What is a Virtual Firewall?

Your Workloads Moved to the Cloud; Your Security Needs to Catch Up.
A Virtual Firewall is a software-based firewall that runs inside virtual machines, cloud environments, and containerized platforms—protecting traffic between workloads, applications, and services, not just at the network edge.
Your workloads have already moved to VMware, AWS, Azure, and increasingly, Kubernetes.
But while infrastructure evolved, security often didn’t.
Traditional hardware firewalls were built for a world of fixed perimeters and predictable traffic flows. Today, applications are distributed across virtual machines, cloud instances, and containers, constantly communicating through dynamic, east-west traffic that rarely touches the network edge.
That’s where the risk lies.
Once an attacker gains access, they don’t leave; they move laterally across workloads, services, and containers. And without visibility inside these environments, that movement often goes undetected.
A Virtual Firewall closes that gap.
By operating within your virtual and cloud infrastructure, it inspects traffic in real time, enforces workload segmentation, and extends protection across both virtual machines and containerized environments.
In this guide, we’ll break down how virtual firewalls work across private and public clouds, how they complement container-native security in Kubernetes, and what to look for in a solution built for modern, distributed applications.
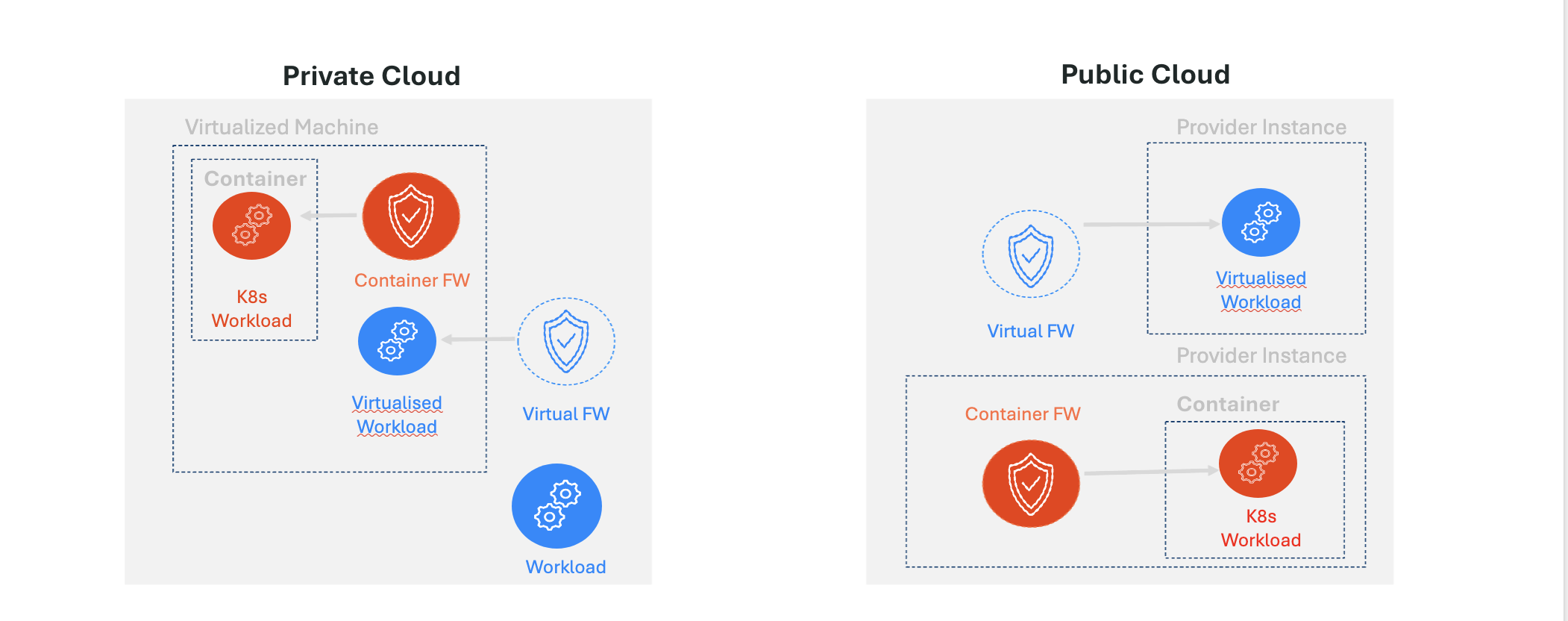
Virtual Firewalls in Private Cloud (VMware, KVM, Hyper-V, Proxmox)
In virtualized environments, your applications don’t sit behind a single perimeter; they operate across dozens, sometimes hundreds, of virtual machines.
And they’re constantly talking to each other.
This creates two distinct types of traffic:
- East-west traffic: communication between workloads inside your environment
- North-south traffic: traffic entering and leaving your network
Traditional firewalls were built for north-south traffic.
Attackers, however, thrive in east-west movement.
A Virtual Firewall operates inside the virtual environment itself, giving you visibility and control where it matters most.
With it, you can:
- Micro-segment applications at the workload level to prevent unauthorized communication
- Isolate critical systems so a breach in one area doesn’t spread
- Stop lateral movement before it escalates into a full compromise
Instead of relying on a hard perimeter, security is built inside your environment, protecting how workloads talk to each other.
Virtual Firewalls in Public Cloud (AWS, Azure, Hybrid Environments)
In the public cloud, the concept of a fixed perimeter disappears entirely.
Applications are exposed to the internet and accessible to external users. Workloads scale up and down dynamically. And environments often span multiple clouds and on-premises data centers.
Security has to keep up.
A Virtual Firewall in the cloud is deployed as a native instance within your environment, protecting:
- Internet-facing applications from external threats
- Traffic within virtual networks (like VPCs)
- Hybrid connections between cloud and on-prem environments
But the real value isn’t just protection, it’s consistency.
You get:
- Unified security policies across hybrid and multi-cloud environments
- Dynamic, scalable protection that grows with your workloads
- Centralized control without slowing down cloud agility
Because in the cloud, security can’t be static. It has to move at the speed of your infrastructure.
How a Virtual Firewall Actually Works
