How Firewall Security Assessment Reporting Strengthens Your Network Security Posture

Transform Firewall Telemetry into Actionable Security Intelligence
Most organizations rely on firewalls as their primary line of defense, but few can clearly answer a simple question: Is the firewall actually working as intended?
Without structured assessment, misconfigurations, policy gaps, and hidden risks can persist undetected for months.
Firewall security assessment reporting turns raw firewall telemetry into clear, actionable intelligence, giving security teams and executives the visibility they need to effectively strengthen their defenses. Without this kind of structured reporting, organizations often can't tell whether their firewalls are actually working, or where policy gaps exist.
SonicWall Network Security Manager (NSM) 3.5 introduces a purpose-built Security Assessment Report that directly addresses this challenge. This article explains what firewall security assessment reporting is, why it matters, and how the NSM Security Assessment Report helps organizations improve their security posture across three critical dimensions.
What Is Firewall Security Assessment Reporting?
Firewall security assessment reporting is the process of analyzing firewall telemetry — including traffic logs, threat events, application usage, and policy activity — and presenting the findings in a structured, executive-ready summary. The goal is to give IT and security teams a clear picture of how effectively their firewall is protecting the network, and where improvements are needed.
A well-structured firewall security assessment report transforms complex network data into executive-readable insights that drive smarter security decisions.
Unlike raw log exports or real-time dashboards, a security assessment report is designed to communicate security performance over time, making it useful both for technical teams tuning policies and for executives reviewing risk exposure.
Why Firewall Visibility Matters for Network Security
Modern networks generate enormous volumes of traffic across applications, users, and cloud environments. While firewalls inspect and filter this traffic in real time, security teams often lack visibility into how that inspection is actually performing.
A lack of firewall visibility can lead to several critical challenges:
- Undetected threats hidden within normal network activity
- Risky application usage that silently expands the attack surface
- User behavior that violates acceptable-use policies or reduces productivity
- Inability to communicate security value and posture to leadership
