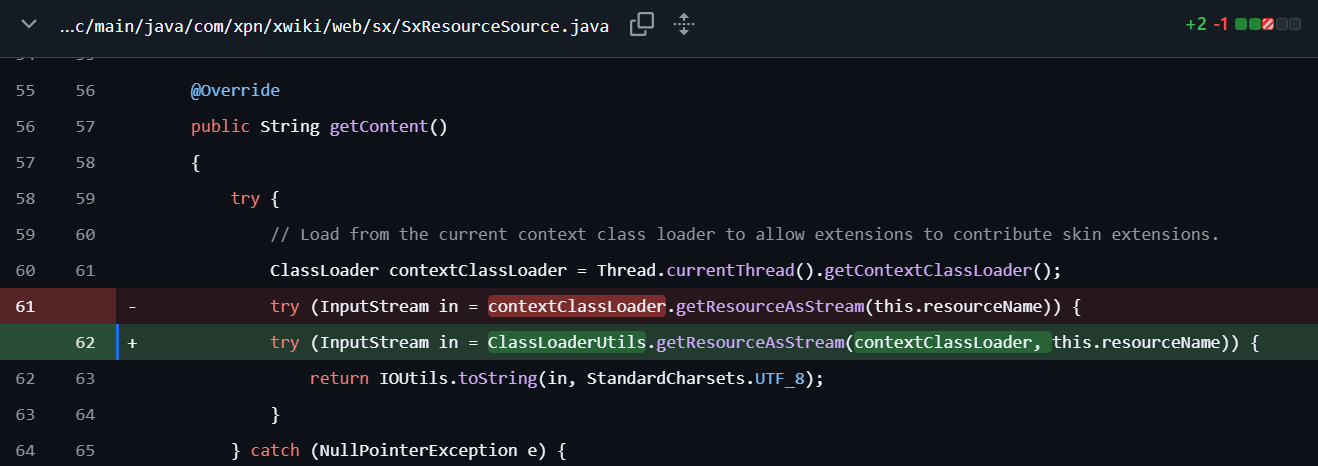
The affected endpoints include the SSX (Skin Style Extension) and JSX (Skin JavaScript Extension) endpoints, which are responsible for loading skin-related JavaScript and CSS files from JAR packages. Attackers can abuse these endpoints by inserting traversal patterns into the resource parameter to escape the restricted directory and retrieve confidential files. For example, the following crafted request can be used to access the XWiki configuration file:
httx[:]//<target_ip>[:]8080/bin/jsx/Main/WebHome?resource=../xwiki.cfg
To mitigate this issue, XWiki introduced proper validation checks for user-supplied paths. As illustrated in Figure 2, the patch includes a new utility class, org.xwiki.classloader.internal.ClassLoaderUtils, which provides secure methods for resource access with built-in path traversal protection.
Exploitation
Successful exploitation of this vulnerability allows remote, unauthenticated attackers to retrieve highly sensitive configuration files from the server. Access to such files can expose critical credentials and internal configurations, potentially leading to a complete system compromise.
Below are a few high-value targets that an attacker may target.
- xwiki.cfg
This is XWiki’s main configuration file and contains core system settings. If the superadmin account is enabled, the file may also store its password in plaintext, allowing an attacker to fully compromise the application.
An example exploit request to access this file is illustrated in Figure 3.
Figure 3 Accessing xwiki.cfg - hibernate.cfg.xml
This file holds database connection details, including credentials and connection pool configurations. An attacker gaining access to this file could establish persistent, stealthy access to the database by adding new admin accounts or modifying existing permissions.
A sample exploit request to retrieve this file is shown in Figure 4.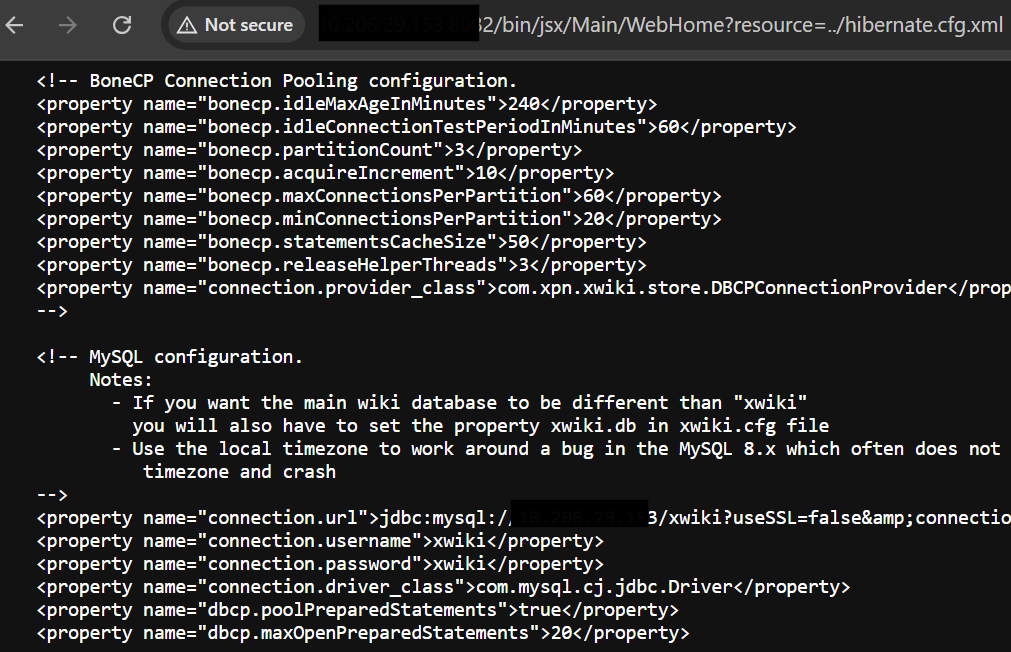
Figure 4 Accessing hibernate.cfg.xml
The resulting impact of this vulnerability is high across confidentiality, integrity, and availability metrics. Once exploited, attackers can achieve several end goals, such as:
- Full application or database takeover
- Data exfiltration of sensitive information
- Privilege escalation or creation of rogue admin accounts
- Lateral movement within the network to compromise additional systems
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:- IPS: 21667 XWiki Platform sx Endpoints Path Traversal
Remediation Recommendations
With more than 5,000 organizations, including several high-profile enterprises, relying on XWiki as part of their operations, the platform continues to attract the attention of threat actors. Given the critical nature of this vulnerability, users are strongly advised to upgrade their XWiki instances to the latest patched version as detailed in the official vendor advisory.
In addition to applying the security update, organizations should consider implementing the following defense-in-depth measures to reduce exposure and strengthen their security posture:
- Apply IPS signature #21667 mentioned above.
- Restrict XWiki access to internal networks or VPN-connected users only.
- Maintain an IP allow list for administrative access to limit exposure to trusted addresses.
- Apply network segmentation to isolate XWiki servers from critical systems.
- Enforce the principle of least privilege, ensuring users and services have only the access necessary for their roles.
Relevant Links
Share This Article

An Article By
An Article By
Security News
Security News