At its core, a Virtual Firewall delivers the same foundational capabilities as a traditional firewall but in a form factor built for modern environments.
The difference is where and how it operates.
Inside private and public clouds, a Virtual Firewall:
- Inspects traffic in real time, including east-west communications traditional tools miss
- Enforces segmentation policies between workloads, applications, and environments
- Controls access dynamically based on identity, policy, and context
- Detects and blocks threats early, before they spread internally
In cloud environments specifically, it also:
- Deploys as a scalable instance within virtual networks
- Protects distributed applications without relying on fixed infrastructure
- Adapts automatically as workloads are created, moved, or scaled
By operating within virtual and cloud environments, a Virtual Firewall delivers scalable security that protects traffic between workloads as your infrastructure grows.
Virtual Firewalls and Containerized Workloads (Kubernetes)
Containers add another layer of complexity and another set of blind spots.
In Kubernetes environments, communication happens at a much finer level:
- Between containers
- Across pods
- Dynamically, and often short-lived
Traditional security approaches and some standard virtual firewalls weren’t designed for this level of granularity.
That’s why relying on a single layer of protection isn’t enough.
To properly secure containerized environments, organizations need a layered approach:
- Virtual Firewalls to secure the infrastructure and network layer
- Kubernetes-native controls (like network policies) to manage pod-level communication
- Container security tools for runtime protection and visibility
When combined, these controls:
- Reduce attack surface across the stack
- Prevent unauthorized service-to-service communication
- Ensure consistent security from the infrastructure to the application layer
Because in containerized environments, security gaps don’t just exist at the edge, they exist everywhere workloads interact.
The Bottom Line: You Can’t Secure What You Can’t See
As infrastructure becomes more distributed across private clouds, public clouds, and Kubernetes clusters, the traditional network perimeter disappears.
And with it, so does your visibility.
Today’s attackers don’t break in and stop. They move laterally, quietly, quickly, and often undetected across the very environments most organizations struggle to monitor.
If your security strategy doesn’t account for east-west traffic, workload-level segmentation, and cloud-native scale, it’s not a matter of if there’s exposure; it’s where.
Virtual firewalls aren’t an upgrade.
They’re a requirement.
Meet SonicWall NSv Gen 8, Built for the Traffic Your Firewall Can’t See
SonicWall NSv Gen 8 is designed for exactly where traditional firewalls fall short.
It delivers:
- Deep visibility into east-west and north-south traffic
- Advanced threat protection inside virtual and cloud environments
- Consistent security across VMware, Hyper-V, KVM, Proxmox, AWS, and Azure
- Scalable performance that grows with your workloads
More importantly, it brings control back to environments where complexity and risk are increasing every day.
Because securing the edge is no longer enough.
You need to secure what’s inside.
Ready to eliminate blind spots in your cloud environment?
Explore SonicWall NSv Gen 8 or request a personalized demo today and discover how next-generation virtual firewalls can secure your cloud journey, end to end.
Share This Article

An Article By
An Article By
Lokesh Kannaiyan
Lokesh Kannaiyan

Leelin Thye
Senior Manager, Product Marketing
Leelin Thye
Senior Manager, Product Marketing

