GNU inetutils-telnetd remote authentication bypass to RCE (CVE-2026-24061)

Overview
The SonicWall Capture Labs threat research team became aware of a Critical authentication bypass vulnerability in GNU –a Unix-like operating system, assessed their impact, and developed mitigation measures. GNU is a collection of many programs: applications, libraries, developer tools, even games.
This critical authentication bypass vulnerability in GNU inetutils-telnetd allows unauthenticated remote attackers to gain instant root shell access via malicious NEW_ENVIRON telnet option exploitation, identified as CVE-2026-24061, affecting versions 1.9.3 up to and including version 2.7. With a CVSS score of 9.8 (Critical) due to its low attack complexity, high impact, and the fact that it affects core application functionality. As described in PoC, the impact of an argument injection can result into Remote Code Execution. The root issue is argument injection through unsafe string interpolation of client-controlled data. Hence, all organizations that use GNU instances are strongly encouraged to update their instances to the latest patched version as a matter of urgency.
Technical Overview
At the heart of vulnerability lies the core issue: USER environment variable. The telnetd server does not sanitize the USER environment variable before passing it to the login(1) program. The login program is used to establish a new session with the system. It is normally invoked automatically by responding to the login: prompt on the user's terminal. Telnet uses at least the HOME, SHELL, DISPLAY, and TERM environment variables. Other environment variables may be propagated to the other side via the TELNET ENVIRON option. The environment variable values for $HOME, $USER, $SHELL, $PATH, $LOGNAME and $MAIL are set according to the appropriate fields in the password entry. GNU InetUtils telnetd delegates authentication to /usr/bin/login by executing it as a subprocess. When establishing a connection, telnetd constructs a command-line string that includes user-provided data. As shown in Figure 1 one can supply various flags to login functionality for the /usr/bin/login executable.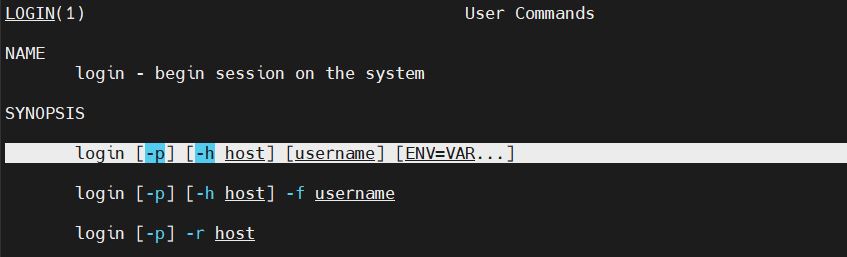
The vulnerable versions of GNU telnetd added a %U placeholder to the login command template. This placeholder is replaced with the USER environment variable, which clients can set through the Telnet protocol’s NEW_ENVIRON option during connection negotiation. The problem is that telnetd performs no sanitization or validation on this value before inserting it into the command arguments. The consequences are severe, ranging from full server compromise to RCE—all without requiring any authentication.

Exploitation
Successful exploitation of CVE-2026-24061 allows remote, unauthenticated attackers to achieve Remote Code Execution (RCE) in vulnerable GNU telnetd instances. As demonstrated in Figure 3, an attacker having access to a vulnerable GNU telnet server, starts the exploit by utilizing no authentication required flag (-f) to the $USER environment variable allowing attacker to login as a legitimate user without prompting for other credentials. The patched system will reject such requests, which introduces additional safeguards to restrict expression evaluation.
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:- IPS:2197 - Telnet Authentication Bypass
Remediation Recommendations
Given that adversary can circumvent access controls allowing them to access sensitive files with ease, users are strongly advised to upgrade their instances to the latest patched version as outlined in the official vendor advisory.
Relevant Links
Share This Article

An Article By
An Article By
Dhiren Vaghela
Dhiren Vaghela
Dhiren Vaghela has over a decade of experience in the IPS domain, with a strong focus on defensive security. His expertise lies in identifying, analyzing and mitigating vulnerabilities. Dhiren is well-versed in content-based signature writing, scanner-based alert generation and technical blog writing. By leveraging emerging technologies, he has developed numerous IPS signatures across various protocols. Known for his exceptional signature writing skills and collaborative team spirit, Dhiren is a valuable asset in the field of cybersecurity.