- Policy gaps that go undetected until an incident exposes them
Organizations need tools that go beyond detection to present clear, contextual insights into how effectively their security controls are performing. This is where assessment-driven reporting becomes essential.
What Is SonicWall NSM and How Does It Support Reporting?
SonicWall Network Security Manager (NSM) is the centralized management platform for SonicWall firewalls. It enables IT teams to deploy, configure, monitor, and report on firewalls across distributed environments from a single interface.
With the release of NSM 3.5, SonicWall introduced the Security Assessment Report, a structured, executive-ready report that aggregates firewall data into three key performance dimensions: threat prevention, network health, and productivity insights.
The report is designed to answer a straightforward question: Is your firewall doing its job effectively?
What Does the SonicWall NSM Security Assessment Report Include?
The NSM Security Assessment Report summarizes firewall security performance across three dimensions, each designed to surface specific, fixable issues for both technical and executive audiences.
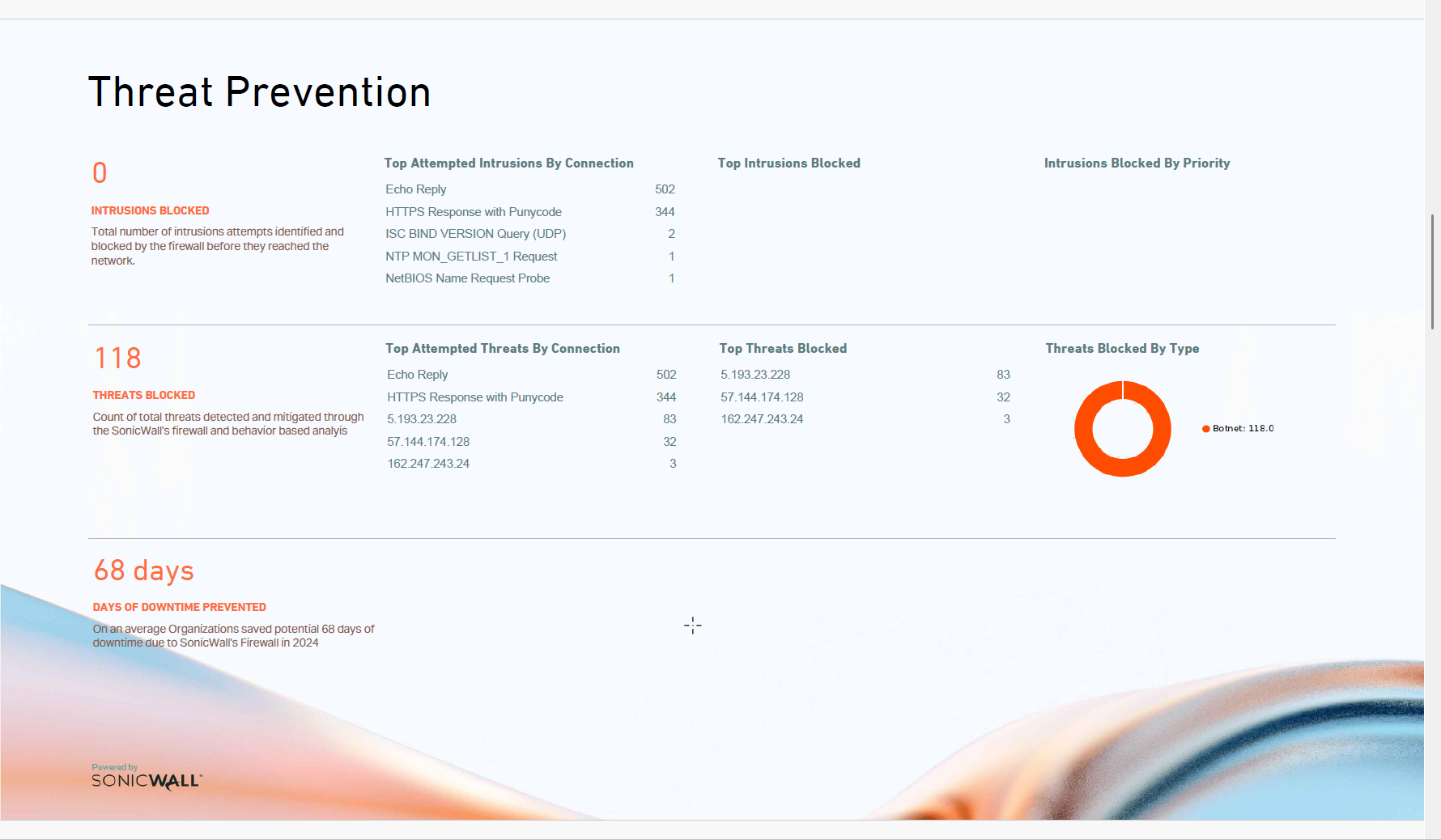
1. Threat Prevention
The threat prevention section answers a critical question: Are we stopping the right threats, and are attack patterns changing? Key metrics such as top attempted intrusions, total intrusions blocked, and threats neutralized give security teams the evidence they need to confirm firewall effectiveness and act on emerging attack trends before they escalate.
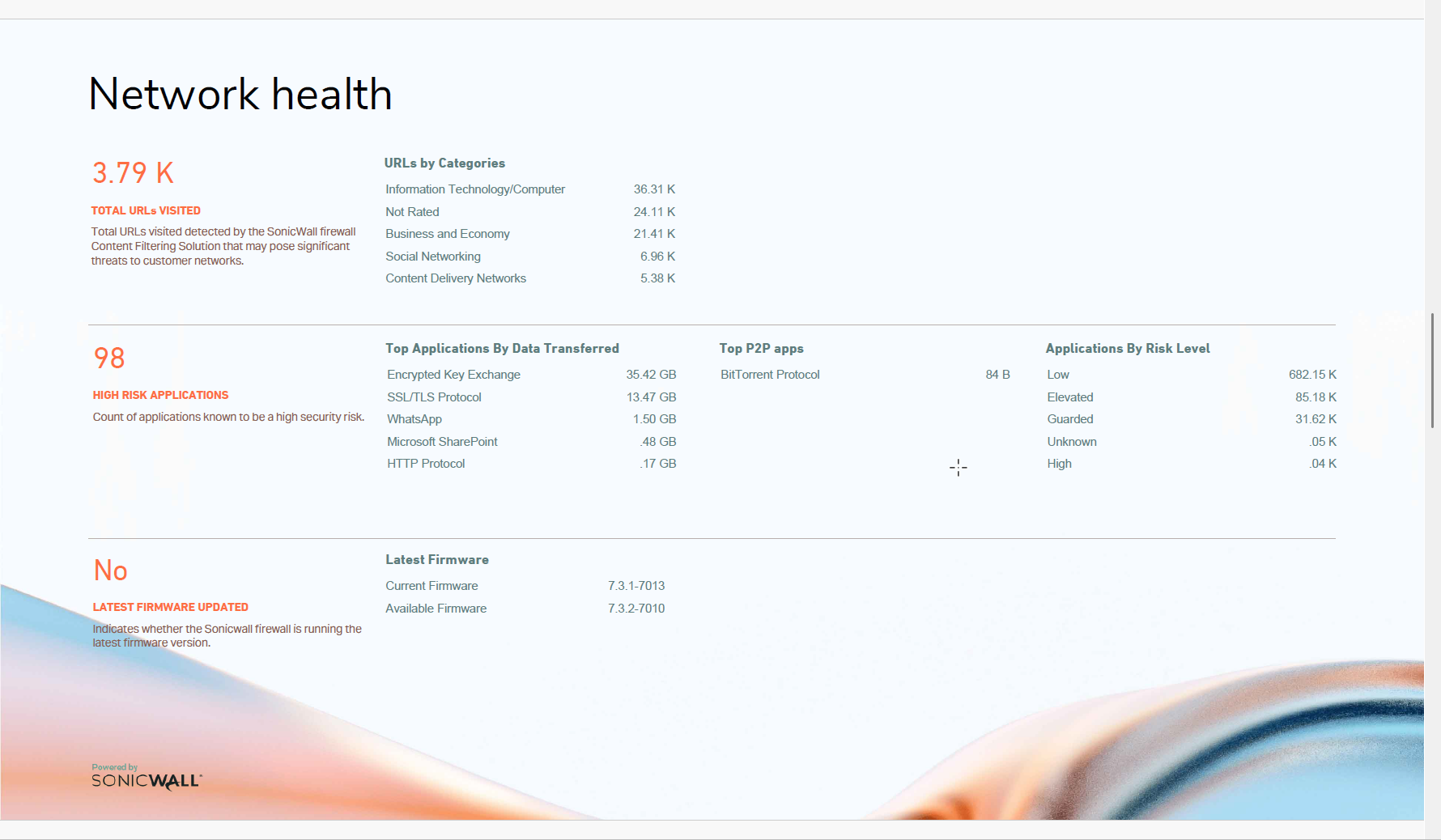
2. Network Health
Security posture isn't only about blocking threats; it also depends on maintaining a healthy, well-configured network. The network health section answers: Are our configurations and firmware up to date enough to hold the line? By surfacing commonly visited URL categories, risky or unproductive applications, and firmware versions across managed firewalls, it helps teams decide where to patch, what to restrict, and which risks to address before they become incidents.
3. Productivity Insights
The productivity insights section answers: Are our acceptable-use policies actually being enforced, and what is non-business activity costing us? Tracking time spent on unacceptable web categories and data transfers to non-business sites gives managers the data they need to intervene, update policies, and quantify the productivity impact of non-compliant behavior.
Together, these three dimensions give organizations a complete picture of firewall performance: from active threat blocking to policy compliance and resource usage.

How to Use Firewall Security Assessment Reports Effectively
To get the most out of firewall security assessment reporting, organizations should treat it as a regular operational tool rather than a one-time audit. Here are four practical ways to put it to work:
- Track threat trends: Review threat prevention metrics monthly to track whether blocked intrusion attempts are rising or shifting in type, which is an early indicator of targeted attacks.
- Prioritize patch hygiene: Use the network health section to identify firewalls running outdated firmware and prioritize patch cycles before vulnerabilities are exploited.
- Communicate security value: Share the executive summary view with leadership to communicate security ROI and justify ongoing investment in firewall security services.
- Strengthen policy enforcement: Leverage productivity insights to enforce acceptable-use policies and initiate conversations with teams about risky or non-compliant behavior.
Conclusion
Firewalls remain the foundation of network security, but their true value depends on the visibility and insights they provide. Without structured reporting, organizations may never know how effectively their security infrastructure is actually performing.
SonicWall NSM Security Assessment Report addresses this gap directly. By transforming firewall telemetry into prioritized security findings across threat prevention, network health, and productivity, it gives security teams the insights they need to effectively strengthen their posture and gives executives the confidence to know their investment is working.
Ready to gain full visibility into your firewall security posture?
Explore what's new in SonicWall NSM and start your free NSv trial today.
Share This Article

An Article By
An Article By
Mahmoud Yasin
Senior Solutions Architect
Mahmoud Yasin
Senior Solutions Architect
Mahmoud Yasin is a Senior Solutions Architect at SonicWall, where he has been making significant contributions for the past seven years, primarily focused on the EMEA region.
With over 15 years of experience in managing, leading, designing, and implementing network and security solutions, he brings a wealth of expertise to his role.
He holds several prestigious certifications, including CISSP, CEH, CCSK, SNSP, and JNCIE-Sec.
Known for translating business requirements into technical solutions effectively, Mahmoud is dedicated to delivering innovative, robust security architectures.

Leelin Thye
Senior Manager, Product Marketing
Leelin Thye
Senior Manager, Product Marketing

